Filters
Delegated Regulation (EU) 2022/1645
Cover Regulation to Delegated Regulation (EU) 2022/1645
EXPLANATORY MEMORANDUM
Regulation (EU) 2022/1645
1.CONTEXT OF THE DELEGATED ACT
The current European aviation safety regulatory framework contains a series of requirements which are aimed at reducing the likelihood of an accident happening.
This combination of requirements allows that even if an error, mistake and/or deficiency happens, it should not create a hazardous situation that could result in an accident or serious incident. Consequently, an accident or serious incident would only happen in the remote random event of several deficiencies happening simultaneously and, by chance, aligning themselves.
The concern is that not enough focus may have been put in properly addressing the situation where existing flaws in different areas are aligned on purpose and exploited by individuals with a malicious intent, no longer being a random event. Such a risk is constantly increasing in the civil aviation environment as the current information systems are becoming more and more interconnected.
As a consequence, it is necessary to introduce requirements for the management of information security risks which could have a potential impact on aviation safety.
In the particular case of this Delegated Act, the provisions introduced increase the robustness of the management systems and reporting processes and procedures required by Annex II ‘Essential requirements for airworthiness’ and Annex VII ‘Essential requirements for aerodromes’ to Regulation (EU) 2018/113928 for design and production organisations, and for aerodrome operators and providers of apron management services.
2.CONSULTATIONS PRIOR TO THE ADOPTION OF THE ACT
In accordance with Article 128(4) of Regulation (EU) 2018/1139, before adopting a delegated act, the Commission shall consult experts designated by each Member State in accordance with the principles laid down in the Interinstitutional Agreement of 13 April 2016 on Better Law- Making. The draft delegated act was presented to the Air Safety experts group, which includes representatives from the Member States, at its meetings on 17 February and 29 June 2022. The present delegated act is based on EASA Opinion No 03/2021 which contents had been publicly consulted through Notice of Proposed Amendment (NPA) 2019-07 ‘Management of information security risks’29 (RMT.0720), published by EASA on 27 May 2019.
3.LEGAL ELEMENTS OF THE DELEGATED ACT
Articles 19(1) and 39(1) of Regulation (EU) 2018/1139 empower the Commission to adopt delegated acts, in accordance with Article 128 of that Regulation, laying down detailed rules with regard to organisations responsible for the design and production of products, parts and non-installed equipment, and with regard to organisations responsible for the operation of aerodromes and for the provision of apron management services.
COMMISSION DELEGATED REGULATION (EU) 2022/1645
of 14 July 2022
laying down rules for the application of Regulation (EU) 2018/1139 of the European Parliament and of the Council, as regards requirements for the management of information security risks with a potential impact on aviation safety for organisations covered by Commission Regulations (EU) No 748/2012 and No 139/2014 and amending Commission Regulations (EU) No 748/2012 and No 139/2014
Regulation (EU) 2022/1645
THE EUROPEAN COMMISSION,
Having regard to the Treaty on the Functioning of the European Union,
Having regard to Regulation (EU) 2018/1139 of the European Parliament and of the Council of 4 July 2018 on common rules in the field of civil aviation and establishing a European Union Aviation Safety Agency, and amending Regulations (EC) No 2111/2005, (EC) No 1008/2008, (EU) No 996/2010, (EU) No 376/2014 and Directives 2014/30/EU and 2014/53/EU of the European Parliament and of the Council, and repealing Regulations (EC) No 552/2004 and (EC) No 216/2008 of the European Parliament and of the Council and Council Regulation (EEC) No 3922/9130, and in particular Articles 19(1) point (g) and 39(1) point (b) thereof.
Whereas:
(1)In accordance with the essential requirements set out in Annex II, point 3.1(b), to Regulation (EU) 2018/1139, design and production organisations are to implement and maintain a management system to manage safety risks.
(2)In addition, in accordance with the essential requirements set out in Annex VII, points 2.2.1 and 5.2, to Regulation (EU) 2018/1139, aerodrome operators and organisations responsible for the provision of apron management services are to implement and maintain a management system to manage safety risks.
(3)The safety risks referred to in recitals (1) and (2) may derive from different sources, including design and maintenance flaws, human performance aspects, environmental threats and information security threats. Therefore, the management systems implemented by the organisations as referred to in recitals (1) and (2), should take into account not only safety risks stemming from random events, but also safety risks deriving from information security threats where existing flaws may be exploited by individuals with a malicious intent. Those information security risks are constantly increasing in the civil aviation environment as the current information systems are becoming more and more interconnected, and increasingly becoming the target of malicious actors.
(4)The risks associated with those information systems are not limited to possible attacks to the cyberspace, but encompass also threats which may affect processes and procedures as well as the performance of human beings.
(5)A significant number of organisations already use international standards, such as ISO 27001, in order to address the security of digital information and data. These standards may not fully address all the specificities of civil aviation.
(6)Therefore, it is appropriate to set out requirements for the management of information security risks with a potential impact on aviation safety.
(7)It is essential that those requirements cover the different aviation domains and their interfaces since aviation is a highly interconnected system of systems. Therefore, they should apply to all the organisations that are already required to have a management system in accordance with the existing Union aviation safety legislation.
(8)The requirements laid down in this Regulation should be consistently applied across all aviation domains, while creating a minimal impact on the Union aviation safety legislation already applicable to those domains.
(9)The requirements laid down in this Regulation should be without prejudice to information security and cybersecurity requirements laid down in Point 1.7 of the Annex to Commission Implementing Regulation (EU) 2015/1998(31) and in Article 14 of Directive (EU) 2016/1148 of the European Parliament and of the Council(32).
(10)The definition on information security used for the purposes of this legal act should not be interpreted as divergent from the definition of security of network and information systems laid down in Directive 2016/1148.
(11)In order to avoid duplication of legal requirements, where organisations covered by this Regulation are already subject to security requirements arising from other Union acts referred to in recital (9), which are, in their effect equivalent to the provisions laid down in this Regulation, compliance with those security requirements should be considered to constitute compliance with the requirements laid down in this Regulation.
(12)Organisations covered by this Regulation that are already subject to security requirements arising from Regulation (EU) 2015/1998 should also comply with the requirements of Annex I (Part IS.D.OR.230 “Information security external reporting scheme”) to this Regulation as Regulation (EU) 2015/1998 does not contain any provisions related to external reporting of information security incidents.
(13)Regulations (EU) No 748/2012(33) and No 139/2014(34) should be amended in order to establish the link between the management systems prescribed in the regulations listed above and the information security management requirements prescribed by this Regulation.
(14)In order to provide organisations with sufficient time to ensure compliance with the new rules and procedures introduced by this Regulation, this Regulation should apply from 3 years after the date of entry into force.
(15)The requirements laid down by this Regulation are based on Opinion No 03/2021(35), issued by the Agency in accordance with Article 75(2) points (b) and (c) and Article 76(1) of Regulation (EU) 2018/1139.
(16)In accordance with Article 128(4) of Regulation (EU) 2018/1139, the Commission consulted experts designated by each Member State in accordance with the principles laid down in the Inter-institutional Agreement of 13 April 2016 on Better Law-Making36,
HAS ADOPTED THIS REGULATION:
Article 1 – Subject matter
Regulation (EU) 2022/1645
This Regulation sets out the requirements to be met by the organisations referred to in Article 2 in order to identify and manage information security risks with potential impact on aviation safety which could affect information and communication technology systems and data used for civil aviation purposes and to detect information security events and identify those which are considered information security incidents with potential impact on aviation safety and respond to, and recover from, those information security incidents.
GM1 Article 1 — Subject matter
ED Decision 2023/008/R
When taking measures under this Regulation, affected entities — irrespective of their size — are encouraged to ensure that the measures they take are proportionate to the nature and safety risk of their activities.
Article 2 – Scope
Regulation (EU) 2025/22
1.This Regulation applies to the following organisations:
(a)production organisations and design organisations subject to Subparts G and J of Section A of Annex I (Part 21) to Regulation (EU) No 748/2012, except design and production organisations that are solely involved in the design and/or production of ELA2 aircraft as defined in Article 1(2), point (j) of Regulation (EU) No 748/2012;
(b)aerodrome operators and apron management service providers subject to Annex III ‘Part Organisation Requirements (Part-ADR.OR)’ to Regulation (EU) No 139/2014.
(c)ground handling organisations subject to Commission Delegated Regulation (EU) 2025/2037 that:
(i)in order to provide the respective services, have to collect, store, analyse or otherwise process data provided by third parties; or
(ii)provide directly to aircraft operators data that will be used for operational purposes.
[point (c) applicable from 27 March 2031 — Regulation (EU) 2025/22]
2.This Regulation is without prejudice to information security and cybersecurity requirements laid down in point 1.7 of the Annex to Commission Implementing Regulation (EU) 2015/1998 and in Article 14 of Directive (EU) 2016/1148 of the European Parliament and of the Council.
Article 3 – Definitions
Regulation (EU) 2022/1645
For the purpose of this Regulation, the following definitions shall apply:
(1)‘information security’ means the preservation of confidentiality, integrity, authenticity and availability of network and information systems;
(2)‘information security event’ means an identified occurrence of a system, service or network state indicating a possible breach of the information security policy or failure of information security controls, or a previously unknown situation that can be relevant for information security;
(3)‘incident’ means any event having an adverse effect on the security of network and information systems as defined in Article 4(7) of Directive (EU) 2016/1148;
(4)‘information security risk’ means the risk to organisational civil aviation operations, assets, individuals, and other organisations due to the potential of an information security event. Information security risks are associated with the potential that threats will exploit vulnerabilities of an information asset or group of information assets;
(5)‘threat’ means a potential violation of information security which exists when there is an entity, circumstance, action or event that could cause harm;
(6)‘vulnerability’ means a flaw or weakness in an asset or a system, procedures, design, implementation, or information security measures that could be exploited and results in a breach or violation of the information security policy.
GM1 Article 3 — Definitions
ED Decision 2023/008/R
For the sake of common understanding, the following is a description of the terms used in the AMC & GM to Part-IS.D.OR of Commission Delegated Regulation (EU) 2022/1645 as well as in the AMC & GM to Part-IS.AR and Part-IS.I.OR of Commission Implementing Regulation (EU) 2023/203:
Assessment | In the context of management system performance monitoring, continuous improvement and oversight, it refers to a planned and documented activity performed by competent personnel to evaluate and analyse the achieved level of performance, effectiveness and maturity, as well as compliance in relation to the organisation’s policy and objectives. Note: An assessment focuses on required outcomes and the overall performance, looking at the organisation as a whole. The main objective of the assessment is to identify the strengths and weaknesses to drive continuous improvement. Remark: For ‘risk assessment’, please refer to the definition below. |
Attack vector (or attack path) | The path, interface, and actions by which an attacker executes an attack, as defined in EUROCAE ED-202. |
Audit | It refers to a systematic, independent, and documented process for obtaining evidence, and evaluating it objectively to determine the extent to which requirements are complied with. Note: Audits may include inspections. |
Competency | It is a combination of individual skills, practical and theoretical knowledge, attitude, training, and experience. |
Correction | It is the action to eliminate a detected non-compliance. |
Corrective action | It is the action taken to eliminate or mitigate the root cause(s) and prevent the recurrence of an existing detected non-compliance or other undesirable conditions or situations. Proper determination of the root cause(s) is crucial for defining effective corrective actions to prevent reoccurrence. |
Deficiency | It is as a deviation from compliance with or a non-fulfilment of any requirement or objectives, either from a regulatory or an organisation’s perspective, either completely or partially. |
Experience | It is the fact or state of having been affected by or gained knowledge and skills through observation, participation or doing. |
Functional chain | The concept of functional chain dictates that information security risks are shared along organisations due to their respective interfaces, such as supplier-customer relationships. Safety effects caused by information security threats primarily materialise at aircraft level, originating upstream of the aircraft. In the functional chain concept, each organisation assesses its information security risks, which it may not be able to address and hence may expose other organisations to risks. It should pass related information to the immediate partner(s) downstream for well-informed risk management purposes and to ensure that the whole chain is adequately protected, even when no organisation has full visibility or control. |
Hazard | It is a condition or an object with the potential to cause or contribute to an aircraft incident or accident. |
Information security control | It is a measure that reduces risk. |
Intentional unauthorised electronic interaction | It refers to the deliberate act of engaging in electronic activities or communications (e.g. access to, or modification of, computer systems, networks, or data) without proper authorisation or permission and with the intent to disclose sensitive information, modify data, disrupt normal operations, or deny access to legitimate users. |
Just culture | It means a culture in which front-line operators or other persons are not punished for actions, omissions or decisions taken by them that are commensurate with their experience and training, but in which gross negligence, wilful violations and destructive acts are not tolerated, as defined in Article 2 of Regulation (EU) No 376/201438. |
Knowledge | Content of information needed to perform adequately in the job at an acceptable level, usually obtained through formal education and on-the-job experience. This knowledge is necessary for job performance but is not sufficient on its own. |
Management (activity) | In the general organisational context, it refers to the activities aimed at directing, controlling, and continually improving the organisation within appropriate structures. In the context of Commission Delegated Regulation (EU) 2022/1645 and Commission Implementing Regulation (EU) 2023/203 it means, more specifically, the supervision and making of decisions necessary to achieve the organisation’s safety and information security objectives. |
Management system | It refers to a set of interrelated or interacting system elements to establish policies, objectives and processes to achieve those objectives, where the system elements include the organisational structure, roles and responsibilities, planning and operations. |
Risk assessment | It is an evaluation that is based on engineering and operational judgement and/or analysis methods in order to establish whether the achieved or perceived risk is acceptable. |
Risk register | It refers to a physical or digital means of documentation used as a risk management tool that acts as a repository for all identified risks and contains additional information about each risk, such as the nature of the risk, mitigation measures, ownership, status, etc. |
Safety | It refers to the state in which risks associated with aviation activities, related to, or in direct support of the operation of aircraft, are reduced and controlled to an acceptable level, as defined in ICAO Annex 19. |
Safety risk | It refers to the predicted likelihood and severity of the consequences or outcomes of a hazard. Note: The term ‘likelihood’ is used instead of the term ‘probability’ to reflect a subjective analysis of the possibility of occurrence rather than a purely statistical assessment. |
Article 4 – Requirements arising from other Union legislation
Regulation (EU) 2022/1645
1.Where an organisation referred to in Article 2 complies with security requirements laid down in Article 14 of Directive (EU) 2016/1148 of the European Parliament and of the Council that are equivalent to the requirements laid down in this Regulation, compliance with those security requirements shall be considered to constitute compliance with the requirements laid down in this Regulation.
2.Where an organisation referred to in Article 2 is an operator or an entity referred to in the national civil aviation security programmes of Member States laid down in accordance with Article 10 of Regulation (EC) No 300/2008 of the European Parliament and of the Council39, the cybersecurity requirements contained in Point 1.7 of the Annex to Implementing Regulation (EU) 2015/1998 are considered to be equivalent to the requirements laid down in this Regulation, except as regards point IS.D.OR.230 of the Annex to this Regulation that shall be complied with.
3.The Commission, after consulting EASA and the Cooperation Group referred to in Article 11 of Directive (EU) 2016/1148, may issue guidelines for the assessment of the equivalence of requirements laid down in this Regulation and Directive (EU) 2016/1148.
GM1 Article 4(1) Requirements arising from other Union legislation
ED Decision 2025/013/R
Pursuant to Article 44 of Directive (EU) 2022/2555 (the NIS 2 Directive), the previous Directive
(EU) 2016/1148 (the NIS Directive) was repealed with effect from 18 October 2024. In accordance with the NIS2 Directive, references to the repealed Directive shall be construed as references to Directive (EU) 2022/2555 and shall be read in accordance with the correlation table set out in its Annex III.
In accordance with this table, references to Article 14 of Directive (EU) 2016/1148 shall be now read as references to Article 21 and Article 23 of Directive (EU) 2022/2555. For an exact correlation, please refer to Annex III to Directive (EU) 2022/2555.
To ensure legal certainty, the equivalence of any requirements should be assessed by the competent authority against the requirements of the national legislation when Directive (EU) 2022/2555 is transposed.
When utilising this equivalence, organisations should consider the following:
—The equivalence between Regulation (EU) 2022/1645 and Directive (EU) 2022/2555 requirements as assessed by the competent authority.
—Possible differences in the perimeter of applicability of the rules, in particular as regards the elements that are within the scope under the two different frameworks.
The competent authority will decide whether or not the measures implemented by the organisation under the NIS framework can be considered sufficient for satisfying requirements of similar nature under this rule.
GM1 Article 4(2) Requirements arising from other Union legislation
ED Decision 2025/013/R
Notwithstanding the equivalence between the requirements in Regulation (EU) 2022/1645 and the cybersecurity requirements contained in point 1.7 of the Annex to Regulation (EU) 2015/1998, in order to ensure effective management of safety consequences by leveraging the requirements of Regulation (EU) 2015/1998, organisations need to consider the differences in the scope of the rules in terms of which elements are covered under the two different regulatory frameworks.
Taking the example of an airport operator, elements such as body scanners, X-ray machines and anti-RPAS systems fall under the scope of the requirements of point 1.7 of the Annex to Regulation
(EU) 2015/1998. Elements such as runway lighting control systems and safety training databases fall under the scope of aviation safety rules. On the other hand, the protection of information and the verification of trustworthiness and identity can be considered element that overlap between the two frameworks.
Consequently, an organisation that has developed a system in accordance with point 1.7 of the Annex to Regulation (EU) 2015/1998 can use it to address safety issues by extending the scope of the system, where necessary, to ensure that all safety-related elements are included. Moreover, compliance with point IS.D.OR.230 has to be ensured.
Article 5 – Competent authority
Regulation (EU) 2025/22
1.The authority responsible for certifying and overseeing compliance with this Regulation shall be:
(a)with regard to organisations referred to in Article 2, point (a), the competent authority designated in accordance with Annex I (Part 21) to Regulation (EU) No 748/2012;
(b)with regard to organisations referred to in Article 2, point (b), the competent authority designated in accordance with Annex III (Part-ADR.OR) to Regulation (EU) No 139/2014.
(c)with regard to organisations referred to in Article 2 point (c), the competent authority designated in accordance with the Annex (Part-ARGH) to Commission Implementing Regulation (EU) 2025/2340.
[point (c) applicable from 27 March 2031 — Regulation (EU) 2025/22]
2.Member States, may for the purposes of this Regulation, designate an independent and autonomous entity to fulfil the assigned role and responsibilities of the competent authorities referred to in paragraph 1. In that case, coordination measures shall be established between that entity and the competent authorities, as referred to in paragraph 1, to ensure effective oversight of all the requirements to be met by the organisation.
GM1 Article 5(2) Competent authority
ED Decision 2025/013/R
The applicability of Annex I (Part-IS.AR) to Implementing Regulation (EU) 2023/203 to competent authorities is specified in its Article 4(2) and called for under the authority requirements for a management system in the implementing or delegated act for each domain. Therefore, the Part-IS.AR requirements apply to the competent authority under Article 5(1) irrespective of the allocation of roles and responsibilities to an independent and autonomous entity designated by the State under Article 5(2).
At the same time, this independent and autonomous entity designated by the State is not subject to the Part-IS.AR requirements; this entity has only to fulfil the responsibilities for certifying and overseeing organisations’ compliance with Implementing Regulation (EU) 2023/203.
This entity typically holds the role of a national information security body within the Member State and is normally subject to similar requirements to those existing in Part-IS.AR.
Article 6 – Amendment to Regulation (EU) No 748/2012
Regulation (EU) 2022/1645
For the consolidated version of Annex I (Part 21) to Regulation (EU) No 748/2012, please refer to the Easy Access Rules for Airworthiness and Environmental Certification (Regulation (EU) No 748/2012).
Article 7 – Amendment to Regulation (EU) No 139/2014
Regulation (EU) 2022/1645
For the consolidated version of Annex III (Part-ADR.OR) to Regulation (EU) No 139/201441, please refer to the Easy Access Rules for Aerodromes (Regulation (EU) No 139/2014).
Article 8
Regulation (EU) 2022/1645
This Regulation shall enter into force on the twentieth day following that of its publication in the Official Journal of the European Union.
It shall apply from 16 October 2025.
Regulation (EU) 2022/1645
This Regulation shall be binding in its entirety and directly applicable in all Member States.
Done at Brussels, 14 July 2022.
For the Commission
The President
Ursula VON DER LEYEN
ANNEX — INFORMATION SECURITY — ORGANISATION REQUIREMENTS [PART-IS.D.OR]
IS.D.OR.100 Scope
Regulation (EU) 2022/1645
This Part establishes the requirements to be met by the organisations referred to in Article 2 of this Regulation.
IS.D.OR.200 Information security management system (ISMS)
Regulation (EU) 2025/22
(a)In order to achieve the objectives set out in Article 1, the organisation shall set up, implement and maintain an information security management system (ISMS) which ensures that the organisation:
(1)establishes a policy on information security setting out the overall principles of the organisation with regard to the potential impact of information security risks on aviation safety;
(2)identifies and reviews information security risks in accordance with point IS.D.OR.205;
(3)defines and implements information security risk treatment measures in accordance with point IS.D.OR.210;
(4)implements an information security internal reporting scheme in accordance with point IS.D.OR.215;
(5)defines and implements, in accordance with point IS.D.OR.220, the measures required to detect information security events, identifies those events which are considered incidents with a potential impact on aviation safety, and responds to, and recovers from, those information security incidents;
(6)implements the measures that have been notified by the competent authority as an immediate reaction to an information security incident or vulnerability with an impact on aviation safety;
(7)takes appropriate action, in accordance with point IS.D.OR.225, to address findings notified by the competent authority;
(8)implements an external reporting scheme in accordance with point IS.D.OR.230 in order to enable the competent authority to take appropriate actions;
(9)complies with the requirements contained in point IS.D.OR.235 when contracting any part of the activities referred to in point IS.D.OR.200 to other organisations;
(10)complies with the personnel requirements laid down in point IS.D.OR.240;
(11)complies with the record-keeping requirements laid down in point IS.D.OR.245;
(12)monitors compliance of the organisation with the requirements of this Regulation and provides feedback on findings to the accountable manager or, in the case of design organisations, to the head of the design organisation, in order to ensure effective implementation of corrective actions;
(13)protects, without prejudice to applicable incident reporting requirements, the confidentiality of any information that the organisation may have received from other organisations, according to its level of sensitivity.
(b)In order to continuously meet the requirements referred to in Article 1, the organisation shall implement a continuous improvement process in accordance with point IS.D.OR.260.
(c)The organisation shall document, in accordance with point IS.D.OR.250, all key processes, procedures, roles and responsibilities required to comply with point IS.D.OR.200(a) and establish a process for amending that documentation. Changes to those processes, procedures, roles and responsibilities shall be managed in accordance with point IS.D.OR.255.
(d)The processes, procedures, roles and responsibilities established by the organisation in order to comply with point IS.D.OR.200(a) shall correspond to the nature and complexity of its activities, based on an assessment of the information security risks inherent to those activities, and may be integrated within other existing management systems already implemented by the organisation.
(e)Without prejudice to the obligation to comply with the reporting requirements contained in Regulation (EU) No 376/201442 and the requirements of point IS.D.OR.200(a)(13), the organisation may be granted approval by the competent authority not to implement the requirements referred to in points (a) to (d) ) and the related requirements contained in points IS.D.OR.205 through IS.D.OR.260, if it demonstrates to the satisfaction of that authority that its activities, facilities and resources, as well as the services it operates, provides, receives and maintains, do not pose any information security risks with a potential impact on aviation safety neither to itself nor to other organisations. The approval shall be based on a documented information security risk assessment carried out by the organisation or a third party in accordance with point IS.D.OR.205 and reviewed and approved by its competent authority.
The continued validity of that approval will be reviewed by the competent authority following the applicable oversight audit cycle and whenever changes are implemented in the scope of work of the organisation.
GM1 IS.D.OR.200 Information security management system (ISMS)
ED Decision 2025/014/R
An information security management system (ISMS) is a systematic approach to establish, implement, operate, monitor, review, maintain and continuously improve the state of information security of an organisation. Its objective is to protect the information assets, such that the operational and safety objectives of an organisation can be reached in a risk-aware, effective and efficient manner.
Generally speaking, an ISMS establishes an information security risk management process, based upon the results of information security impact analyses, which basically determine its scope. If information security breaches may cause or contribute to aviation safety consequences, information security requirements need to limit the impact or influence of information security breaches on levels of aviation safety, which are deemed acceptable. Hence, all roles, processes, or information systems, which may cause or contribute to aviation safety consequences, are within the scope of Regulation (EU) 2022/1645. The ISMS provides for means to decide on needed information security controls for all architectural layers (governance, business, application, technology, data) and domains (organisational, human, physical, technical). It further allows to manage the selection, implementation, and operation of information security controls. Finally, it allows to manage the governance, risk management and compliance (GRC) within the ISMS scope.
The overall risk assessment considers safety consequences influenced by information security risks. These may emerge as threats, hazards, escalation factors that weaken barriers, or direct triggers of existing hazards. When conducting this assessment, both aspects, information security and safety need to be coordinated throughout the process. This ensures mutual understanding of the objectives and the implementation of preventive measures against all types of threats or weaknesses, as well as mitigating measures.
The risk management process is thus based on aviation safety risk assessments and derived information security risk acceptance levels, which are designed to effectively treat and manage information security risks with a potential impact on aviation safety caused by threats exploiting vulnerabilities of information assets in aeronautical systems.
Interacting bow-ties is one possible way that allows for a higher level and non-exhaustive illustration of how different disciplines of risk assessment may need to collaborate to establish a common risk perspective. The below Figure 1 from ICAO Doc 10204 ‘Manual on Aviation Information Security’ illustrates these interactions.
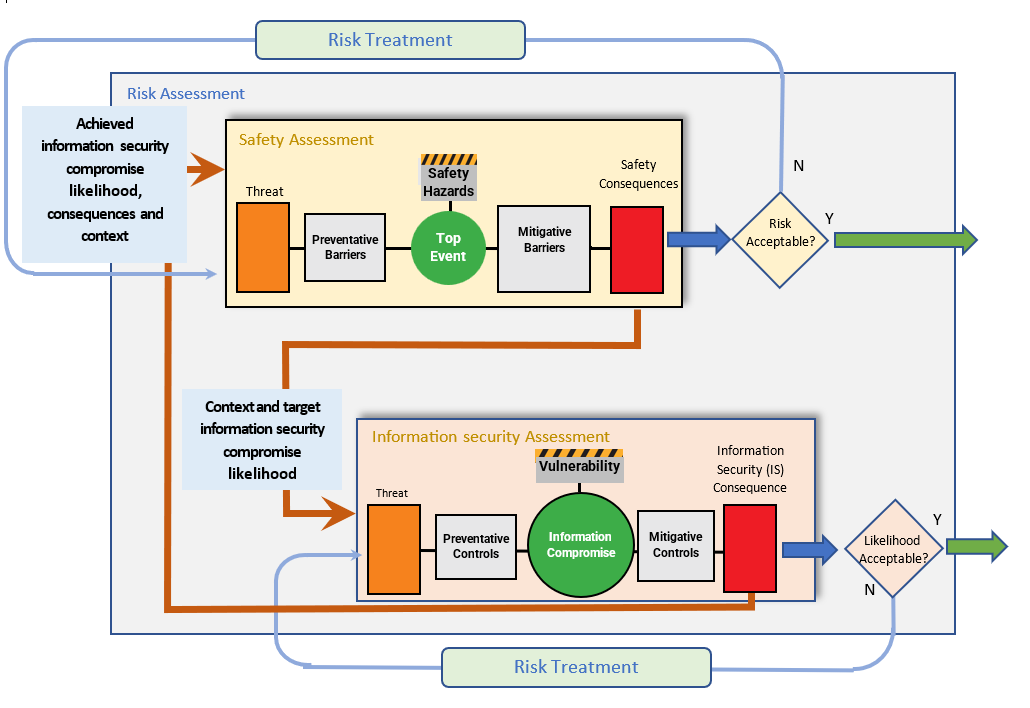
Figure 1: Bow-tie representation of management of aviation safety risks posed by information security threats
In the drawing, the term ‘context’ in the communication between the safety assessment process (SAP) and the information security assessment process (ISAP) carries slightly different notions, which need to be understood and distinguished.
In order to satisfy the safety requirements, the SAP will provide context information such as:
—the architecture of the systems and the functional descriptions of the elements within the scope, including those related to the barriers. Systems should be understood as the dynamic interaction between people, processes, and products or services;
—all identified relevant safety hazards;
—the top events and their relations (e.g. triggers) to those hazards.
In addition to context information, it provides the target likelihood of the related information security successful compromise. This target likelihood is commensurate with the safety objectives related to the severity of the safety consequence. However, it needs to be complemented to include information about the acceptable level of uncertainty, in order to be able to rely adequately on the results of the ISAP.
In turn, the ISAP will return context information such as:
—modification to the architecture of the systems and functional descriptions of the elements modified or added, whether those were safety barriers or other items;
—additional threats;
—potentially additional safety hazards;
—additional direct triggers of hazards;
—additional escalating factors affecting barriers.
In addition to context information, it provides the achieved likelihood of an information security successful compromise. While this likelihood is consistent with the safety objectives set by the SAP, the achieved level of uncertainty also needs to be considered.
The interaction between SAP and ISAP is iterative and continues until the safety risk is acceptable, i.e. the target likelihood of the related information security successful compromise has been achieved. The interaction can start from safety consequences identified through the SAP that fall within the scope of the ISMS risk analysis, or from existing information security assessments.
ISMS implementation and maintenance
An ISMS, as defined in this Regulation, employs the perspectives of governance, risk and compliance, and an approach that combines the safety risk and performance dimensions to determine the information security controls that are appropriate and compliant with the specific context and can effectively provide the level of protection required to achieve the aviation safety objectives by:
—Governance perspective refers to providing management direction and leadership aimed to achieve the entity’s own overarching objectives:
—leadership and commitment of the senior management defining and ensuring the close involvement of the management and a ‘top-down’ ISMS implementation
—information security and safety objectives aligned and consistent with the entity’s business objectives and monitored by, e.g., management reviews
—information security policies stating the principles and objectives to be achieved
—roles, responsibilities, competencies and resources required for an effective ISMS
—effective, target-group-oriented communication to internal and external stakeholders
—Risk perspective refers to a key aspect of an ISMS in an aviation safety context according to this Regulation and serves as a basis for transparent decision-making and prioritisation of controls and risk treatment options. It further refers to the assessment, treatment and monitoring of information security risks in support of the management of aviation safety risks for the key processes and information assets upon which they depend. This includes protection requirements, risk exposure, attitude towards risks and risk acceptance criteria, methods and industry standards.
—Compliance perspective refers to the compliance with regulatory, legal and contractual requirements. This includes:
—this Regulation,
—the entity’s own policies and standards and may further include international or industry standards adopted by the entity from ISO, EUROCAE, etc.
This perspective comprises the definition, implementation and maintenance of the required information security provisions whose effectiveness and compliance should be regularly monitored and assured by, e.g. (internal) audits.
Based on these perspectives we may identify the following processes or subject areas that have been shown to be relevant for the establishment of an effective ISMS. These ISMS processes and subject areas can be summarised as follows:
(a)context establishment defining the scope, interfaces, dependencies and requirements of interested parties;
(b)leadership and commitment of the senior management;
(c)information security and safety objectives;
(d)information security policies;
(e)roles, responsibilities, competencies and resources required for an effective ISMS;
(f)communication to internal and external stakeholders to achieve a sufficient level of information security awareness and training of all involved parties;
(g)information security risk management including risk assessment and treatment;
(h)information security incident management establishing processes for the handling of information security incidents and vulnerabilities;
(i)performance & effectiveness monitoring, measurement and evaluation;
(j)internal audits and management reviews;
(k)corrections and corrective actions;
(l)continuous improvement;
(m)relationship with suppliers;
(n)documentation, record-keeping, and evidence collection.
Additional critical success factors for the implementation and operation of an ISMS include the following:
—The ISMS should be integrated with the entity’s processes and overall management structure or even — at least partially, with safeguards for their respective integrity, and as reasonably applicable — with an overarching management system comprising information security, aviation safety and quality management.
—Information security has to be considered at an early stage in the overall design of processes and procedures, of systems and of information security controls, to be seamlessly integrated, for maximum effectiveness, minimal functional interference and optimised cost. None of these benefits can be achieved by integrating it on later.
—The risk management process determines appropriate characteristics of preventive controls to reach and maintain acceptable risk levels.
—The incident management process ensures that the organisation detects, reacts and responds to information security incidents in a timely manner. This is achieved by defining responsibilities, procedures, scenarios and response plans in advance to ensure a coordinated, targeted and efficient response.
—Continuous monitoring and reassessment are undertaken and improvements are made in response.
The above-mentioned core components are related to the requirements in this Regulation, for which Figure 2 provides a high-level depiction of the aspects that are more prominent in the implementation phase and those that characterise the operational phase, as well as the review and possible improvement, if the functions do not perform as planned
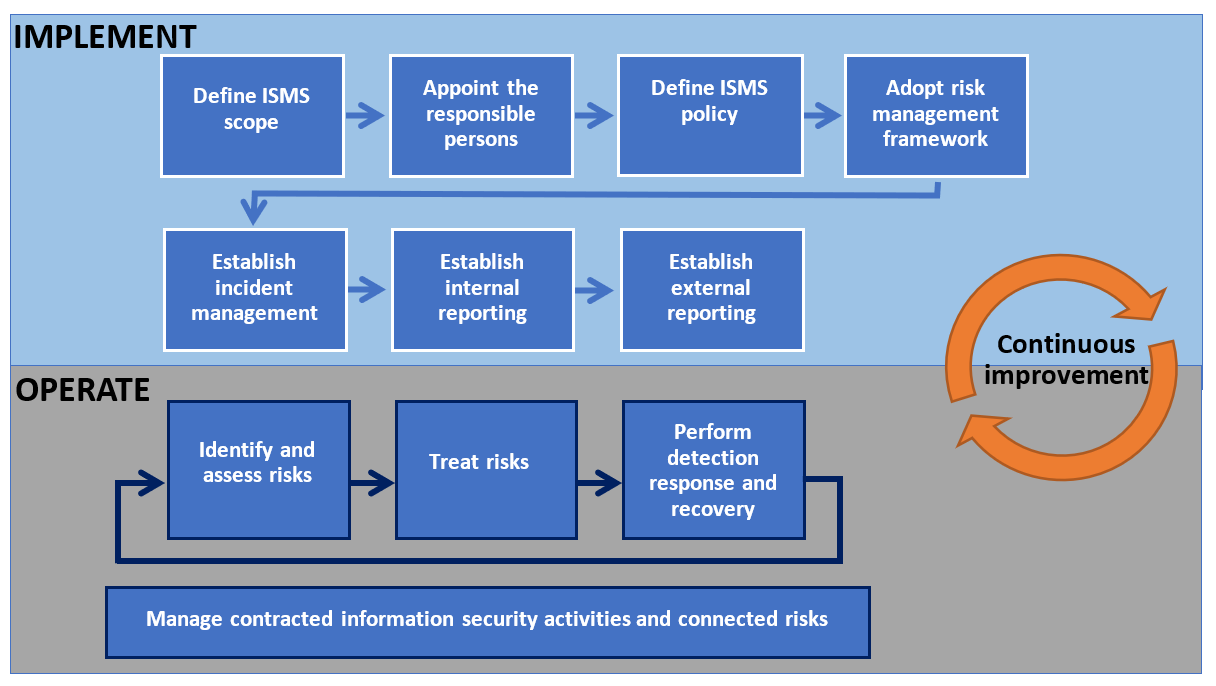
Figure 2: Representation of the Part-IS requirements from an ISMS’s life cycle perspective
Plan-Do-Check-Act approach
The Plan-Do-Check-Act (PDCA) refers to a process approach that is often used to establish, implement, operate, monitor, review and improve management systems. Figure 3 depicts the PDCA applied to an ISMS.
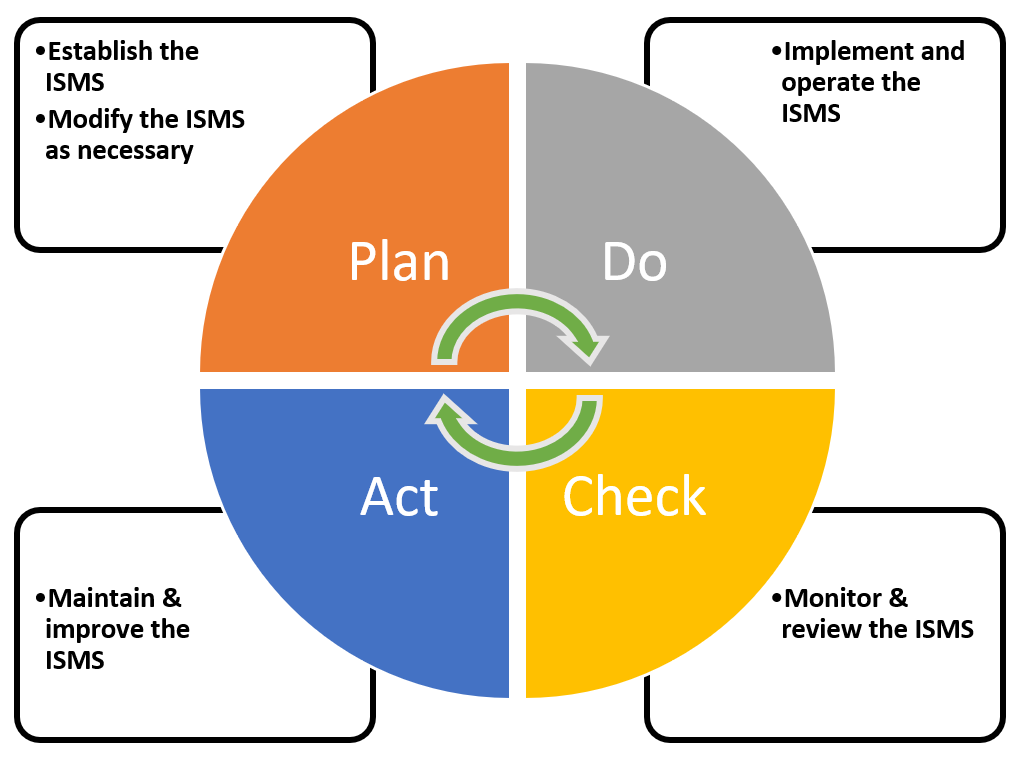
Figure 3: Plan-Do-Check-Act approach applied to an ISMS
Benefits of an ISMS
The benefits of a management system operating in a dynamic, uncertain or unpredictable risk environment are realised in the long term only when the organisation improves existing controls, processes and solutions based on the assessments of risks, performance and maturity as well as on the learnings from incidents, audits, non-conformities and their root causes. A successful adoption and deployment of an ISMS allows an entity to:
—achieve greater assurance to the management and interested parties that its information assets are adequately protected against threats on a continual basis;
—increase its trustworthiness and credibility providing confidence to interested parties that information security risks with an impact on aviation safety are adequately managed;
—increase the resilience of the entity’s key processes against unauthorised electronic interactions and maintains the entity’s ability to decide and act;
—support the timely detection of control gaps, vulnerabilities or deficiencies aimed to prevent information security incidents or at least to minimise their impact;
—detect and timely react to changes in the entity’s environment including system architecture and threat landscape or the adoption of new technologies;
—provide a foundation for effective and efficient implementation of a comprehensive information security strategy in times of digital transformation, increasing interconnectivity of systems, emerging information security threats and new technologies.
Relation to ISO/IEC 27001
The international standard ISO/IEC 27001 is a widely adopted standard for ISMS which specifies generic requirements for establishing, implementing, maintaining and continually improving an ISMS. It also includes requirements for the assessment and treatment of information security risks. The requirements are applicable to all entities, regardless of type, size or nature. The conformity of an ISMS with the ISO/IEC 27001 standard can be certified by an accredited certification body. ISO/IEC 27001 is compatible with other management system standards (quality, safety, etc.) that have also adopted the structure and terms defined in Annex SL to ISO/IEC Directives, Part 1, Consolidated ISO Supplement. This compatibility allows an entity to operate a single management system that meets the requirements of multiple management system standards.
ISO/IEC 27001 allows entities to define their own scope of audit and their own organisational risk appetite. This, in turn, leads to information security requirements that provide the ISMS with criteria for the acceptability of information security risks in line with the entity’srisk appetite (see Figure4).
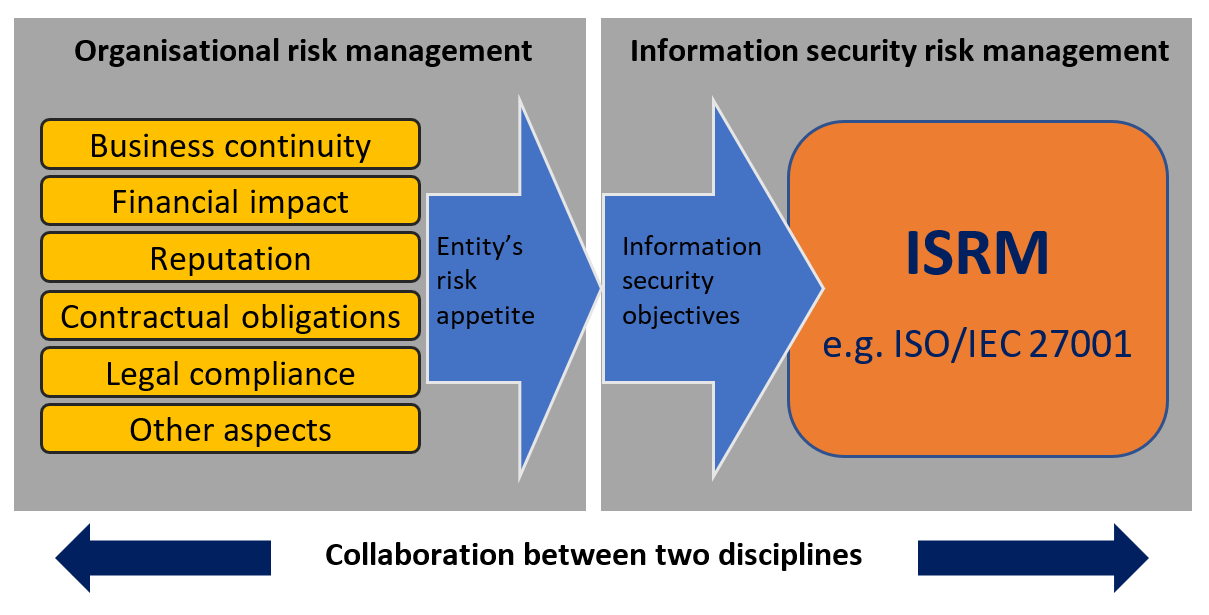
Figure 4: Relation between the entity’s risk appetite and the information security objectives
The requirements for an ISMS specified by this Regulation are in most parts consistent and aligned with ISO/IEC 27001; however, this Regulation introduces provisions specific to the context of aviation safety. If an ISO/IEC 27001-based ISMS is already operated by an entity for a different scope and context, it can be adapted and extended to the scope and context of this Regulation in a straightforward manner based on an analysis of the scope and the gaps. In order to take credit from ISO/IEC 27001 certifications to achieve compliance with Part-IS, aviation safety needs to be included in the organisational risk management, with the relevant risk acceptance level determined by the applicable regulation (see Figure 5). Therefore, careful determination of the scope of the ISMS related to aviation safety risks is needed, as it might differ from the one related to the other organisational risks. To allow demonstration of compliance with Regulation (EU) 2022/1645, careful delineation between aspects of the ISMS related to aviation safety risks and other organisational risks may be required. This could have an influence upon the decision to integrate ISMSs.
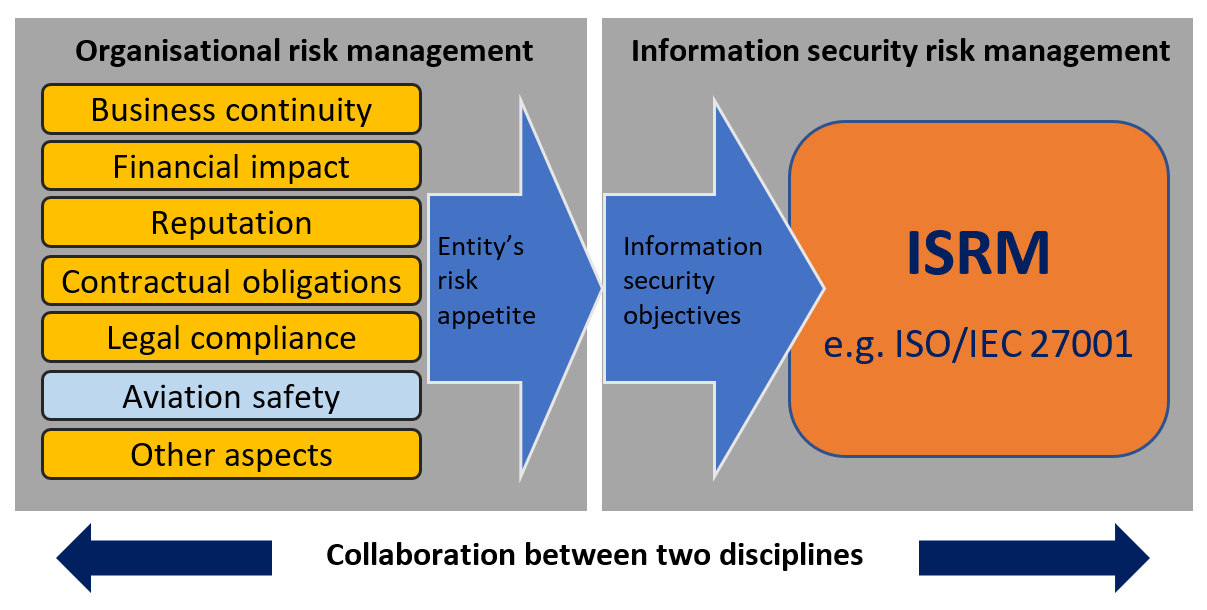
Figure 5: Introduction of aviation safety aspects in the entity’s risk appetite
PART-IS versus ISO/IEC 27001 cross reference table
For a mapping between the Part-IS provisions and the clauses and associated controls in ISO/IEC 27001:2022, refer to Appendix IV.
AMC1 IS.D.OR.200(a)(1) Information security management system (ISMS)
ED Decision 2023/009/R
The organisation should define and document the scope of the ISMS, by determining activities, processes, supporting systems, and identifying those which may have an impact on aviation safety.
The information security policy should be endorsed by the accountable manager or, in the case of design organisations, by the head of the design organisation, and reviewed at planned intervals or if significant changes occur. Moreover, the policy should cover at least the following aspects with a potential impact on aviation safety by:
(a)committing to comply with applicable legislation, consider relevant standards and best practices;
(b)setting objectives and performance measures for managing information security;
(c)defining general principles, activities, processes for the organisation to appropriately secure information and communication technology systems and data;
(d)committing to apply ISMS requirements into the processes of the organisation;
(e)committing to continually improve towards higher levels of information security process maturity as per IS.D.OR.260;
(f)committing to satisfy applicable requirements regarding information security and its proactive and systematic management and to the provision of appropriate resources for its implementation and operation;
(g)assigning information security as one of the essential responsibilities for all managers;
(h)committing to promote the information security policy through training or awareness sessions within the organisation to all personnel on a regular basis or upon modifications;
(i)encouraging the implementation of a ‘Just-(Culture’ and the reporting of vulnerabilities, suspicious/anomalous events and/or information security incidents;
(j)committing to communicate the information security policy to all relevant parties, as appropriate.
Note: A significant change is a notable alteration or modification that has a meaningful impact on the organisation’s operations, such as a structural change within the organisation due to reorganisations, a change in the business processes (e.g. working from home, use of personal devices), a technological evolution (e.g. distributed computing resources, artificial intelligence/machine learning) or an evolution in the threat landscape.
GM1 IS.D.OR.200(a)(1) Information security management system (ISMS)
ED Decision 2023/009/R
INFORMATION SECURITY POLICY AND OBJECTIVES
The information security policy should suit to the organisation’s purpose and direct its own information security activities. Such policy should contain the needs for information security in the organisation’s context, a high-level statement of direction and intent of the information security activities, the principles and most important strategic and tactical objectives to be achieved by the ISMS, as well as the general information security objectives or a specification of a framework (who, how) for setting information security objectives. The information security policy should also contain a description of the established ISMS including roles, responsibilities and references to topic-specific policies and standards.
The information security objectives should be:
—consistent and aligned with the information security policy and consider the applicable information security requirements, derived from the overarching organisation’s objectives, and the results from the risk assessment and treatment (which, in turn, supports the implementation of the organisation’s strategic goals and information security policy);
—regularly reviewed to ensure that they are up to date and still appropriate;
—measurable if practicable (to be able to determine whether the objective has been met), aimed to be SMART (specific, measurable, attainable, realistic, timely) and aligned with all affected responsible persons.
When defining information security objectives, e.g., based on the overarching organisation’s objectives, the information security requirements or the results of risk assessments, it should be determined how these objectives will be achieved. The degree to which IS objectives are achieved must be measurable. If possible, it should be measured by key performance indicators (KPIs) which have been defined in advance (refer to resources such as COBIT 5 for Information Security). It is recommended to start with the definition of a limited number of information security objectives which are relevant for the entity, more of a long-term nature and measurable with a reasonable effort relative to the delivered benefits.
AMC1 IS.D.OR.200(a)(12) Information security management system (ISMS)
ED Decision 2023/009/R
COMPLIANCE MONITORING
When establishing compliance with the provisions under points IS.D.OR.200(a)(12) the organisation should implement a function to periodically monitor compliance of the management system with the relevant requirements and adequacy of the procedures including the establishment of an internal audit process and an information security risk management process. When the organisation has already established a compliance monitoring function under the implementing regulation for its domain, such function should include the monitoring of the management system with the relevant requirements within the scope of its activities. Compliance monitoring should include a feedback mechanism of audit findings to the accountable manager or, in the case of design organisations, to the head of the design organisation, or delegated persons to ensure implementation of corrective actions as necessary.
GM1 IS.D.OR.200(a)(12) Information security management system (ISMS)
ED Decision 2023/009/R
COMPLIANCE MONITORING
For the purpose of compliance monitoring, internal audits should be conducted at planned intervals to provide assurance on the status of the ISMS to the management and to provide information on the following:
—conformity of the ISMS to the requirements of this Regulation and the organisation’s own requirements either stated in the information security policy, procedures and contracts or derived from information security objectives or outcomes of the risk treatment process;
—effective implementation and maintenance of the ISMS.
Internal audits should follow an independent approach and a decision-making process based on evidences. Moreover, when setting up an audit programme the importance of the processes concerned, and definitions of the audit criteria and scopes should be considered. Documented information should be retained evidencing the audit results, their reporting to the relevant management and the audit programme.
AMC1 IS.D.OR.200(a)(13) Information security management system (ISMS)
ED Decision 2023/009/R
When establishing compliance with the provisions under points IS.D.OR.200(a)(13), the organisation should implement and maintain information security controls that are sufficiently robust and effective to protect information and ensure the need-to-know principle (i.e. limiting access to information to only those who need it to perform their duties). It should protect the source of information in accordance with the relevant provisions established in Regulation (EU) 2018/1139. It should also comply with Regulation (EU) No 376/2014.
AMC1 IS.D.OR.200(c) Information security management system (ISMS)
ED Decision 2023/009/R
When establishing compliance with the provisions under point IS.D.OR.200(c), the organisation should:
(a)provide an outline of the structure of the specific information security personnel (internal and external), including their roles and responsibilities. This outline of the structure will be used to manage and maintain the elements included within the scope of the ISMS and will be approved by the accountable manager or, in the case of design organisations, by the head of the design organisation. The organisation should review the outline of the structure at planned intervals or if significant changes occur (see the Note in AMC1 IS.D.OR.200(a)(1));
(b)identify and categorise all relevant contracted organisations used to implement the ISMS. The organisation should define and document procedures for the management of interfaces and coordination between the organisation and other organisations, including contracted organisations;
(c)identify and define all key processes and procedures, and internal and external reporting schemes that will be used to maintain compliance with the objectives of this Regulation over the life cycle of the ISMS. The organisation may adjust existing processes or procedures for compliance;
(d)identify and document any other information that will be used to maintain compliance with the objectives of this Regulation;
(e)when creating and updating documented information, ensure appropriate identification and description (e.g. a title, date, author, or reference number) as well as a review and an approval for suitability and adequacy;
(f)control the documented information required by the ISMS to ensure that it is:
(1)available and suitable for use, where and when it is needed;
(2)adequately protected (e.g. from loss of confidentiality, improper use, or loss of integrity).
GM1 IS.D.OR.200(c) Information security management system (ISMS)
ED Decision 2023/009/R
The amount of information that should be documented to maintain compliance with the objectives of this Regulation may vary between organisations due to various factors, such as size and complexity, or the need for harmonisation with other management processes already in place. As general guidance, taking into account the documents required to comply with point IS.D.OR.200(a), the record-keeping requirements referred to in IS.D.OR.245 and the information security management manual requirements referred to in IS.D.OR.250, the following is a non-exhaustive list of information that should be documented:
(a)information security policy that should include the organisation’s information security objectives — see IS.D.OR.200(a)(1);
(b)responsibilities and accountabilities for roles relevant to information security — see IS.D.OR.250(a)(2), (3), (6) and (7) and the personnel requirements referred to in points IS.D.OR.240(a), (b), (c), (d) and (f) and the related AMC and GM;
(c)scope of the ISMS and the interfaces with, and dependencies on, other parties — see IS.D.OR.200(a)(2) and the information security requirements referred to in points IS.D.OR.205(a) and (b);
(d)information security risk management process — see the information security requirements referred to in points IS.D.OR.205 and IS.D.OR.210;
(e)archive of the risks identified in the information security risk assessment along with the associated risk treatment measures (often referred to as ‘risk register’ or ‘risk ledger’) — see IS.D.OR.245;
(f)evidence of the competencies necessary for the personnel performing the activities required under this Regulation — see IS.D.OR.240(g) and the related AMC and GM;
(g)evidence of the current competencies of the personnel performing the activities required under this Regulation — see IS.D.OR.245(b)(1);
(h)(key) performance indicators derived from evidence of the monitoring and measurement of the ISMS processes.
GM1 IS.D.OR.200(d) Information security management system (ISMS)
ED Decision 2025/014/R
PROPORTIONALITY IN ISMS IMPLEMENTATION
When implementing the processes and procedures, as well as establishing the roles and responsibilities required under point IS.D.OR.200(d), the organisation should primarily consider the risks that it may be posing to other organisations, as well as its own risk exposure. Other aspects that may be relevant include the organisation’s needs and objectives, information security requirements, its own processes and the size, complexity and structure of the organisation, all of which may change over time.
As a general guide, the following aspects of the degree of safety relevance and organisational complexity could be taken into account when defining the ISMS. Each of these influences the implementation of the ISMS in certain areas:
(a)The organisation’s position in the functional chain and the number and degree of safety relevance of the interfacing organisations/stakeholders.
(b)The complexity of the organisational structure and hierarchies (e.g. number of staff, departments, hierarchical layers, external location, subsidiaries, etc.)
(c)The complexity of the information and communication technology systems and data used by the organisation and their connection to external parties.
More details on the influence on the proportionate implementation of Part-IS for each aspect of safety relevance and organisational complexity are provided in Appendix V.
SUPPORTED IMPLEMENTATION OF THE ISMS
In the context of Part-IS, all organisations initiate the implementation of an ISMS with determining its scope, which in turn is based upon at least an assessment of aviation safety impacts for which information security incidents are a cause or a contributing factor. Organisations, irrespective of their size, may not have yet sufficient knowledge about their information security risks, and may consider seeking support by a service provider that can also provide additional personnel and expertise during this implementation phase of the ISMS. The same may apply to later phases of the ISMS implementation, and to this end organisations may want to consider the provision of IS.D.OR.235 and related AMC. Outsourcing specific ISMS functions, such as information security monitoring or incident response to service providers, may help ensure that the organisation has access to experienced personnel and expertise. Similarly, organisations may want to be supported by a service provider in performing risk assessments.
Regarding the establishment of the appropriate personnel to implement and comply with the provisions of this Regulation, organisations should always refer to AMC1 IS.D.OR.240(f) and GM1 IS.D.OR.240(f), by considering that multiple responsibilities may be assigned to one person, while always ensuring the independence of the compliance monitoring.
As an introduction to the nature of information security risks and their management, organisations may use, as initial guidance, the NIST Interagency Report (NISTIR 7621 Rev.1) ‘Small Business Information Security: The Fundamentals’.
INTEGRATION OF ISMS UNDER THIS REGULATION WITH EXISTING MANAGEMENT SYSTEMS
An organisation may take advantage of existing management systems when implementing an ISMS by integrating it with those existing systems.
By integrating the ISMS with existing management systems, the organisation may reduce the effort and costs required to implement and maintain the ISMS, while also ensuring consistency and alignment with the organisation’s overall management approach. Below is a non-exhaustive list of potential synergies that can be exploited when integrating the ISMS with an existing management system:
—Leverage existing policies and procedures: an organisation may use its existing policies and procedures as a foundation for its ISMS. This may help to ensure consistency and minimise the need for additional documentation.
—Align ISMS with other management systems: an organisation may align the ISMS with other management systems, such as safety management systems (SMS), to ensure that the ISMS is consistent with the organisation’s overall management approach.
—Use existing risk management processes: an organisation may use their existing risk management processes to identify and assess the information security risks potentially leading to aviation safety risks.
—Reuse existing controls: an organisation may reuse existing controls, such as access controls or incident management process, to implement the information security controls required by the ISMS.
—Continuous improvement process: an organisation may use the continuous improvement process of existing management systems to improve the ISMS over time.
AMC1 IS.D.OR.200(e) Information security management system (ISMS)
ED Decision 2023/009/R
DEROGATION
Organisations should follow the directions provided in AMC1 IS.D.OR.205(a) and AMC1 IS.D.OR.205(b) to perform a documented information security risk assessment to seek the approval from the competent authority of a derogation under point IS.D.OR.200(e). In order to justify the grounds for an derogation, the risk assessment is expected to provide explanations for the exclusion of all elements from the scope of the ISMS. It is up to the authority to determine whether this assessment is deemed satisfactory for a derogation to be granted.
Organisations that would like to have the risk assessment performed by a third party should consider the requirements of IS.D.OR.235 and the related AMC.
GM1 IS.D.OR.200(e) Information security management system (ISMS)
ED Decision 2025/014/R
Any organisation that believes that it does not pose any information security risk with a potential impact on aviation safety, either to itself or to other organisations, may consider requesting an approval for a derogation by the competent authority following the procedure outlined in AMC1 IS.D.OR.200(e).
Existing safety risk assessments, such as those carried out as part of the SMS, can form the basis of enhanced assessments considering safety risks arising from information security threats.
It should be noted that applications for partial exemption from individual articles are not possible.
APPLICATION FOR A DEROGATION
In order to ensure a consistent approach by organisations when submitting a derogation request, the competent authority may establish an official derogation request application form.
The application for a derogation, based on the application form where one exists or in a format decided by the organisation, will need to be signed by the accountable manager of the applicant organisation and submitted to the appropriate competent authority for review and consideration.
The application for a derogation should contain preliminary information used for a pre-assessment by the competent authority, including:
—Company information and contact information;
—Affected approval(s);
—Detailed justification for the exclusion of the provisions;
—Overview of services that the organisation provides and receives;
—Architecture overview of information systems used for business operation;
—Summary of the high-level information security risk assessment aligned with the above architecture;
—Methodology used to perform the information security risk assessment;
—List of people and roles involved in the information security risk assessment process;
—Date and signature.
Note: At this stage, the high-level risk assessment needs to properly document the absence of information security risks that may impact safety. To do so, it should at least cover the identification of the scope and boundaries, as required under points IS.D.OR.205 (a) and (b), and the analysis of safety impact, as required under point IS.D.OR.205(c).
EVALUATION OF THE REQUEST FOR A DEROGATION
The competent authority reviews the information security risk assessment and other supporting documentation, normally assessing whether:
—the documentation is sufficient for a proper analysis and assessment;
—the repository or asset inventory of digital systems, data flows and processes is comprehensive;
—the high-level information security risk assessment has been conducted in accordance with the organisation’s methodology and with the appropriate diligence;
—the relevant stakeholders have been involved in the assessment process;
—the assessment has been performed by people with sufficient expertise in information security and aviation safety;
—the organisation has assigned and indicated a point of contact for enquiries.
Figure 1 below depicts the process, including the pre-assessment. If the pre-assessment provides the competent authority with sufficient evidence that the derogation request is legitimate and that the organisation meets the expected criteria, the process will proceed to the exchange of more detailed information.
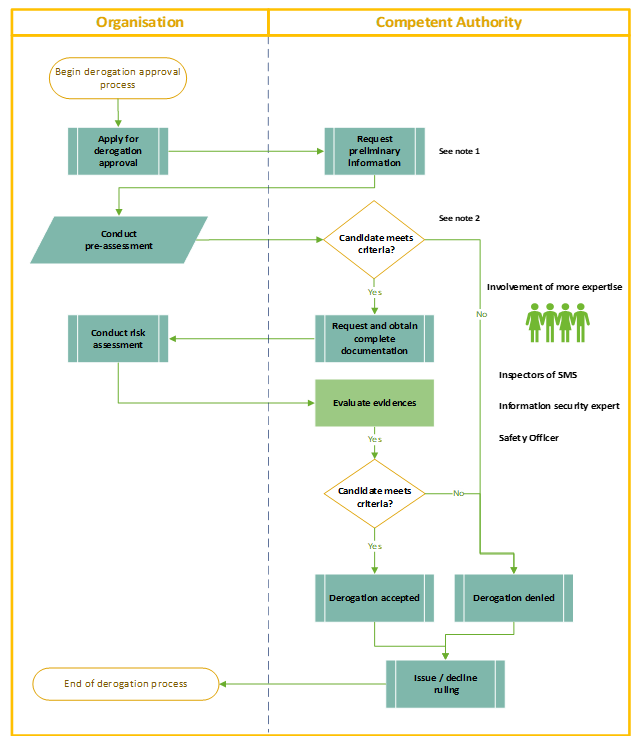
Figure 1: Representation of the derogation process
Note 1 to Figure 1: The objective of this step is to obtain preliminary information about the organisation risk profile by using suitable means (e.g. questionnaire, self-assessment template, request tool, etc.)
Note 2 to Figure 1: The objective of this step is to conduct a pre-evaluation to check whether the organisation has the possibility to be granted a derogation. The pre-assessment allows to avoid a detailed assessment if the prerequisites for a derogation are not met.
EXPECTATIONS AND RECOMMENDATION AFTER DEROGATION APPROVAL
Once a derogation approval has been granted, the organisation is expected to undertake the following on a continuous basis:
—Comply with all provisions of the regulation which are not exempted, in particular point IS.D.OR.200(a)(13) which should not be limited to only protection of the received information. When transmitting information with confidential nature, the organisation needs to have secure means in place as well;
—Comply with Regulation (EU) No 376/2014 to take into account the obligation to comply with the reporting requirements.
—Monitor any changes in the organisation’s scope of work and identify those which may have a potential impact on the documented information, which supports the derogation approval. Where such changes are identified, the organisation should ensure that they are brought to the attention of the competent authority without delay and notified in accordance with the applicable implementing rule.
—Monitor the risk picture for any variation due to changes in the safety and security environment over time. To this end, point IS.D.OR.205(d) should be considered.
—Ensure that the accountable manager or the head of the design of the organisation can demonstrate an understanding of the derogation process and the terms on which the approval has been granted. This means that at least one person in the organisation needs to have a basic understanding of the Regulation. To this end, point IS.D.OR.240(a)(3) and the related AMC and GM should be considered.
—Implement basic protection against information security risks according to industry best practices.
—Remain up to date with the latest information security threat landscape and consult the respective national authority for additional guidance.
EXAMPLES
An example of organisations that may consider asking for a derogation might include DOA or POA holders that design or produce only components or parts that either are not involved in ensuring the structural integrity of the aircraft (e.g. carpets, interiors) or have no major safety-related aircraft functionalities, including but not limited to, aircraft software, navigation, avionics, engines, flight control, landing gear, hydraulic, electrical, air, communications, etc.
The aforementioned example is only indicative of a potential scenario that might provide an initial basis for the preparation of an information security risk assessment that justifies the exclusion of all elements of an organisation from the scope of the ISMS.
IS.D.OR.205 Information security risk assessment
Regulation (EU) 2022/1645
(a)The organisation shall identify all of its elements, which could be exposed to information security risks. That shall include:
(1)the organisation’s activities, facilities and resources, as well as the services the organisation operates, provides, receives or maintains;
(2)the equipment, systems, data and information that contribute to the functioning of the elements listed in point (1).
(b)The organisation shall identify the interfaces that it has with other organisations, and which could result in the mutual exposure to information security risks.
(c)With regard to the elements and interfaces referred to in points (a) and (b), the organisation shall identify the information security risks which may have a potential impact on aviation safety. For each identified risk, the organisation shall:
(1)assign a risk level according to a predefined classification established by the organisation;
(2)associate each risk and its level with the corresponding element or interface identified in accordance with points (a) and (b).
The predefined classification referred to in point (1) shall take into account the potential of occurrence of the threat scenario and the severity of its safety consequences. Based on that classification, and taking into account whether the organisation has a structured and repeatable risk management process for operations, the organisation shall be able to establish whether the risk is acceptable or needs to be treated in accordance with point IS.D.OR.210.
In order to facilitate the mutual comparability of risks assessments, the assignment of the risk level pursuant to point (1) shall take into account relevant information acquired in coordination with the organisations referred to in point (b).
(d)The organisation shall review and update the risk assessment carried out in accordance with points (a), (b) and (c) in any of the following situations:
(1)there is a change in the elements subject to information security risks;
(2)there is a change in the interfaces between the organisation and other organisations, or in the risks communicated by the other organisations;
(3)there is a change in the information or knowledge used for the identification, analysis and classification of risks;
(4)there are lessons learnt from the analysis of information security incidents.
GM1 IS.D.OR.205 Information security risk assessment
ED Decision 2023/009/R
Part-IS does not require the use of any specific information security framework, such as ISO, NIST, or others to develop the risk assessment or in general to implement risk management. Each framework offers different benefits and none of these frameworks is perfect for an individual organisation and should be customised and tailored to meet the overall needs of an organisation as well as the specific need to consider aviation safety aspects.
Organisation whose information security frameworks have achieved industry certifications can provide this information as supporting artefacts; however, these organisations should show the applicability of the industry certification to the scope of this Regulation (see GM1 IS.D.OR.200).
General guidance on risk management, including risk assessment, can be found in ISO/IEC 27005 and ISO/IEC 31000 as well as NIST SP 800-30. Aviation organisations may also wish to consider aviation-specific guidance as defined in the risk management chapter of the latest version of EUROCAE ED-201A and, as appropriate to the specific operating environment, in the chapters of EUROCAE ED-204A, UROCAE ED-205A and EUROCAE ED-206 covering risk management.
AMC1 IS.D.OR.205(a) Information security risk assessment
ED Decision 2023/009/R
When conducting an information security risk assessment, the organisation should ensure that all relevant aviation safety elements are identified and included in the ISMS scope as per IS.D.OR.200 and related AMC.
A means to comply with the requirement in point IS.D.OR.205(a) is to perform a preliminary high-level risk assessment or impact assessment, carried out in accordance with a documented methodology and following precise criteria for the inclusion in and exclusion from the ISMS scope of the elements listed in IS.D.OR.205(a).
GM1 IS.D.OR.205(a) Information security risk assessment
ED Decision 2023/009/R
SCOPE AND BOUNDARIES IDENTIFICATION
The organisation should develop clear and comprehensive understanding of its aviation activities and services, the related processes and associated information systems, and the relevant data flows and information exchanges that define the scope of the ISMS and the boundaries for risk assessment. Therefore, the organisation should develop corresponding documentation on resources and dependencies related to computing, networking and contracted services which have the potential to affect the information security and safety of the functions, services, or capabilities within the scope of the risk assessment.
The following non-exhaustive list provides examples of items that may be considered for the identification of the aforementioned scope and boundaries. The level of detail of the analysis can be an iterative process, with the effort commensurate with the expected level of risk. As stated above, the purpose is to establish understanding of all relevant assets, resources and dependencies that are directly a part of the functions, services and capabilities through the following activities:
(a)Identification of operational inputs and outputs relevant to the functions, services and capabilities of the organisation; these can be related to:
—Internal or external sources;
—internal or external leased or managed services, or other dependencies;
(b)Identification of all relevant assets (i.e. hardware, software, network and computing resources) used to create, process, transmit, store or receive the aforementioned operational inputs and outputs;
(c)Identification of the operating environments (e.g. office, public access area, access-controlled room etc.) and locations for all relevant assets;
(d)For each asset included in the scope, identification of the specific methods, processes and resources that will be used to manage, operate and maintain each asset throughout its life cycle, including:
—internal or contracted resources;
—contracted companies remotely managing the assets (i.e. provider of managed services).
AMC1 IS.D.OR.205(b) Information security risk assessment
ED Decision 2023/009/R
The organisation should, as part of the information security risk assessment, identify the interfaces it has with other parties such as service providers, supply chains and other third parties, based on the exchange of data and information and the assets used for that exchange, which could lead to a situation where information security risks, as a result of mutual exposure, may either:
—increase aviation safety risks faced by other parties; and/or
—increase aviation safety risks faced by the organisation.
GM1 IS.D.OR.205(b) Information security risk assessment
ED Decision 2023/009/R
RISK INFORMATION SHARING
Interfacing organisations should share information with each other about the potential exposure to information security risks by following, for instance, the approach detailed in EUROCAE ED-201A, Appendix B — B.1, B.2 and B.3. The purpose of this exchange of information is to enable organisations to establish a matching mapping for the services identified under IS.D.OR.205(a), including all information and data flows, in order to:
(a)illustrate (e.g. through a functional diagram) the relationships of logical and physical paths connecting the different parts involved;
(b)clearly identify all assets (i.e. hardware, software, network and computing resources) that will be used in the exchange;
(c)identify all functions, activities and processes, including their respective information and data, which will be created, transmitted, processed, received and stored, and associate those with the responsible party which provides or performs those functions, activities and processes;
(d)determine for these paths, constituting the so-called functional chains, the role of the interfacing party as a producer, processor, dispatcher or consumer of the information or data involved;
(e)determine whether one interfacing party acts as an originator or receiver of a flow across such path.
TWO CATEGORIES OF INTERFACING ORGANISATIONS
There are two categories of interfacing organisations: those that are subject to Regulation (EU) 2023/203 or Regulation (EU) 2022/1645, and those that are not.
Where the organisation has interfaces with an organisation that is subject to Regulation (EU) 2023/203 or Regulation (EU) 2022/1645, each entity:
—is responsible for the identification of the interfaces that its own organisation has with other organisations, and which could result in the mutual exposure to information security risks. The entity may benefit from the sharing of risk information as this exchange allows for a more accurate assessment of those risks.
—remains accountable for the proper management of the information security risks within the scope of its own ISMS.
In all other cases, the organisation is accountable for the proper management of the information security risks that may arise from its exposure to the interfacing entity. Where these risks need to be treated, the organisation always has the option of implementing mitigating measures and controls within its own boundaries. In the specific case where the interfacing entity is a supplier, the organisation may decide to manage the risks through contractual arrangements and require the supplier to implement mitigating measures and controls within its own organisation.
GM2 IS.D.OR.205(b) Information security risk assessment
ED Decision 2023/009/R
EXAMPLES OF AVIATION SERVICES
Examples of aviation services that may be considered when determining of the ISMS scope and interfaces are provided in Appendix III.
AMC1 IS.D.OR.205(c) Information security risk assessment
ED Decision 2023/009/R
The organisation should use a risk management framework that includes a methodology for assigning risks with a risk level and establishing criteria for determining risk acceptance or further treatment.
The organisation should provide documented evidence of assessment of risks which have a potential impact on aviation safety including the level of risks. The organisation should associate each risk with the relevant elements and interfaces identified under IS.D.OR.205 (a) and (b), and document whether the risk is acceptable or requires further treatment.
The organisation should provide the assurance that the risk assessment process is carried out with the necessary rigour and discipline by documenting the process and its robustness. By doing so, the organisation should consider:
(a)reproducibility of the assessment’s results for similar inputs;
(b)repeatability of the assessment over time in a way that the results of the different prior assessments can be compared to determine the changes;
(c)the gathering of inputs that are relevant and valid, in particular:
(1)the information that allows the determination of the safety consequences;
(2)the information that allows the determination of the potential of occurrence of the threat scenario;
(d)iterative refinement over time allowing for more fine-grained threat scenarios as inputs become available, with the aimof reducing uncertainty regarding threats, vulnerabilities, effectiveness of existing controls, and dependencies on external entities, in particular by:
(1)refining initial high-level threat scenarios with greater detail and specificity as more data is gathered;
(2)refining data on known vulnerabilities by continuously updating information about their exploitability and the associated consequences;
(3)reviewing the effectiveness of existing controls, and consider newly available controls;
(4)refining the understanding of the dependencies on external entities and their implications for the organisation’s risk profile.
GM1 IS.D.OR.205(c) Information security risk assessment
ED Decision 2023/009/R
RISK ASSESSMENT
The risk classification levels for the potential of occurrence of the threat scenario and severity of the safety consequences listed below may be applied; however, this does not prevent the organisation from developing additional intermediate categories if it deems this necessary for risk assessments. The organisation should specify and document the applied, organisation-specific, classification levels with an accurate qualitative or quantitative definition in terms of a range or interval of numerical values in order to enable a sufficiently calibrated, consistent estimation, evaluation and communication within the organisation or with the interfacing entities. The potential of occurrence of the threat scenario may be expressed as an interval of likelihoods including the duration of the observation. Supporting documentation and methods can be found in EUROCAE ED-203A, Chapter 3.6 which references the evaluation of the potential of occurrence of the threat scenario in the Security Risk Assessment of EUROCAE ED-202A.
Note 1: The phrase ‘duration of the observation’ refers to the time period during which a threat scenario is observed or monitored. It is essential in determining the likelihood of the threat scenario occurring, since the probability of occurrence may vary depending on the length of the observation period.
Note 2: EUROCAE ED-202A and EUROCAE ED-203A were originally developed for aircraft information security risk assessment, but the generic principles developed in those documents can be adapted to other frameworks when deemed useful by the organisation.
In order to facilitate the mutual comparability of risk assessment methodologies between interfacing organisations, the organisation may associate the assessment of the potential of occurrence of the threat scenario with one of the following categories:
—High potential of occurrence: the threat scenario is likely to occur. The attack related to the threat scenario is feasible and similar threat scenarios have occurred many times in the past.
—Medium potential of occurrence: the threat scenario is unlikely to occur. The attack related to the threat scenario is possible and a similar threat scenario may have occurred in the past.
—Low potential of occurrence: the threat scenario is very unlikely to occur. The materialisation of the threat scenario is theoretically possible; however, it is not known to have occurred.
The evaluation of the potential of occurrence of the threat scenario may be based on the following aspects:
Protection (as defined in EUROCAE ED-203A)
—Security measures and architecture that deny access to assets: the degree to which an asset is open to access from compromised systems
—Access to security measures: the degree to which a security measure prevents access/attack to itself from compromised systems
—Failure of mechanism: the degree to which the known implementation of a security measure will fail to prevent an attack
—Detection methods or procedures to recognise the attack and appropriately respond to reduce the potential of occurrence of the threat scenario
Exposure reduction (as defined in EUROCAE ED-203A)
—Conditions under which an external access connection can be used by a user or attacker
—Limits on the functionality of an external access connection
—Organisational policies that control the time-to-feasibility for developing attack tools specific to the product
—Vulnerability management including intelligence, scanning, treatment and retesting aimed to discover, detect and treat reported or detected vulnerabilities in a fast, risk-prioritised manner with high assurance in order to reduce the attack surface
—Reduction of the severity of a successful attack (i.e. through a redundant system that can maintain the continuity of service in case of a denial of service of a system critical for aviation safety)
Attack attempt (as defined in EUROCAE ED-203A)
—The capability of the attackers which is determined by the resources and expertise required for their attack
The capability of the attackers can be assessed through several ways, for instance:
—information from computer emergency response teams (CERTs) / computer security incident response teams (CSIRTs), information sharing and analysis centres (ISACs);
—analyses of past activities, techniques and procedures (TTPs) and success rate of attacks.
For the same reason the organisation may associate the outcome of the evaluation of the severity of the safety consequences with one of the following categories:
—High severity: those immediate or delayed scenarios that can cause or contribute to an unsafe condition where an unsafe condition means an occurrence associated with the operation of an aircraft in which:
—a person is fatally or seriously injured;
—the aircraft sustains damage or structural failure;
—the aircraft is either missing or completely inaccessible;
—Moderate severity: those immediate or delayed scenarios that can cause or contribute to safety incidents where an incident means any occurrence other than an accident, associated with the operation of an aircraft, which affects or could affect the safety of operations;
—Low severity: those immediate or delayed scenarios that can cause or contribute to negligible safety consequences.
Examples for high, moderate, and low severity can be found in EUROCAE ED-201A, Appendix B for products, ATM systems and airspace.
If the organisation cannot determine the safety effect, the assessment should identify assumptions from the risk-sharing information at interfaces with other organisations along the functional chain, leading up to the safety effect.
Some of those assumptions can be granted with the certification of products: where assets are subject to product certification from other aviation regulations addressing product information security, the organisation performing the risk assessment may consider the perimeter of the product certification as already covered. This should be acceptable under the condition that this certification is valid and that the instructions provided by the OEM to maintain the certification validity are implemented by the organisation.
Additional information can also be found in Regulation (EU) 2015/1018 on mandatory reporting of occurrences in civil aviation. Further examples of impact severity classifications for aviation domains can be found in EUROCAE ED-201A, Appendix B — Tables B-5, B-6 and B-7.
Risk acceptance criteria
Risk acceptance criteria are critical and should be developed, specified and documented. The criteria may define multiple thresholds, with a desired target risk level, but allowing also for the accountable manager or, in the case of design organisations, for the head of the design organisation, or delegated persons to accept risks above this level under defined circumstances and conditions.
In order to facilitate the mutual comparability of risk assessments between interfacing entities, the organisation should classify the risks in the following categories:
—unacceptable risk;
—conditionally acceptable risk;
—acceptable risk.
For what concerns the conditional acceptance of risks, the criteria for acceptance should take into account how long a risk is expected to exist (temporary or short-term activity or exposure), or may include requirements for the commitment of future treatments to reduce the risk at an acceptable level within a defined time duration and show how the risk will be managed over time through the organisation’s risk governance processes.
Moreover, risks should be conditionally accepted only under the condition that the organisation demonstrates the presence of a comprehensive risk management structure that includes risk assessment, risk treatment and risk monitoring processes for operations. The risk management should consider the variability and consistency of threat likelihood, vulnerability, existing controls, external dependencies and safety impact. This is typically achieved when the organisation reaches a higher level of maturity that is representative of functionality and repeatability of information security risk management — see GM1 IS.D.OR.260(a).
The following Figure 1 depicts a risk acceptance matrix based on the aforementioned categories that can be used by interfacing organisations for mutual comparability.
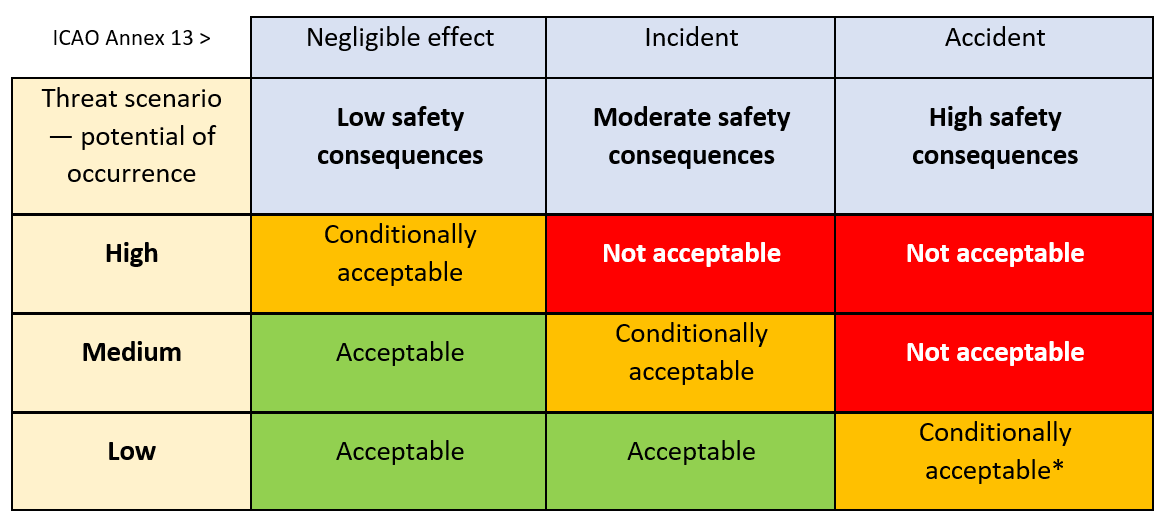
Figure 1: Example of a risk acceptance matrix for comparison purposes
* The potential of occurrence of the threat scenario is reassessed in a timely manner (refer to IS.D.OR.205(d)) and monitored to ensure that it remains low and that if the risk materialises, it is early detected and dealt with.
A comprehensive risk management structure typically entails the following aspects and processes:
—a repeatable and reproduceable risk assessment. If the risk factors are considered fairly uncertain and within some wide value range or not sufficiently precise, further iterations of the risk assessment are performed involving additionally gathered or detailed information and a more in-depth assessment in order to reduce uncertainty and increase precision;
—a thorough review of those risks proposed to be conditionally acceptable that is performed by the accountable manager or, in the case of design organisations, by the head of the design organisation, or delegated person(s) who may impose additional conditions for the risk retention, including risk treatment measure and the timeline for its implementation;
—strict monitoring of the key risk indicators that includes a defined, reliable detection of the potentially evolving risk materialisation;
—an incident response scheme is in place with reactive measures that are triggered by detection mechanisms in order to immediately contain the consequences, in particular, for risk scenarios involving a high severity level.
Note: As detailed in NIST SP-800 Rev.1, repeatability refers to the ability to repeat the assessment in the future, in a manner that is consistent with and hence comparable to prior assessments —enabling the organisation to identify trends. Therefore, a risk assessment process can be classified as ‘repeatable’ when under similar conditions an entity or a person delivers consistent results.
As detailed in NIST SP-800 Rev.1, reproducibility refers to the ability of different experts to produce the same results from the same data. Therefore, a risk assessment process can be classified as ‘reproducible’ when another entity or person, given the same inputs, assumptions, information security context and threat environment can replicate the same steps and reach the same conclusions.
Threat scenario identification
A threat scenario is one of the possible ways a threat could materialise. Typically, a threat scenario describes a potential attack targeting one or more vulnerabilities of assets, as well as processes.
The purpose of the threat scenario identification under this Regulation is to develop a list of scenarios that may lead to an information security threat having an impact on aviation safety.
A threat scenario, in general, is characterised by the following:
—a threat source of the information security attack;
—an attack vector and a path through the organisation up to the asset;
—the information security controls that would mitigate the attack;
—the consequence of the attack including the affected safety aspects.
Threat scenario identification guidance can be found in EUROCAE ED-202A, Chapter 3.4. This is not the only source where guidance can be found, and the organisation may refer to different guidance more appropriate for their application.
Additional methods to identify relevant threat scenarios
When conducting this analysis, both information security and safety aspects should be coordinated throughout the process to ensure mutual understanding of the threat preventive measures and mitigating measures being applied. In the following Figure 2 the interactions between information security and aviation safety are depicted through a ‘bow-tie’ diagram that highlights the links between risk controls and the underlying management system.
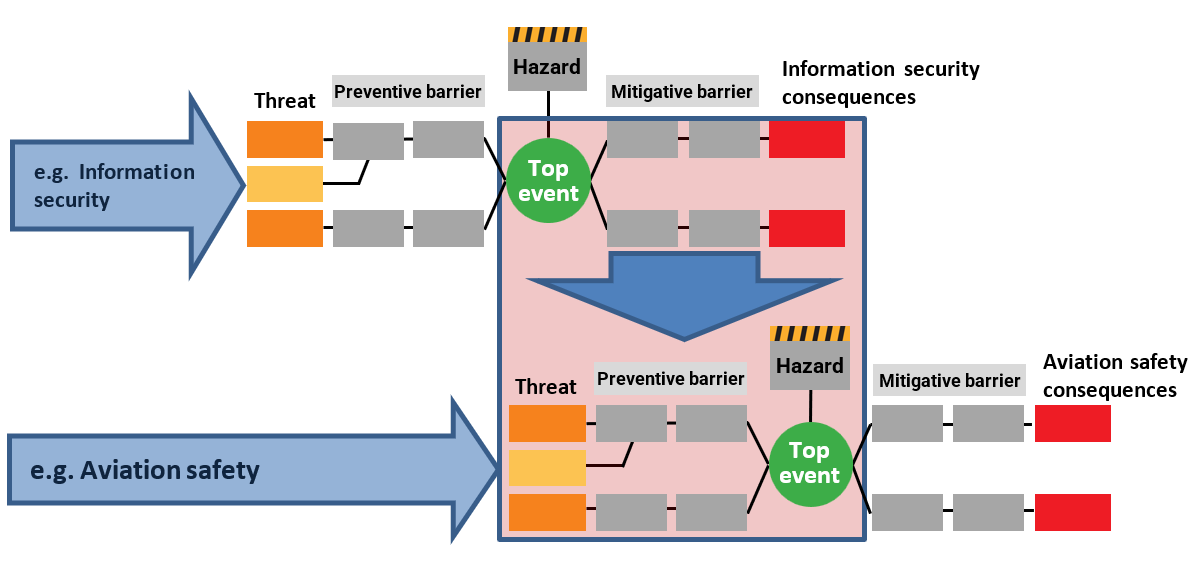
Figure 2: Interactions between information security and aviation safety risk management areas
Note: A preventive barrier or measure is a proactive action or control implemented to reduce the likelihood of a risk, hazard, or threat materialising while a mitigating measure is an action or control designed to reduce the severity or impact of an undesired event, would it occur.
Examples of threat scenarios
Threat catalogues may provide guidance and elements for the elaboration of threat scenarios that are relevant for the organisation. References can be found in ARINC 811 – Att. 3 – Tables 3-7 and 3-8 for the threat catalogues examples and other threat catalogue examples as they are provided by EU institutions — for example, the ENISA threat taxonomy. However, this is not an exhaustive list of examples, and the identification of threat scenarios should therefore not be limited to those examples only. In addition, other relevant resources containing information on information security threats and the information security threat landscape should be consulted to support the risk assessment process with relevant inputs.
A set of examples of threat scenarios can be found in Appendix I.
AMC1 IS.D.OR.205(d) Information security risk assessment
ED Decision 2023/009/R
The organisation should take into account the following criteria when establishing compliance with the objectives contained in point IS.D.OR.205(d):
(a)The risk assessment performed under points IS.D.OR.205(a), (b) and (c) should be reviewed at regular intervals to identify and account for relevant changes. The periodicity at which potential changes have to be evaluated should be determined by the organisation performing the assessment considering the criticality of the assets within the scope of the risk assessment, levels of residual risk of the assets within the scope of the risk assessment and any contractual or regulatory requirements. A higher criticality or level of risk will require more frequent review.
(b)The periodicity of risk assessment reviews should be documented by the organisation and include the justification, date of approval and information about the risk owner.
GM1 IS.D.OR.205(d) Information security risk assessment
ED Decision 2023/009/R
The criteria to consider for the frequency of the risk assessment review may be the risk level as well as the criticality and complexity of the assets concerned. The objective of a risk assessment review is to trigger the revaluation of risks, their likelihood and impact in case of relevant changes. One possible way is to have a tiered approach to risk assessment, with a higher-level risk assessment being used for the identification of changes. The higher-level risk assessment could allow the identification of the detailed risks that should be reviewed in a next step. Risk assessments should be subject to regular reviews to:
(a)allow for continuous improvement of the quality of risk assessment;
(b)ensure efficiency and effectiveness of risk controls and mitigating measures in both their design and operation;
(c)review plans and actions for risk treatment;
(d)identify any organisational change which may require a review of the priorities as well as of the treatment of risks;
(e)maintain an overview of the complete risk picture; and
(f)identify any emerging risks.
Risk assessment reviews should involve the risk owners, project teams and other stakeholders as applicable. Evidence of risk assessment review should be documented and should include:
—evidence of approval of the review by the designated risk owner; and
—the rationale behind or basis for the risk owner’s approval of the review.
Such evidence may comprise, but is not limited to:
—reports which constitute a form of documentation to track information security risks potentially impacting an organisation;
—the documentation of the information security risk assessment;
—exerts from a business or security risk register.
The periodicity of risk assessment reviews should also be documented by the organisation in information security manuals, processes or procedures and should align with wider change management activities and management reviews of information security. Further guidance on criteria and frequency of risk assessment review can be found in EUROCAE ED-201A, Chapter 4, as well as in EUROCAE ED-205A, Chapter 3.2 (for ATMS/ANS).
GM2 IS.D.OR.205(d) Information security risk assessment
ED Decision 2023/009/R
The following are examples of changes that should be identified during the risk assessment review as they may trigger an update of the risk assessments:
(a)there is a change in the elements subject to information security risks as identified in IS.D.OR.205(a); a change in the elements will include:
—additions to, or removals from, the scope of the risk assessment of individual elements;
—changes to design or configuration of elements within the scope of the risk assessment that have the potential to alter the risk assessment outcomes; or
—changes to values, which would potentially trigger changes to impact levels, of elements within the scope of the risk assessment;
(b)there is a change in the interfaces between the organisation and other organisations with which the organisation shares information security risks or relies upon to mitigate information security risks (e.g. supply chains, service providers, cloud providers and customers), as identified in IS.D.OR.205(b), or between the system within the scope of the risk assessment and any other interconnected systems, or in the risks notified to the organisation by other organisations, as identified in IS.D.OR.205(b), or owners or managers of the other systems including:
—establishment of new interfaces;
—removal of existing interfaces;
—changes to existing interfaces that would have the potential to alter the risk assessment outcomes.
Note: Some organisational or system interconnections may be with organisations that are not within the scope of this Regulation as defined in Article 2 and therefore are not subject to the requirements of Part-IS. Where this is the case, these organisations should be informed of their responsibility to report such changes as listed above through contractual arrangement and reporting requirements between the affected organisations on a case-by-case basis and where applicable;
(c)there is a change in the information or knowledge used for the identification, analysis and classification of risks including:
—changes to threats and their values or addition of new threats that have not previously been assessed;
—changes to vulnerabilities or addition of new vulnerabilities that have not previously been assessed;
—changes in impacts or consequences of assessed threats or vulnerabilities;
—changes in aggregation of risks that may result in unacceptable levels of risks;
—changes or improvements in the risk management process, risk assessment approach and related activities;
—changes or improvements in the treatments of risks;
—changes in the criteria used to determine acceptance and treatments of risks;
(d)there are lessons learned from the analysis of information security incidents including:
—understanding why and how incidents have occurred; and
—reviewing all types of incidents including those due to external factors, technical reasons, human errors (inadvertent behaviour). For human intentional acts a distinction can be made between malign and benign actions.
IS.D.OR.210 Information security risk treatment
Regulation (EU) 2022/1645
(a)The organisation shall develop measures to address unacceptable risks identified in accordance with point IS.D.OR.205, implement them in a timely manner and check their continued effectiveness. Those measures shall enable the organisation to:
(1)control the circumstances that contribute to the effective occurrence of the threat scenario;
(2)reduce the consequences on aviation safety associated with the materialisation of the threat scenario;
(3)avoid the risks.
Those measures shall not introduce any new potential unacceptable risks to aviation safety.
(b)The person referred to in point IS.D.OR.240(a) and (b) and other affected personnel of the organisation shall be informed of the outcome of the risk assessment carried out in accordance with point IS.D.OR.205, the corresponding threat scenarios and the measures to be implemented.
The organisation shall also inform organisations with which it has an interface in accordance with point IS.D.OR.205(b) of any risk shared between both organisations.
GM1 IS.D.OR.210 Information security risk treatment
ED Decision 2025/014/R
Unacceptable risks identified in accordance with point IS.D.OR.205 require a risk treatment process that may lead to the introduction of information security measures, often referred to as information security controls.
For each identified risk, the organisation defines the specific risk treatment measures, methods or resources that will be used over the life cycle of each asset to:
—manage risk reduction;
—monitor and maintain each asset;
—update and fulfil activities for configuration management;
—manage supply chain;
—manage contracted services or service provider.
The review of risk treatment measures includes life cycle considerations which are introduced by equipment, procedures and personnel.
A risk treatment plan as an outcome of the risk management process includes a prioritisation of risks, the corresponding information on the objectives and means for risk treatment to reach an acceptable level of risk, as well as agreed timelines specifying when responsible personnel should have implemented the risk treatment measures. The timelines for the implementation of a risk treatment measure are subject to agreement by the personnel responsible for the implementation and are communicated to and accepted by the accountable manager or, in the case of design organisations, by the head of the design organisation, of the organisation or delegated person(s).
Any subsequent implementation delay, together with its cause, reason, rationale or necessity, is documented in the risk treatment plan, for risks that may lead to an unsafe condition. The delay is also subject to the acceptance by the accountable manager of the organisation, or by the head of the design organisation, or delegated person(s). This person may condition such acceptance on the implementation or availability of compensating controls or reactive measures to monitor, early detect and timely respond to the materialisation of the risk in treatment. In order to timely respond, the incident response team may be informed to trigger their preparedness.
The risk treatment plan can act as a means of communication with the competent authority to demonstrate effective treatment of unacceptable risks. Similarly, this plan can be utilised to communicate to interfacing organisations how shared risks are controlled.
In accordance with IS.D.OR.205(d), a regular or conditional review of the risk assessment is necessary, and this includes the review of the risk treatment measures developed under IS.D.OR.210(a) to identify whether they are still effective or they require adaptations.
In addition, the organisation should also consider the potential impact on the effectiveness of risk treatment measures where a shared information security risk may arise as a result of the interaction between interfacing entities (see IS.D.OR.235 and related AMC).
AMC1 IS.D.OR.210(a) Information security risk treatment
ED Decision 2023/009/R
(a)The risk treatment process should reach at least one of the objectives listed under IS.D.OR.210(a).
(b)When establishing compliance with the objectives under points IS.D.OR.210(a)(1) and IS.D.OR.210(a)(2), the organisation should take into account that:
(1)the measures developed under these points should be implemented according to a risk treatment plan with defined, risk-based priorities, objectives and agreed timelines and owners;
(2)life cycle considerations should be identified and associated to ensure continuous effectiveness of the information security measures including exchange of data with other entities;
(3)it should review and update the risk assessment, according to IS.D.OR.205(d), to evaluate whether the measures developed under these points introduce new unacceptable risks or modify existing risks in a way that they become unacceptable.
(c)Risk treatment should be documented and recorded, for example, in a risk registry, even if the risk has been avoided.
IS.D.OR.215 Information security internal reporting scheme
Regulation (EU) 2022/1645
(a)The organisation shall establish an internal reporting scheme to enable the collection and evaluation of information security events, including those to be reported pursuant to point IS.D.OR.230.
(b)That scheme and the process referred to in point IS.D.OR.220 shall enable the organisation to:
(1)identify which of the events reported pursuant to point (a) are considered information security incidents or vulnerabilities with a potential impact on aviation safety;
(2)identify the causes of, and contributing factors to, the information security incidents and vulnerabilities identified in accordance with point (1), and address them as part of the information security risk management process in accordance with points IS.D.OR.205 and IS.D.OR.220;
(3)ensure an evaluation of all known, relevant information relating to the information security incidents and vulnerabilities identified in accordance with point (1);
(4)ensure the implementation of a method to distribute internally the information as necessary.
(c)Any contracted organisation which may expose the organisation to information security risks with a potential impact on aviation safety shall be required to report information security events to the organisation. Those reports shall be submitted using the procedures established in the specific contractual arrangements and shall be evaluated in accordance with point (b).
(d)The organisation shall cooperate on investigations with any other organisation that has a significant contribution to the information security of its own activities.
(e)The organisation may integrate that reporting scheme with other reporting schemes it has already implemented.
AMC1 IS.D.OR.215(a)&(b) Information security internal reporting scheme
ED Decision 2023/009/R
Organisations should use as a source the incidents detected during activities performed to show compliance with IS.D.OR.220(a). Organisations should have a mechanism to collect notifications of events by personnel and by sources outside the company including suppliers, partners, customers, open-source software, and information security researchers. The mechanism for collecting information by personnel and external sources should be easily accessible and communicated.
The organisation should collect all events gathered through the detection means for internal analysis. Each event should be analysed to identify whether it is reportable and if so, what potential or actual impact on aviation safety has occurred. Information security events should be considered in combination with other events to provide correlation to identify incidents or vulnerabilities with a potential impact on aviation safety.
The organisation should consider the outcome of the risk assessment and the exploitability of new vulnerabilities discovered during the detection activities conducted according to the measures required in IS.D.OR.220(a).
The organisation should identify all internal stakeholders that require notification of a specific incident or vulnerability and ensure that these stakeholders receive all necessary information on the incident or vulnerability in order to act effectively and in a timely manner to support the required detection and response periods.
GM1 IS.D.OR.215(a)&(b) Information security internal reporting scheme
ED Decision 2023/009/R
RELATIONSHIP BETWEEN INTERNAL AND EXTERNAL REPORTING
Organisations should collect and report internally incidents and vulnerabilities aiming at covering all items within the scope of this Regulation. Both internal and external reporting are necessary for a complete and effective reporting system. Internal reports should be assessed in a timely manner and where the potential impact on safety is an unsafe condition, organisations should initiate reporting of these internal reports according to IS.D.OR.230.
GM2 IS.D.OR.215(a)&(b) Information security internal reporting scheme
ED Decision 2023/009/R
ORGANISATION OF COLLECTION AND EVALUATION OF INFORMATION SECURITY EVENTS
It is a common practice in large organisations to centralise information security operations in a security operations centre (SOC) and make use of an information security information and event management (SIEM) system. A SIEM system collects all events from sources such as log files in a common database and allows the analysts and responders in a joint SOC to review and act on these events. Organisations may choose to use a SOC for events relevant to Part-IS in isolation or in combination with events not subject to Part-IS but of interest to the organisation, such as events relating to business interests. Events can be automatically aggregated, correlated and analysed in order to detect abnormal behaviour leading to information security incidents.
Organisations that do not have a SOC capability and do not use a SIEM system need to consider how to establish processes to meet the required collection and evaluation capabilities as well as detection and response times.
GM3 IS.D.OR. 215(a)&(b) Information security internal reporting scheme
ED Decision 2023/009/R
RELEVANT INFORMATION FOR INCIDENTS AND VULNERABILITIES
Understanding the causes of, and contributing factors to, information security incidents and vulnerabilities relevant to Part-IS allows lessons learned to be gained and to introduce corrections to processes and asset design. However, understanding causes and contributing factors may not always be possible or may not aid in continuous improvement of aviation safety. Where vulnerabilities arise from assets developed solely or primarily for aviation, it is expected to be possible to perform the necessary investigation on the root causes. These root causes will inform the affected organisation(s) to improve processes and asset design to remediate vulnerability and to ensure that such vulnerabilities are not introduced in other assets. Understanding the root causes of vulnerabilities also allows the aviation community to learn and thus avoid similar vulnerabilities in the future.
GM1 IS.D.OR.215(c) Information security internal reporting scheme
ED Decision 2023/009/R
If contracted organisations are also subject to this Regulation, the exchange of information and reporting should be covered under the management of shared risks and through the establishment of an external agreement between the organisations. Guidance regarding the development of external agreements can be found in EUROCAE ED-201A, Chapter 4.4 External agreements.
More in general, and in all other cases, any service contract should include standard clauses concerning obligations for the contracted organisation to:
—report within an agreed time information security incidents that may have an impact on the contracting organisation. Incidents and vulnerabilities which could lead to unsafe conditions should be reported as soon as possible and in such a manner that the external reporting obligation under IS.D.OR.230 can be ensured;
—designate a point of contact for the incident management and possible crisis management.
In some cases contracted organisations, such as service providers with distributed resources, may not be able to offer any ad hoc reporting. In these cases the internal reporting requirement may be fulfilled through other means that satisfy the objective of this provision. For instance, the contracted organisations may provide an up-to-date list of vulnerabilities affecting the systems within the scope of the contracted services. This list should be monitored by the contracting organisation as part of the internal reporting of information security events.
GM1 IS.D.OR.215(d) Information security internal reporting scheme
ED Decision 2023/009/R
The cooperation under point IS.D.OR.215(d) can be substantiated by sharing elements from incident records that can support other organisations’ information security activities. In case the organisations are bound by contractual obligations, this contract may also include commitment to cooperate. Organizations may consider developing formal agreements (e.g. memorandum of understanding) outlining roles and responsibilities for information security collaboration such as governance meetings, joint development activities, and real-time indicators of compromise (IoC) sharing.
Moreover, commitment to cooperate may also be achieved through the active participation of the organisation in information security sharing initiatives; for instance, ISAC(s). Additionally, for their own awareness, organisations may also subscribe to receive vulnerability and threat alerts, like those distributed by CERTs.
IS.D.OR.220 Information security incidents — detection, response and recovery
Regulation (EU) 2022/1645
(a)Based on the outcome of the risk assessment carried out in accordance with point IS.D.OR.205 and the outcome of the risk treatment performed in accordance with point IS.D.OR.210, the organisation shall implement measures to detect incidents and vulnerabilities that indicate the potential materialisation of unacceptable risks and which may have a potential impact on aviation safety. Those detection measures shall enable the organisation to:
(1)identify deviations from predetermined functional performance baselines;
(2)trigger warnings to activate proper response measures, in case of any deviation.
(b)The organisation shall implement measures to respond to any event conditions identified in accordance with point (a) that may develop or have developed into an information security incident. Those response measures shall enable the organisation to:
(1)initiate the reaction to the warnings referred to in point (a)(2) by activating predefined resources and course of actions;
(2)contain the spread of an attack and avoid the full materialisation of a threat scenario;
(3)control the failure mode of the affected elements defined in point IS.D.OR.205(a).
(c)The organisation shall implement measures aimed at recovering from information security incidents, including emergency measures, if needed. Those recovery measures shall enable the organisation to:
(1)remove the condition that caused the incident, or constrain it to a tolerable level;
(2)reach a safe state of the affected elements defined in point IS.D.OR.205(a) within a recovery time previously defined by the organisation.
GM1 IS.D.OR.220 Information security incidents — detection, response and recovery
ED Decision 2023/009/R
Without prejudice to the definition of ‘information security event’ in Article 3 of Regulation (EU) 2022/1645, those events that indicate the potential materialisation of unacceptable risks include both occurrences (i.e. anything that causes harm or have the potential to cause harm) and discovery of vulnerabilities. In fact, information security risks are associated with the potential that threats will exploit vulnerabilities, therefore the discovery of an exploitable vulnerability is an information security event.
In light of this, in the context of this Regulation:
—detection activities required under IS.D.OR.220(a) include vulnerability discovery;
—response activities under IS.D.OR.220(b) include vulnerability management.
AMC1 IS.D.OR.220(a) Information security incidents — detection, response and recovery
ED Decision 2023/009/R
DETECTION
When complying with the requirement in IS.D.OR.220(a), the organisation should define and implement a strategy to detect information security incidents which may have a potential impact on safety.
This should be done in a way to ensure that at least the detection strategy is able to cover all known information security threats to their assets that may materialise in a safety hazard having unacceptable consequences.
DETECTION STRATEGY
In order to determine the scope of the event detection, the organisation should:
(a)identify a list of threat scenarios from the risks identified under IS.D.OR.205;
(b)identify, as a minimum, those assets that, if compromised, contribute to the scenario(s) that may materialise in an unsafe condition. For this identification of the assets, the measures introduced under IS.D.OR.210 should also be considered.
Note: The contribution of an asset to the threat scenario and the materialisation of an unsafe condition should be assessed by considering also the whole functional chain. In some cases, the asset may be at the end of a functional chain and if it is compromised, the effect on safety is direct and may be immediate; conversely, if the asset is far from the end of a functional chain and it is compromised, the effect should propagate and may be delayed.
GM1 IS.D.OR.220(a) Information security incidents — detection, response and recovery
ED Decision 2023/009/R
DETECTION STRATEGY
When developing the detection strategy, for those items within the scope of event detection, the organisation should define the conditions that trigger a process that, for example, would require personnel intervention and further analysis. These conditions on the items may be defined using elements from the:
(a)expected functional baseline: engage in the identification of deviations from the expected functional operation of the system (excluding information security functions/controls);
(b)expected information security baseline: engage in the identification of deviations from the expected information security operation of information security controls.
These conditions should consider both abnormal behaviour and substantial deviations from the baselines and relevant correlation of multiple independent events.
Further guidance on the objectives for the establishment of a detection strategy can be found in EUROCAE ED-206, Chapter 4.
AMC1 IS.D.OR.220(b) Information security incidents — detection, response and recovery
ED Decision 2023/009/R
(a)INCIDENTS
The organisation should take into account the following aspects when establishing compliance with the objectives contained in point IS.D.OR.220(b) relative to incidents:
(1)Preparation of procedures and delineation of roles and responsibilities to respond in a timely, effective and orderly manner to any relevant information security incidents.
(2)The response procedure should:
(i)consider the warnings, unitary or combined, from IS.D.OR.220(a)
(ii)establish, in accordance with IS.D.OR.220(b)(2), a containment strategy for each asset category considering the potential worst-case effect and the mission constraints, and provide criteria indicating when the incident is contained;
(iii)define, in accordance with IS.D.OR.220(b)(3), the acceptable impact on safety and information security of each asset within the scope when they fail due to the materialisation of a threat scenario.
(3)The response time should be commensurate with the impact level assessed in (2)(iii).
(4)The response measures implemented under IS.D.OR.220(b) should be based on the response procedure referred to in the point (a)(2) and they should, in particular, consider the following:
(i)the maximum acceptable safety level degradation of the assets within the scope of incident;
(ii)the actions, such as resistance, containment, deception and control of the possible ways systems can fail, which will contribute to achieving the acceptable safety level degradation identified in point (i) while minimising the impact on operations;
(iii)the resources required to implement the actions specified in point (ii).
(5)The response time and the measures should take into account the potential immediate negative impact on safety if the measure is taken before it has been fully verified that it would not cause additional immediate safety impacts.
(b)VULNERABILITIES
The organisation should take into account the following aspects when establishing compliance with the objectives contained in point IS.D.OR.220(b) relative to vulnerabilities:
(1)Establishment of a vulnerability management strategy defining procedures, roles and responsibilities to respond in a timely, effective and orderly manner to any detected relevant vulnerabilities.
(2)The response measures implemented under point IS.D.OR.220(b) should be based on the maximum acceptable risk of the items within the scope of the vulnerability, considering the worst-case scenario of the vulnerability being exploited.
(3)The response time should be commensurate with the pre-triage done on the warnings and the assessment of the potential impact of the vulnerability, if it is exploited.
GM1 IS.D.OR.220(b) Information security incidents — detection, response and recovery
ED Decision 2023/009/R
An attack is considered contained (i.e. it is not spreading any further) when the boundaries of the incident have been identified and the threat does not propagate beyond these boundaries. Further guidance can be found in EUROCAE ED-206, Chapter 5.
The term ‘warning’ as used in IS.D.OR.220 should be understood as an alert that would require timely awareness and response from the information security events management team.
In the context of information security response, ‘deception’ refers to a range of techniques that aim to mislead potential attackers or malicious users, thereby protecting the system and its data. Deception techniques, such as honeypots or breadcrumb trails, are designed to confuse, slow down, or divert attackers, increasing their cost and risk while providing defenders with valuable time and intelligence.
Guidance regarding the vulnerability management strategy can be found in EUROCAE ED-206, Chapter 3.4 — Vulnerability management considerations. This is not the only source where guidance can be found, and the organisation may refer to different guidance more appropriate for their application.
AMC1 IS.D.OR.220(c) Information security incidents — detection, response and recovery
ED Decision 2023/009/R
When complying with the requirement in IS.D.OR.220(c), the organisation should develop an incident recovery procedure including at least the following:
(a)a list of those assets that enable safe operations, as well as the dependencies among them, constituting the scope of the recovery;
(b)a description of the process with the necessary priority actions to be executed for a return to a safe and secure state for the assets within the scope of the recovery;
(c)the resources required to execute the actions defined in point (b) to ensure that these resources are readily available after an incident has occurred;
(d)the objectives for recovery time that should be set in relation to the safety criticality of the assets within the scope of the recovery.
GM1 IS.D.OR.220(b)&(c) Information security incidents — detection, response and recovery
ED Decision 2023/009/R
RECOVERY OBJECTIVES AND TIMING
Point IS.D.OR.220(b) addresses event conditions which may develop or have developed into information security incidents, that may have a potential impact on aviation safety, and require response and recovery measures to be in place to ensure that operational safety remains above a minimum acceptable level.
The level of operations and safety may be interrelated, so in some cases when the level of operations is compromised by an information security incident and drops, the level of safety does the same. This is, for instance, the case of air traffic control; if air traffic services are reduced or become unreliable, the safety of flights is reduced too.
However, in other cases the relation between the level of operations and safety may be the inverse, or they may be decoupled, so when an incident occurs and the level of operations drops, the level of safety is preserved. One example is the compromise of the software loading process on board the aircraft. In this case, a detected incident followed by the decision to interrupt the software loading operations would preserve the existing level of safety.
The following Figure 1 depicts a conceptual framework that may be considered for the definition of the response and recovery objectives, including the recovery time. It represents, in the worst-case scenario, how the expected level of operational safety (safety level) for a process or an activity may vary over time when an information security incident occurs. In this scenario, the safety level is first reduced by the incident and then it degrades as long as the time passes. The figure also shows the expected effect that mitigating measuress and controls should have, respectively: in containing the operational safety drop as soon as an incident occurs, and in improving the recovery, i.e. the return to the expected safety level.
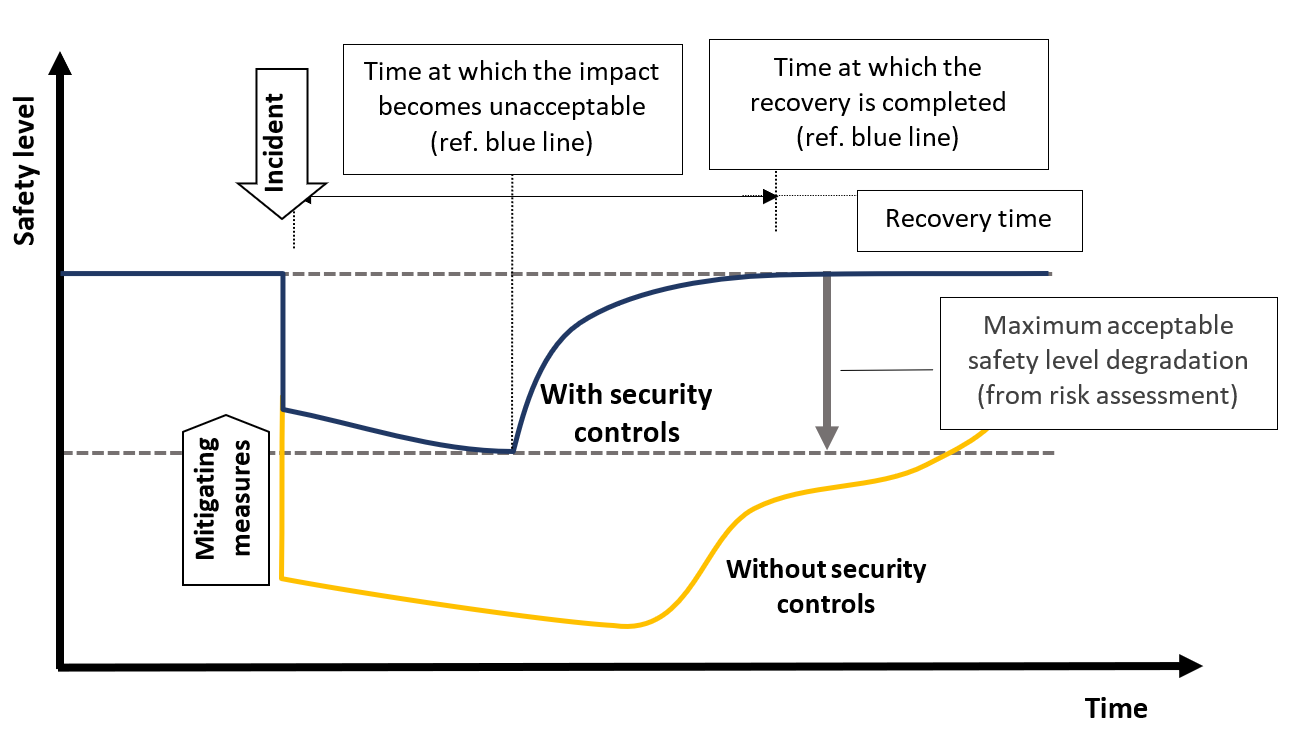
Figure 1: Conceptual framework for the definition of the response and recovery objectives
As mentioned, there might be different relations between the level of operations and safety that would lead to a different representation of the above figure. In certain cases, an incident may have a delayed effect on the safety level (e.g. a compromised development environment) as depicted in Figure 2, or it may have no impact if properly controlled, as in the case of the compromised software loading process mentioned before, which is depicted in Figure 3.
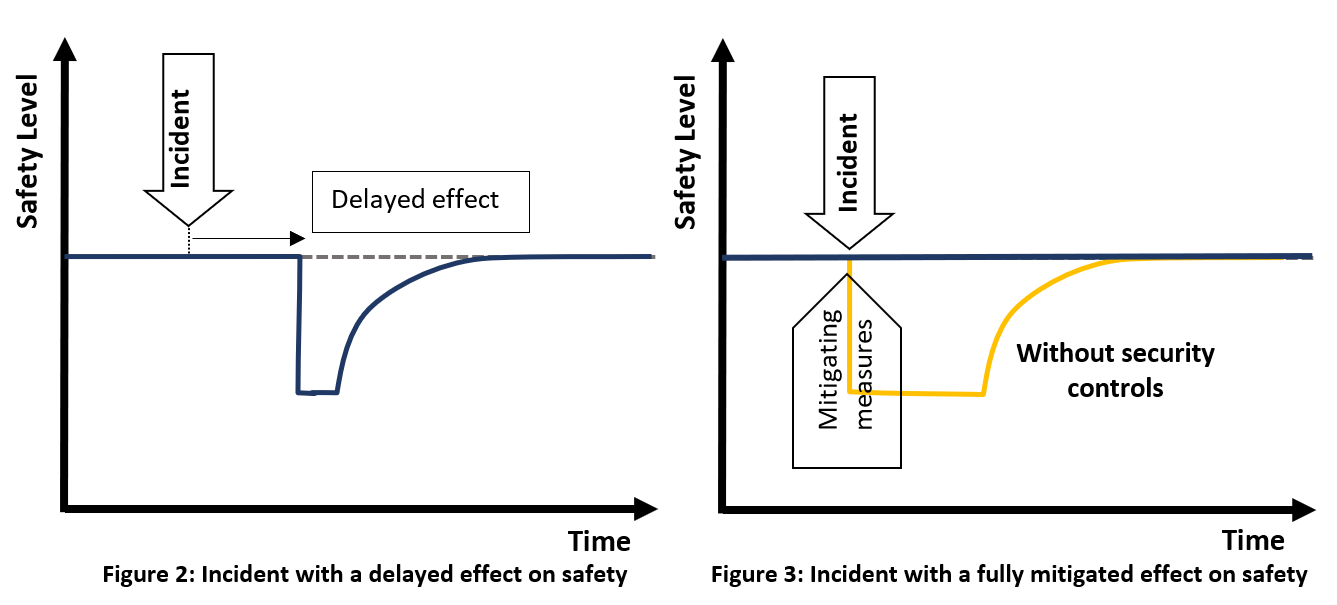
Moreover, it should be noticed that there might be different ways the same incident can be dealt with, since there are several factors that may affect safety.
In practical terms, the objectives for recovery time referred to in AMC1 IS.D.OR.220(c) may be expressed as a list of resources and services to be restored by order of priority, within the scope of the recovery. Guidance about objectives for recovery time can be found in EUROCAE ED-206, Chapter 7.3.5.
GM1 IS.D.OR.220(c) Information security incidents — detection, response and recovery
ED Decision 2023/009/R
A recovery procedure or recovery plan should describe incident recovery actions and the internal or external resources that are involved (e.g. staff, IT, buildings, providers). Guidance about incident recovery plan can be found in EUROCAE ED-206, Chapter 7 – Recover.
The resources required to apply the recovery measures should be available in order to implement the recovery actions in a timely manner after an incident has occurred. Those resources may be internally available or provided by contracted organisations as provided for in IS.D.OR.235. The contracting of recovery activities should be established before an incident occurs (proactive), and the contract should include provisions for the contracted party to react in a timely manner.
The return to a safe and secure state may initially require emergency measures, which are actions that are initiated based on the best information available at the time, before complete understanding of the situation is achieved and these measures can potentially degrade the level of service or functionalities. The return to a safe and secure state should be evaluated against the initial risk assessment and may only temporarily differ from the normal operational conditions. However, any increase of the residual risk and the duration of this risk increase, i.e. due to the implementation of emergency measures, should be documented and accepted at the right level of accountability.
The recovery activities mentioned here may also be the outcome of the response to incidents for which the organisation has received information that requires the implementation of adequate measures in order to react to information security incidents or vulnerabilities with a potential impact on aviation safety.
In such context the organisation may not have a process or a recovery plan covering the specific occurrence. Therefore, the definition from the organisation of a specific recovery plan and its approval by the competent authority is usually required.
IS.D.OR.225 Response to findings notified by the competent authority
Regulation (EU) 2022/1645
(a)After receipt of the notification of findings submitted by the competent authority, the organisation shall:
(1)identify the root cause or causes of, and contributing factors to, the non-compliance;
(2)define a corrective action plan;
(3)demonstrate the correction of the non-compliance to the satisfaction of the competent authority.
(b)The actions referred to in point (a) shall be carried out within the period agreed with the competent authority.
AMC1 IS.D.OR.225 Response to findings notified by the competent authority
ED Decision 2023/009/R
The compliance with IS.D.OR.225 should be managed as required for each organisation in the corresponding implementing regulation for the domain as identified in point Article 2(1) of Regulation (EU) 2022/1645 concerning the response to findings notified by the competent authority. The domain regulation may require the organisation to respond to the findings in accordance with their categorisation.
GM1 IS.D.OR.225 Response to findings notified by the competent authority
ED Decision 2023/009/R
The requirement for the categorisation of findings and the period within which the actions in IS.D.OR.225(a) should be performed can be found in the corresponding implementing regulation for the domain, under the authority requirements. For the opening of findings related to this Regulation, the competent authority will follow the above-mentioned requirement.
IS.D.OR.230 Information security external reporting scheme
Regulation (EU) 2022/1645
(a)The organisation shall implement an information security reporting system that complies with the requirements laid down in Regulation (EU) No 376/2014 and its delegated and implementing acts if that Regulation is applicable to the organisation.
(b)Without prejudice to the obligations of Regulation (EU) 376/2014, the organisation shall ensure that any information security incident or vulnerability, which may represent a significant risk to aviation safety, is reported to their competent authority. Furthermore:
(1)where such an incident or vulnerability affects an aircraft or associated system or component, the organisation shall also report it to the design approval holder;
(2)where such an incident or vulnerability affects a system or constituent used by the organisation, the organisation shall report it to the organisation responsible for the design of the system or constituent.
(c)The organisation shall report the conditions referred to in point (b) as follows:
(1)a notification shall be submitted to the competent authority and, if applicable, to the design approval holder or to the organisation responsible for the design of the system or constituent, as soon as the condition has been known to the organisation;
(2)a report shall be submitted to the competent authority and, if applicable, to the design approval holder or to the organisation responsible for the design of the system or constituent, as soon as possible, but not exceeding 72 hours from the time the condition has been known to the organisation, unless exceptional circumstances prevent this.
The report shall be made in the form defined by the competent authority and shall contain all relevant information about the condition known to the organisation;
(3)a follow-up report shall be submitted to the competent authority and, if applicable, to the design approval holder or to the organisation responsible for the design of the system or constituent, providing details of the actions the organisation has taken or intends to take to recover from the incident and the actions it intends to take to prevent similar information security incidents in the future.
The follow-up report shall be submitted as soon as those actions have been identified, and shall be produced in the form defined by the competent authority.
GM1 IS.D.OR.230 Information security external reporting scheme
ED Decision 2023/009/R
Organisations are required to report occurrences to their competent authority.
EXAMPLES
Design organisations approved by EASA: EASA is the competent authority.
Air operators certified by the competent authority of a Member State: the competent authority of the Member State is the competent authority.
SPECIAL CASES
In a situation where an organisation has two air operator certificates (AOCs) under two different EU Member States (State A and B), the occurrences involving aircraft operating under the State A AOC have to be reported to the State A competent authority, instead the occurrences involving aircraft operating under the State B AOC have to be reported to the State B competent authority.
For organisations holding multiple approvals, the reporting will be done to the competent authority of the approved part of the organisation where the incident has occurred, or the vulnerability has been discovered. In case the incident/vulnerability affects multiple approvals, the reporting will be done to all the competent authorities.
For organisations holding an approval but operating outside the EU (e.g. Part-145), EASA is the competent authority and they have to report to the Agency.
Dual-use aircraft — a vulnerability may need to be reported through both the military and civil reporting systems if it affects a dual-use function/system. Information reported through the civil reporting system should be sanitised (i.e. all sensitive information should be properly removed).
AMC1 IS.D.OR.230(a)&(b) Information security external reporting scheme
ED Decision 2023/009/R
In order to comply with the provisions under IS.ID.OR.230 (a) and (b), the organisation should report:
(a)any occurrence covered by Regulation (EU) No 376/2014 that originated from intentional unauthorised electronic interactions;
(b)information security incidents having a potential significant risk to aviation safety not covered under Regulation (EU) No 376/2014;
(c)vulnerabilities that pose a significant risk to aviation safety and are not yet adequately mitigated in accordance with an approved vulnerability management strategy (see AMC1 IS.D.OR.220(b)).
From the aforementioned reports, it is the responsibility of the competent authorities under Part-IS to ensure compliance with Article 7 of this Regulation and to submit any relevant information that needs to be shared with the information security competent authorities designated under Article 8 of Directive (EU) 2016/1148.
GM1 IS.D.OR.230(a)&(b) Information security external reporting scheme
ED Decision 2023/009/R
RELATION BETWEEN IS.D.OR.230(b) AND REGULATION (EU) No 376/2014
Regulation (EU) No 376/2014 of the European Parliament and of the Council lays down requirements on the reporting, analysis and follow-up of occurrences in civil aviation. Compliance with point IS.D.OR.230(b) does not exempt organisations from compliance with Regulation (EU) No 376/2014.
For each category of reporter, Regulation (EU) No 2015/1018 defines the nature of items to be mandatorily reported. Regulation (EU) No 376/2014 also considers voluntary reporting of other items that are perceived by the reporter as a threat to aviation safety.
Furthermore, compliance with Regulation (EU) No 376/2014 does not exempt organisations from compliance with point IS.D.OR.230(b). However, this should not give rise to two parallel reporting systems, and point IS.D.OR.230(b) and Regulation (EU) No 376/2014 should be seen as complementary in that respect.
In practice, this means that reporting obligations under point IS.D.OR.230(b) on the one hand and reporting obligations under Regulation (EU) No 376/2014 on the other hand are compatible. These reporting obligations may be discharged using one reporting channel. In addition, any natural or legal person that has more than one role subject to the obligation to report may discharge all those obligations through a single report. Organisations are encouraged to properly describe this in their organisation manual, to address cases in which the responsibilities are discharged on behalf of the organisation.
FOLLOW-UP ANALYSIS
When the analysis of an occurrence reported under Regulation (EU) No 376/2014 later identifies that the root cause of, or the contributing factor to, the occurrence was an intentional unauthorised electronic interaction, the organisation should update its notification to the competent authority.
SIGNIFICANT RISK TO AVIATION SAFETY
In line with the definition of occurrence under Article 2(7) of Regulation (EU) No 376/2014 any information security incident or vulnerability, which may represent a significant risk to aviation safety should be considered a reportable occurrence. Significant risk to aviation means unsafe condition, i.e. one that can result in an accident or a serious incident (as defined in ICAO Annex 13).
Note: When assessing the possibility that the effects of an information security incident could lead to an unsafe condition, the organisation should consider the combination of effects if the incident involves multiple systems; indeed, some assumptions about system independence that may be valid for fortuitous occurrences may be violated by deliberate acts.
RELATION BETWEEN IS.D.OR.230(b)(1) AND OTHER REPORTING REQUIREMENTS OF information security occurrences RELATED TO AVIATION PRODUCTS OR PARTS
For organisations subject to reporting requirements of information security occurrences related to aviation products or parts, compliance with the specific provisions in the implementing regulation for their domain is considered sufficient to achieve compliance with the requirement in point IS.D.OR.230(b)(1). For example, for organisations subject to Regulation (EU) No 748/2012, the reporting can be done in accordance with point 21.A.3A of Annex I (Part 21) to that Regulation.
AMC1 IS.D.OR.230(c) Information security external reporting scheme
ED Decision 2023/009/R
Within the overall limit of 72 hours the degree of urgency for submission of a report should be determined by the level of the safety impact judged to have resulted from the information security incident or discovered vulnerability. Where an occurrence is judged by the person identifying the possible unsafe condition to have resulted in an immediate and particularly significant hazard, the competent authority expects to be advised immediately and by the fastest possible means (telephone, fax, email, telex, etc.) of whatever details are available at that time.
GM1 IS.D.OR.230(c) Information security external reporting scheme
ED Decision 2023/009/R
Guidance regarding the reporting of information security incidents and vulnerabilities can be found in EUROCAE ED-206, Chapter 6.4.2.2 — Reporting timeline and Chapter 6.4.5 — Reporting information content. This is not the only source where guidance can be found, and the organisation may refer to different guidance more appropriate for their application.
Note: The person reporting an occurrence under Regulation (EU) No 376/2014 may not have the capability to determine the nature of the occurrence. This is particularly true for information security and the result can come from forensic analysis that determines the information security nature of the occurrence. The evaluation will be done as part of the initial internal reporting process (see IS.D.OR.215 and related AMC). The evaluation of the occurrence can demonstrate the possibility that it materialises into an unsafe condition taking into account the likelihood of realisation.
IS.D.OR.235 Contracting of information security management activities
Regulation (EU) 2022/1645
(a)The organisation shall ensure that when contracting any part of the activities referred to in point IS.D.OR.200 to other organisations, the contracted activities comply with the requirements of this Regulation and the contracted organisation works under its oversight. The organisation shall ensure that the risks associated with the contracted activities are appropriately managed.
(b)The organisation shall ensure that the competent authority can have access upon request to the contracted organisation to determine continued compliance with the applicable requirements laid down in this Regulation.
GM1 IS.D.OR.235 Contracting of information security management activities
ED Decision 2023/009/R
Organisations may decide to outsource certain activities to suppliers, both for their own operational needs and for the purpose of complying with this Regulation (information security management activities). Activities contracted for operational needs may fall within the scope of Part-IS and therefore the relevant information security risks have to be managed in accordance with the requirements in points IS.D.OR.205 and IS.D.OR.210. Instead, information security management activities are subject to the specific provisions of IS.D.OR.235 because matters relating to these activities can have a major impact on the organisation.
Therefore the objectives of point IS.D.OR.235 are:
(a)to protect critical and sensitive information and assets when being handled by organisations contracted for the provision of information security management activities (including organisations in the supply chain) at either their facilities or the organisation facilities, or when being transmitted between the organisation and contracted organisations, or being remotely accessed by contracted organisations;
(b)to prevent information security risks from being introduced through products and services developed or provided by the contracted organisations to the organisation, in the frame of the provision of information security management activities;
(c)to ensure that information security risks are managed throughout all the stages of the relation with the contracted organisations.
GM2 IS.D.OR.235 Contracting of information security management activities
ED Decision 2023/009/R
(a)The contracting of information security management activities is a means to allocate tasks from the contracting organisation to third parties (contracted organisations). The contracting organisation remains responsible for the oversight of the contracted organisation(s) and accountable for compliance with this Regulation.
(b)A contract could take the form of a written agreement, letter of agreement, service letter agreement, memorandum of understanding, etc. as appropriate for the contracted activities.
