Filters
Appendix V — Proportionality considerations related to safety relevance and aspects of complexity
ED Decision 2025/014/R
The following is a non-exhaustive, non-binding, list of activities related to the implementation of the ISMS under this Regulation. These activities are proposed in association with a set of indicators, with activities suggested at the lower and upper ends of the scale. Organisations are encouraged to assess their own level for each indicator, selecting or adapting the proposed activities based on their specific information security risks and organisational context. This approach helps to keep the activities proportionate to the overall safety relevance and complexity of the organisation.
Indicator of the degree of safety relevance: the organisation’s role in the functional chain, and number and criticality of interfacing organisations
The organisation’s role in the functional chain and its overall contribution to the safety of related functional processes are key indicators of safety relevance. This should impact the depth of risk assessment required and the level of assurance needed to ensure the effectiveness of measures implemented to mitigate unacceptable risks.
Low safety relevance: organisations whose role in the functional chain and their interfaces do not pose a risk of unsafe conditions.
The following approach may be adopted:
Risk assessment and treatment
—Simplified risk assessment: A streamlined risk assessment process that prioritises risks based on their potential impact on safety is used. The assessment focuses on high-impact areas; more detailed assessments are performed only where and if necessary.
—Risk treatment prioritisation: A risk treatment plan that prioritises high-impact risks with costeffective measures is adopted. In such cases, cost-effective controls that reduce risks to acceptable levels may be used. These controls can often leverage existing processes, physical controls or technology.
High safety relevance: organisations whose role in the functional chain and their interfaces may pose a risk of unsafe conditions
The following approach may be adopted:
Risk assessment and treatment
Detailed risk assessments: Detailed and often more frequent risk assessments are carried out for those elements that have been identified as having a relevant safety impact, i.e. an unsafe condition.
Indicator of complexity 1: complexity of the organisational structure and hierarchies
The complexity of an organisation’s structure — typically determined by the number of staff, departments and hierarchical layers — directly influences the level of internal coordination required and the extent to which information exchange needs to be formalised and proceduralised.
Low complexity: organisations characterised by a combination of limited number of staff members, few hierarchical layers and departments
The following approaches may be adopted:
(a)Policy and procedure simplification
—Streamlined documentation: Policies and procedures can be concise, clear and easy to read. Documents are kept short and simple to make them easily understandable. Templates can be used in order to expedite the creation of the necessary documentation.
—Focus on key policies: During the development, the key policies have been prioritised in order to address the most critical aspects of information security, such as management commitment, access control and incident response.
(b)Employee training and awareness
—Targeted training programmes: Focused training programmes that target the specific roles and responsibilities of employees are provided. The training is relevant to the organisation’s specific risks and operational context.
—Security culture: A culture of information security awareness is encouraged throughout the organisation. Short training sessions and awareness campaigns are conducted on a regular basis.
(c)Outsourcing and partnerships
—Outsourcing: For areas where the organisation lacks expertise, outsourcing to providers of managed-security services is adopted.
—Collaboration with peers: Information-sharing with similar organisations (e.g. through the European Centre for Cyber Security in Aviation (ECCSA)) or industry groups is carried out. Collaboration provides insights to evaluate the evolution of the security environment with limited effort.
(d)Engagement with management
Simplified management reporting: Reports to management are concise and focused on key metrics that demonstrate the effectiveness of the ISMS. Continued support and resource allocation from top management is ensured.
(e)Compliance monitoring and continuous improvement
—Regular but scaled audits: Internal audits are regularly conducted, but the effort is scaled to the organisation’s size and complexity. The focus is on the most critical areas and the audit results are provided to the accountable manager or the head of the design organisation and utilised to guide continuous improvement.
—Agile review process: The ISMS is regularly reviewed and, if necessary, adapted to ensure that it remains aligned with the organisation’s evolving needs and threats.
High complexity: organisations characterised by a combination of large number of staff members, hierarchical layers and departments and interfaces
The following approaches may be adopted:
(a)Robust governance structure
—Information security governance: Governance implementation to oversee the ISMS are present. This is to ensure alignment with the organisation’s safety and security objectives. This governance should operate through formal committees or working groups that include representatives from senior management, safety, information technology, legal and key business units.
—Metrics and reporting: Comprehensive metrics and reporting structures to track the effectiveness of the ISMS are implemented. Report on key performance indicators (KPIs) to senior management and the management board are provided to ensure ongoing support and resource allocation.
(b)Extensive policy and procedure framework
—Detailed policies and procedures: Although streamlined documentation is still the overall objective, more complex organisations may require a broader range of policies and procedures to cover different business units and departments, compliance requirements and operational processes.
—Policy harmonisation: Policies are harmonised across the organisation to avoid conflicting practices between different departments or regions. This requires a centralised governance model to oversee policy development and enforcement.
(c)Risk assessment and treatment
—Cross-risk assessments: Cross-risk assessments include assessing risks across various departments, geographic locations and technological platforms.
—Risk aggregation and correlation: With a larger volume of information, risks assessments are aggregated and correlated to identify systemic issues and ensure that risks are managed and escalated at an organisational level, not just within individual silos.
(d)Comprehensive training and awareness programmes
—Role-based training: Extensive role-based training programmes tailored to different functions within the organisation are implemented. For example, IT staff, executives and end-users all have different levels of training specific to their roles.
—Continuous security awareness campaigns: Security awareness campaigns using various methods (e.g. phishing simulations, workshops and e-learning modules) are continuously deployed to keep security top-of-mind for all employees across the organisation.
(e)Enhanced contracted activities management
—Supply chain risk management: Thorough information security assessments of contracted organisations and ongoing monitoring of third-party risks are carried out. Information security requirements are integrated into contracts.
(f)Comprehensive incident management
—Security monitoring and incident response capability: In order to monitor security events around the clock, manage incidents and coordinate response efforts across the organisation, structured security operations are established. Depending on the organisation's resources, this can be achieved through a dedicated security operations centre (SOC), a virtual SOC, managed security services or other appropriate solutions that ensure effective coverage.
—Complex incident response plans: Detailed incident response plans that cover a variety of scenarios, including cross-departmental coordination, communication strategies and operational continuity planning are developed and maintained.
—Crisis simulation exercises: Crisis simulation exercises that involve key stakeholders across the organisation are regularly conducted to test the effectiveness of incident response and operational continuity plans.
(g)Continuous improvement and compliance monitoring programmes
—Internal audits: Comprehensive internal audits are regularly conducted to assess compliance with the ISMS and identify areas for improvement.
—Audits of contracted organisations: To ensure compliance with the organisation’s security and safety objectives, audits of contracted organisations are conducted at a frequency proportionate to the relevance of the contracted activities to security and safety. Using the results of existing relevant audits is also encouraged to reduce the burden.
—Continuous improvement programmes: A continuous improvement process to update and refine the ISMS based on audit findings, incident post-mortems and changes in the threat landscape is implemented.
Indicator of complexity 2: complexity of the ICT systems and data used by the organisation
The complexity of the information and communication technology systems and data used by the organisation, and their connection to external parties, directly influences the level of customisation and tailoring required for risk management and incident detection, response and recovery.
Low complexity: organisations characterised by a combination of usage of a few ICT tools and utilisation of standard ICT products
The following approaches may be adopted:
(a)Use of standards and tools
—Leverage ISO/IEC 27001:2022 controls as a baseline: ISO/IEC 27001:2022 Annex A provides a catalogue of controls that are selected based on the results of the risk assessment. Similarly, NIST SP 800-53 offers a comprehensive set of controls that can be adapted to specific threats and operational requirements. Aligning control selection with risk assessment outcomes ensures that the controls are suitable for the specific threats and vulnerabilities identified, while reducing the effort involved in designing controls from scratch. Additionally, using the controls as a checklist helps to ensure that critical areas are addressed. To ensure full alignment with aviation-specific information security requirements under Part-IS, it is also recommended to consult the Part-IS versus ISO/IEC 27001:2022 comparison guide.
—Simplified incident management: A basic incident management process that allows for quick identification, reporting and response to security incidents is adopted. Lessons learned from incidents are in any case integrated into the ISMS for continuous improvement.
—Automated tools: Automated tools for monitoring, logging and managing security incidents are used in order to reduce manual effort while maintaining continuous compliance.
(b)Documentation and record-keeping
—Essential records: Only records that are essential to demonstrate compliance and the effectiveness of the ISMS are kept. Excessive documentation that does not add value or is burdensome to maintain is avoided.
—Use of digital solutions: Digital tools are used for document management to simplify access and version control, and to ensure the security of records.
High complexity: organisations characterised by a combination of usage of several and diverse ICT tools, amongst which bespoke ICT solutions
The following approaches may be adopted:
(a)Advanced security technologies
—Integration of advanced security tools: Security technologies like security information and event management (SIEM), data loss prevention (DLP), and endpoint detection and response (EDR) systems are utilised to help manage the scale and complexity of monitoring, detecting and responding to security incidents across the organisation.
—Automated threat intelligence: Automated threat intelligence platforms are used to enable real-time threat detection and response across the broad threat surface.
(b)Documentation and record-keeping
—Detailed documentation: Extensive documentation of all ISMS processes, risk assessments, incident reports and compliance activities is carried out.
—Record retention: Records and data are widely collected, retained and securely stored, and are accessible over extended periods.
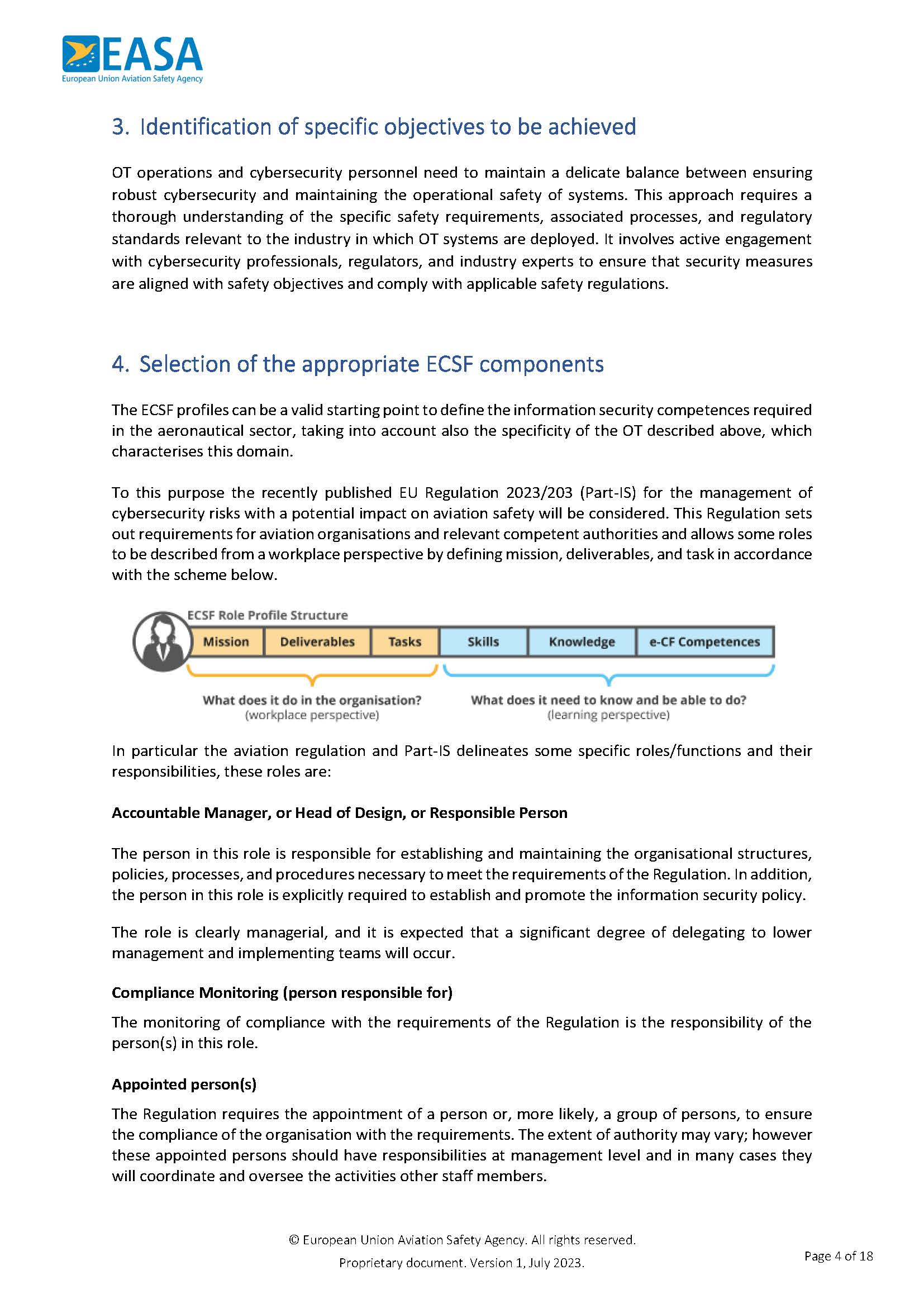
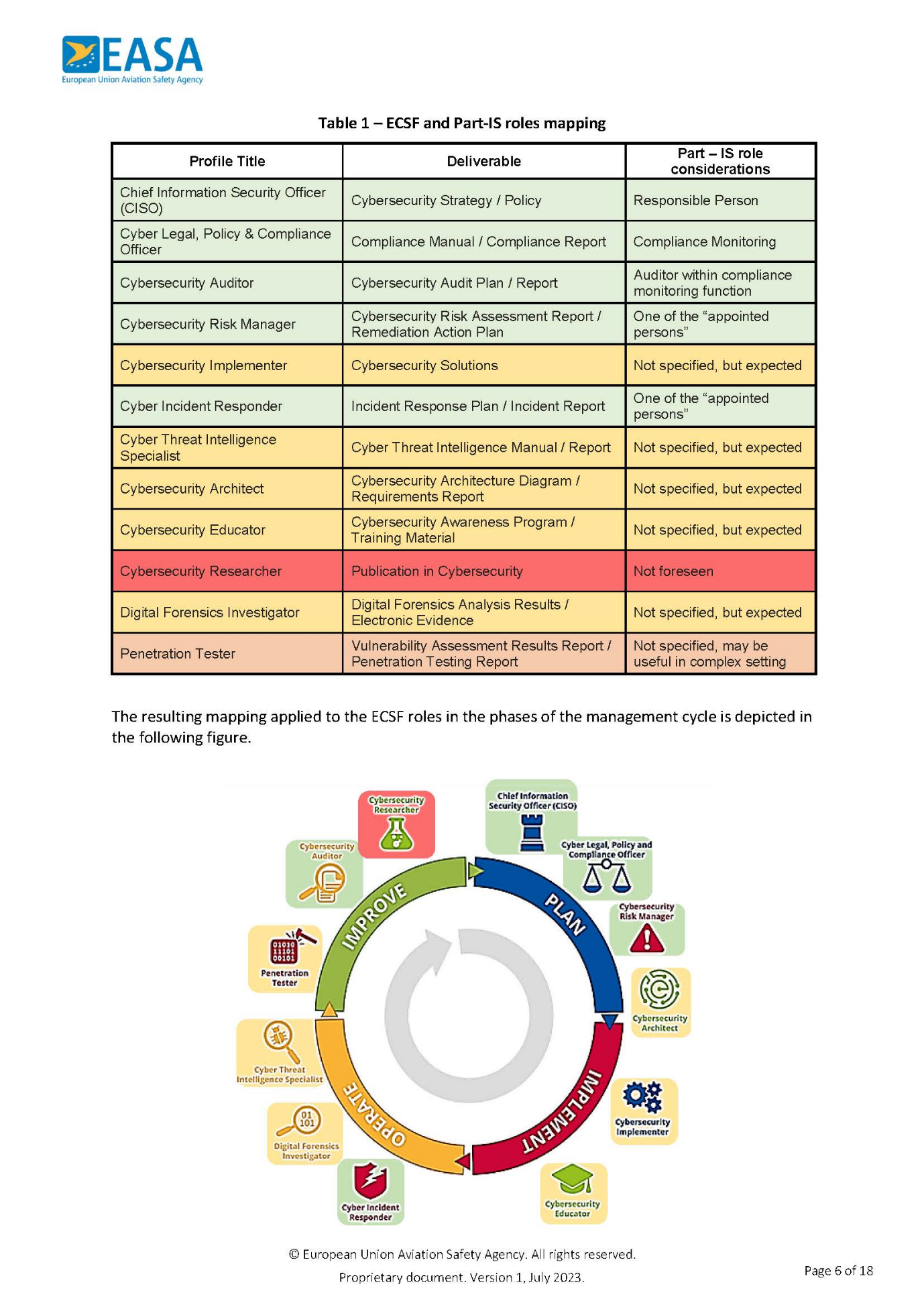
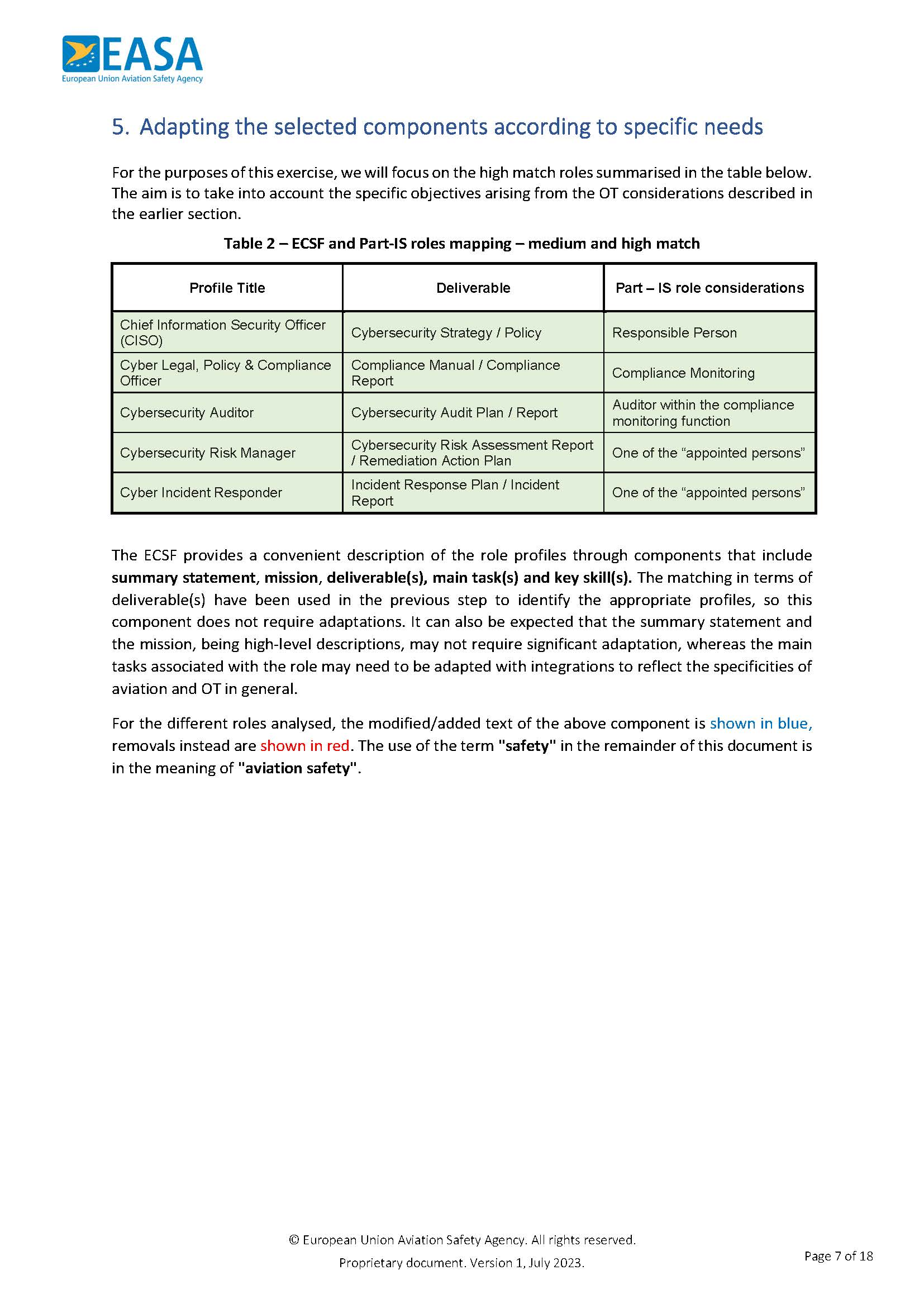
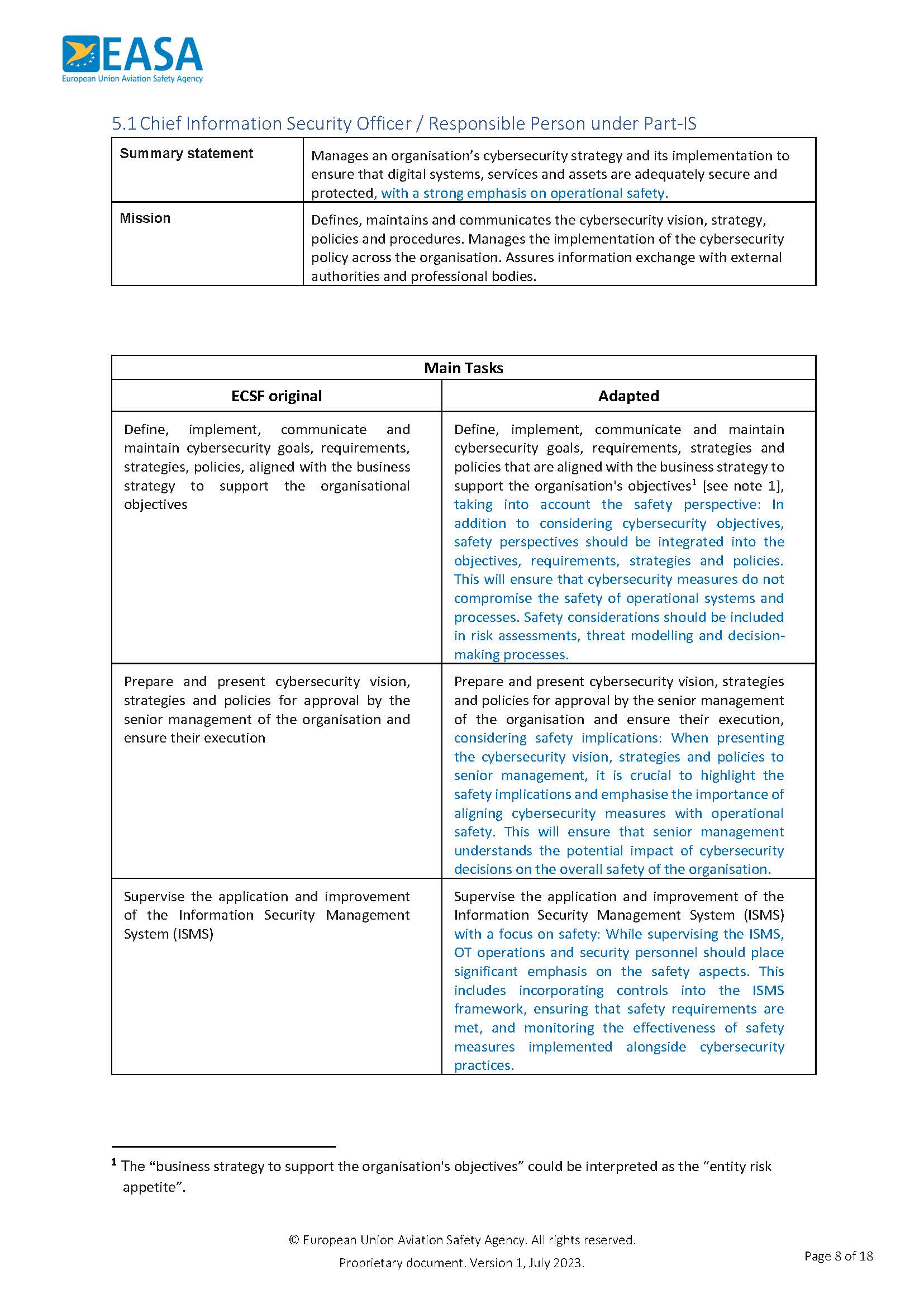
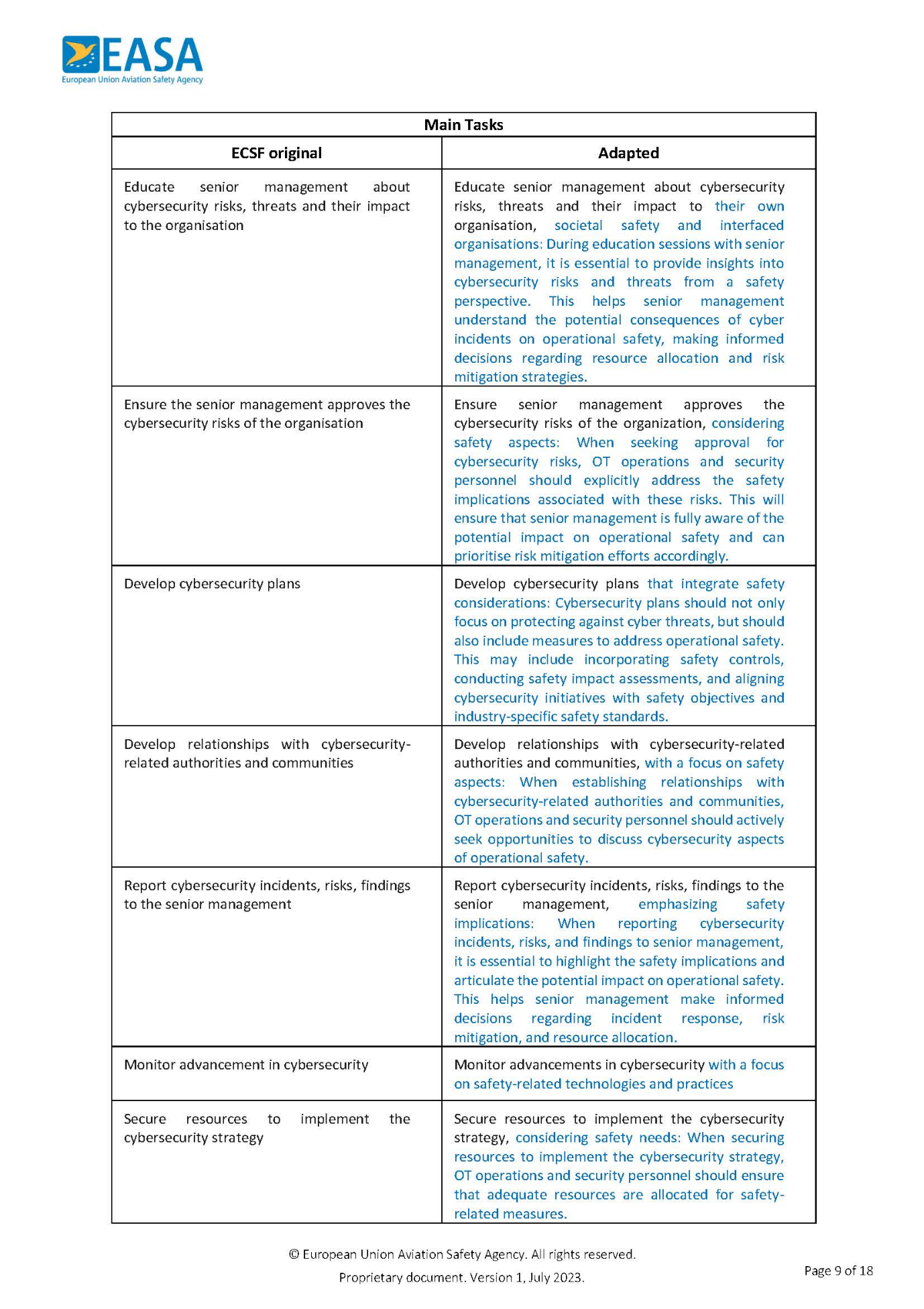
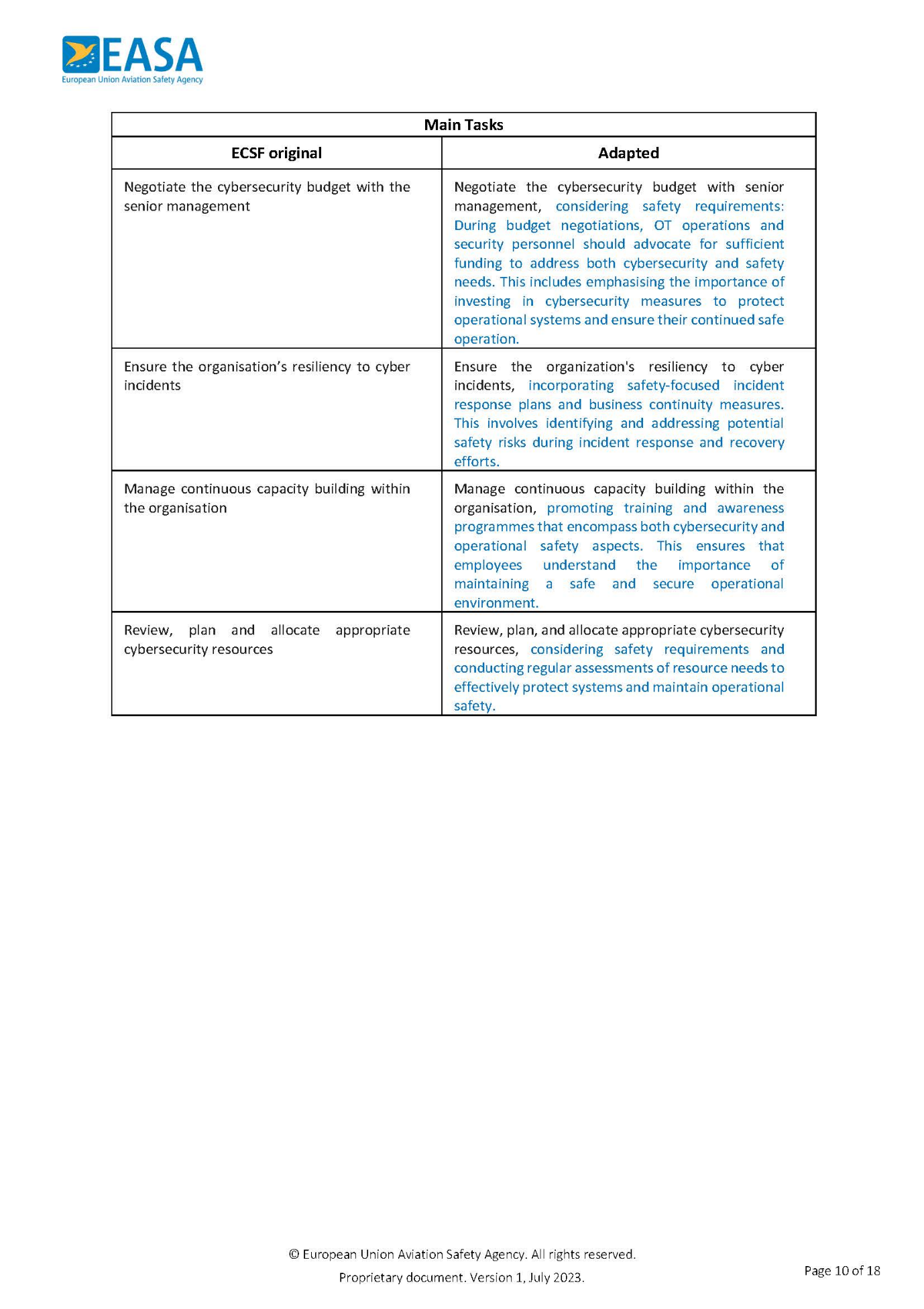
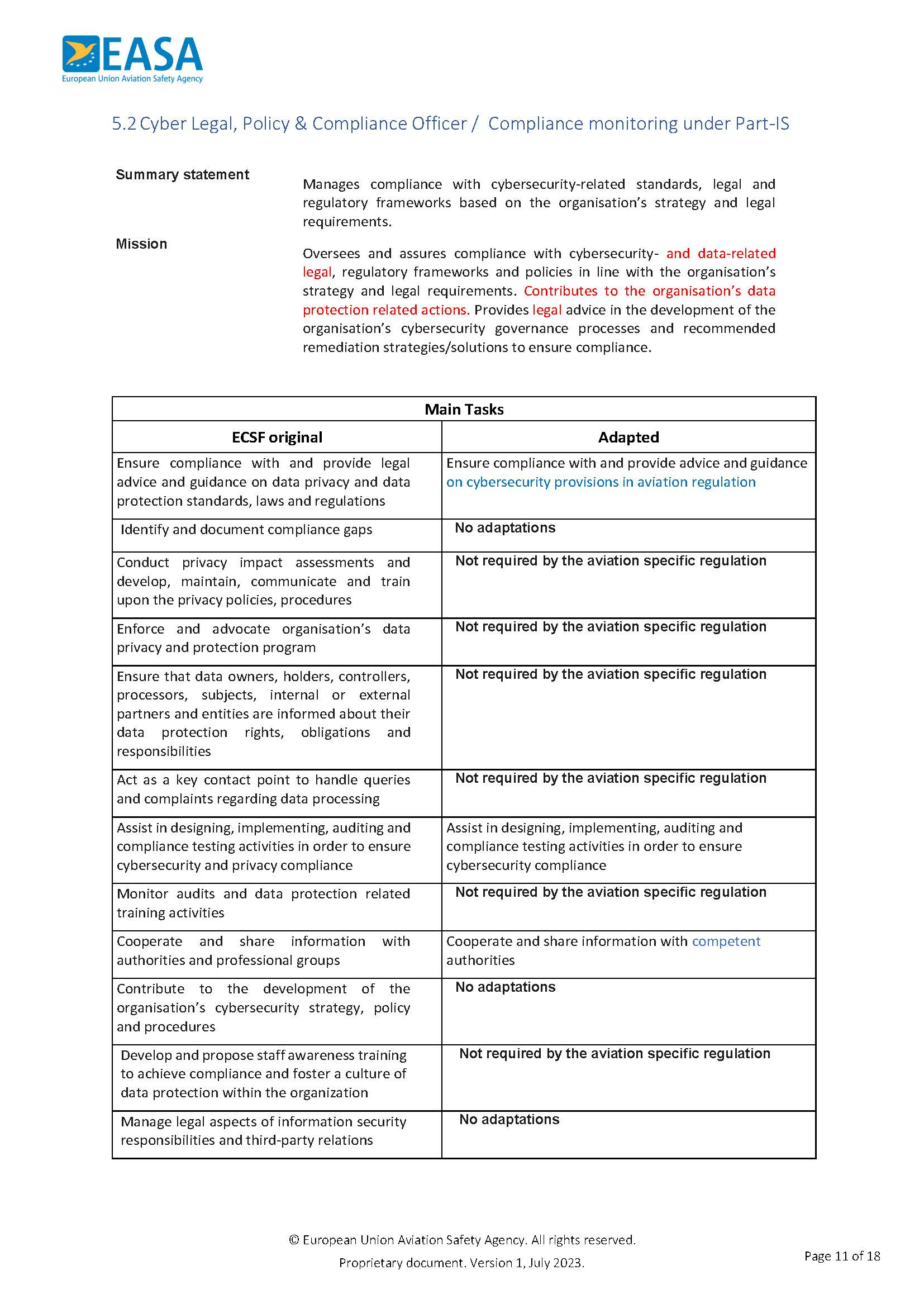
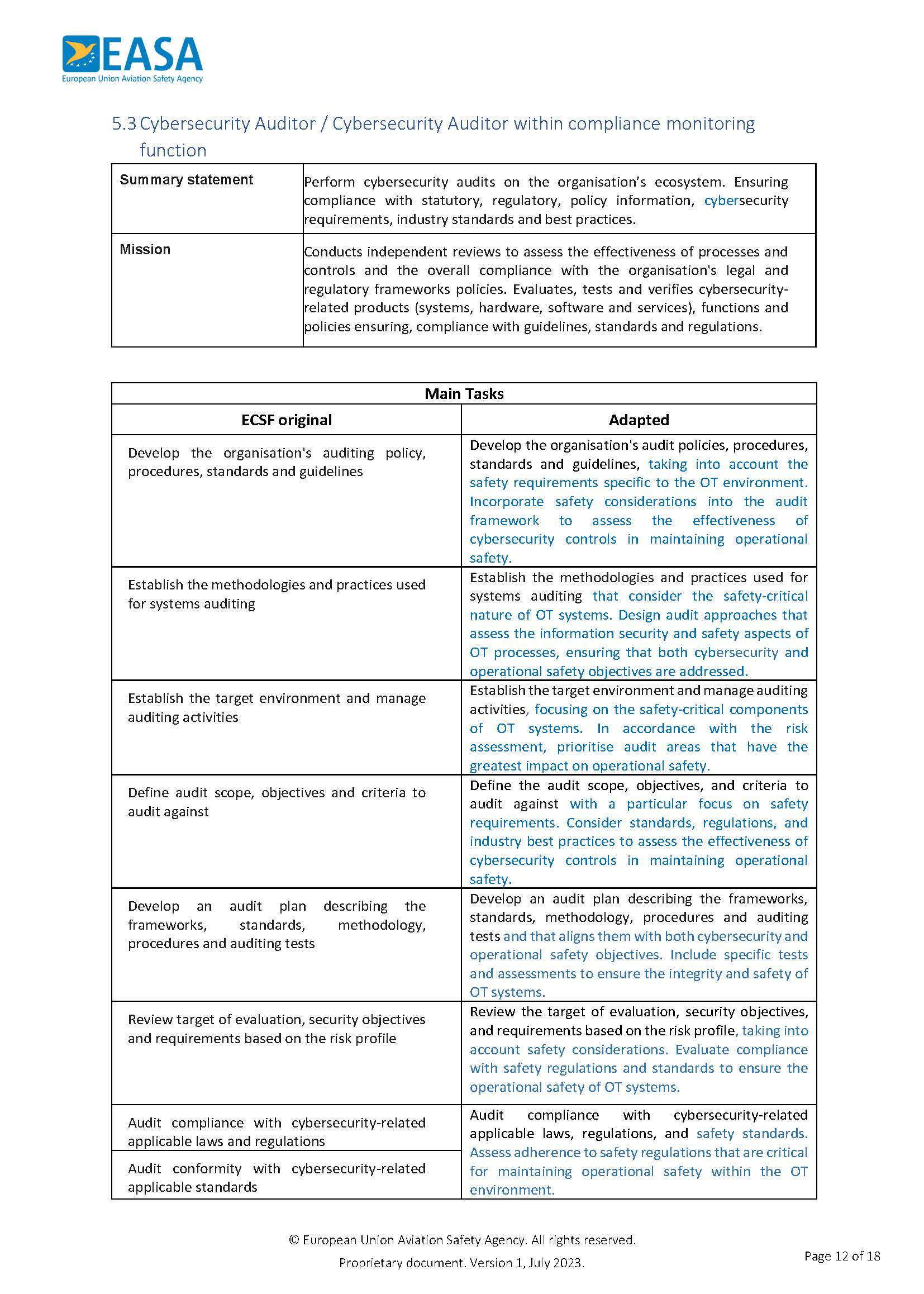
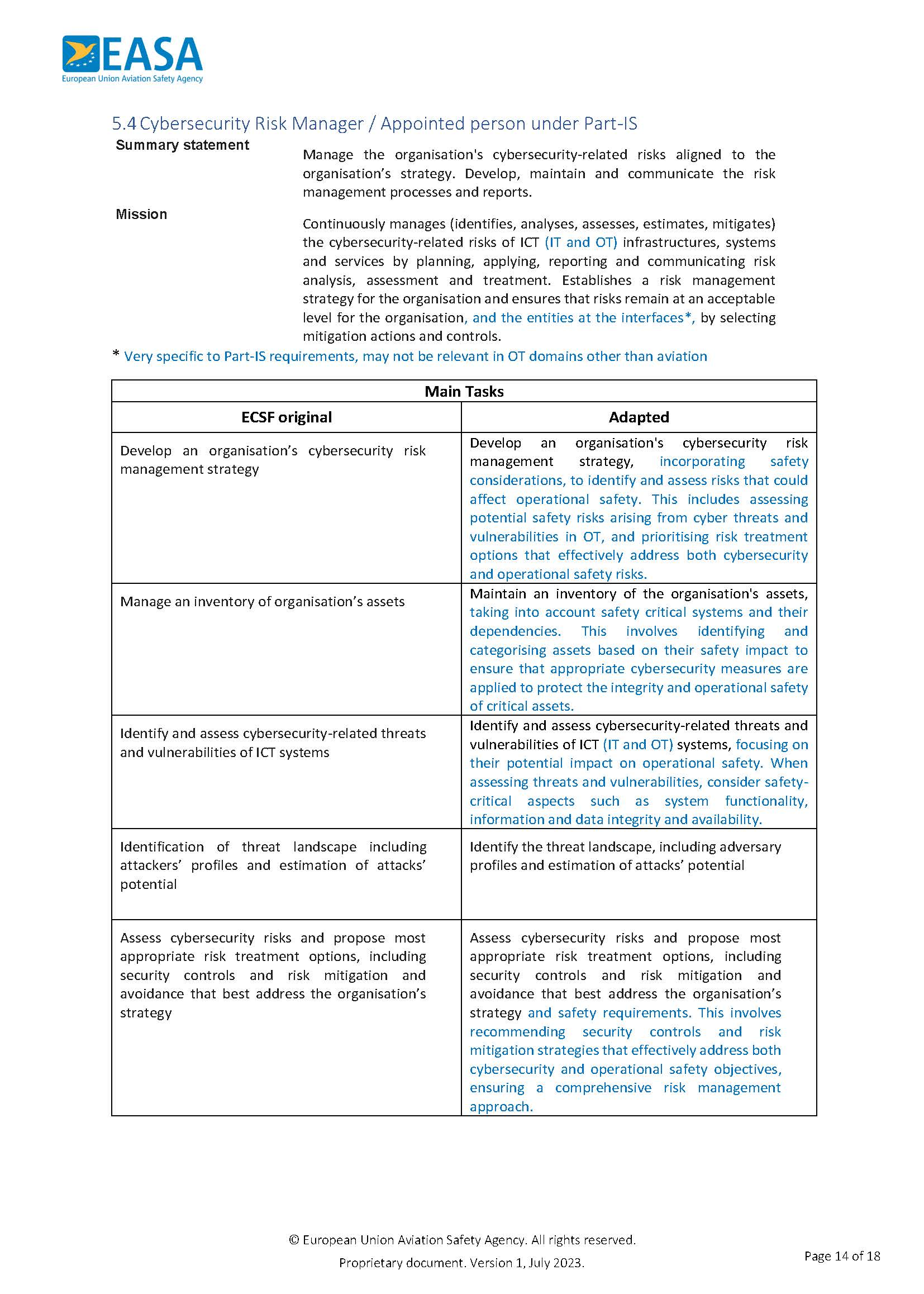
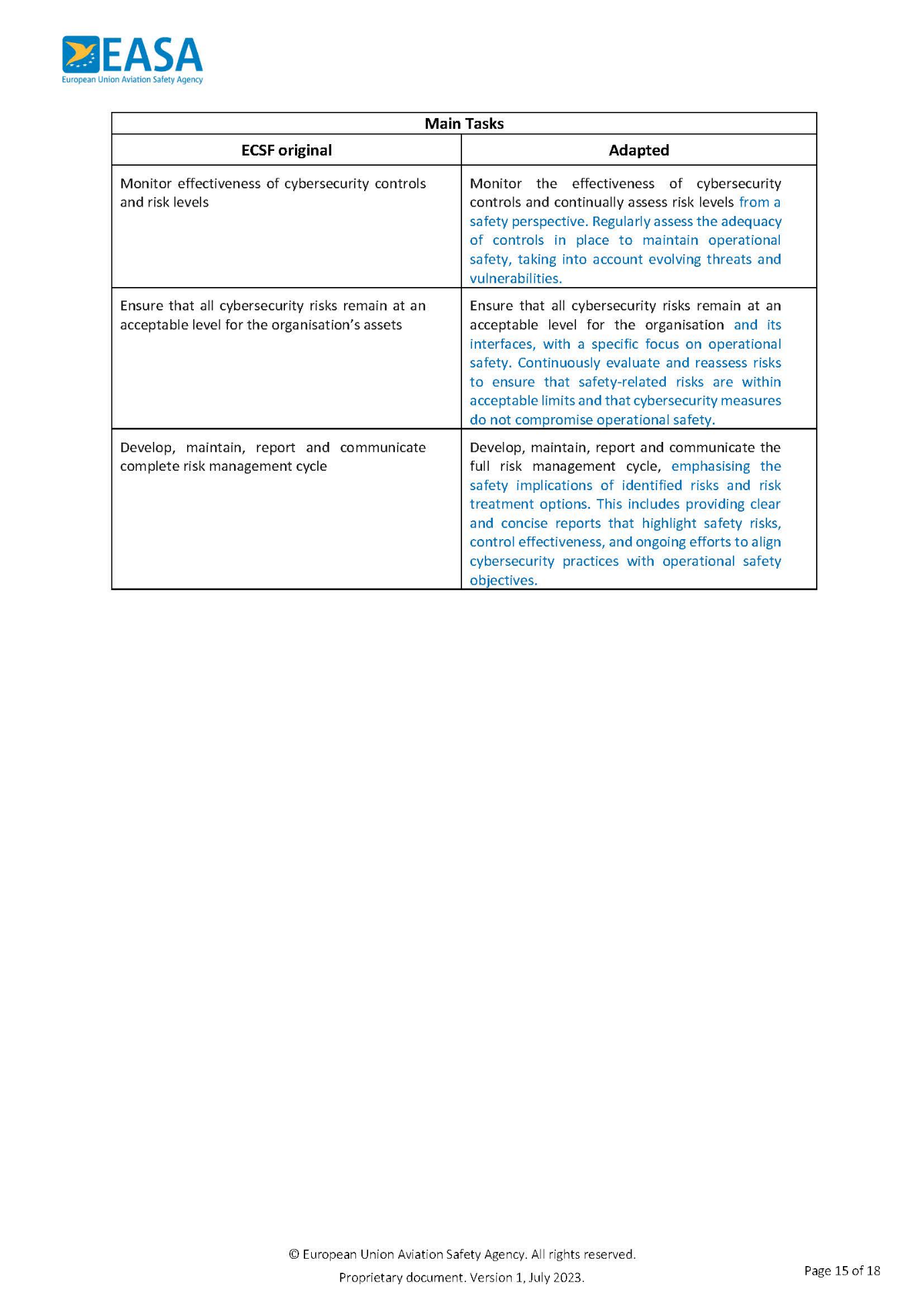
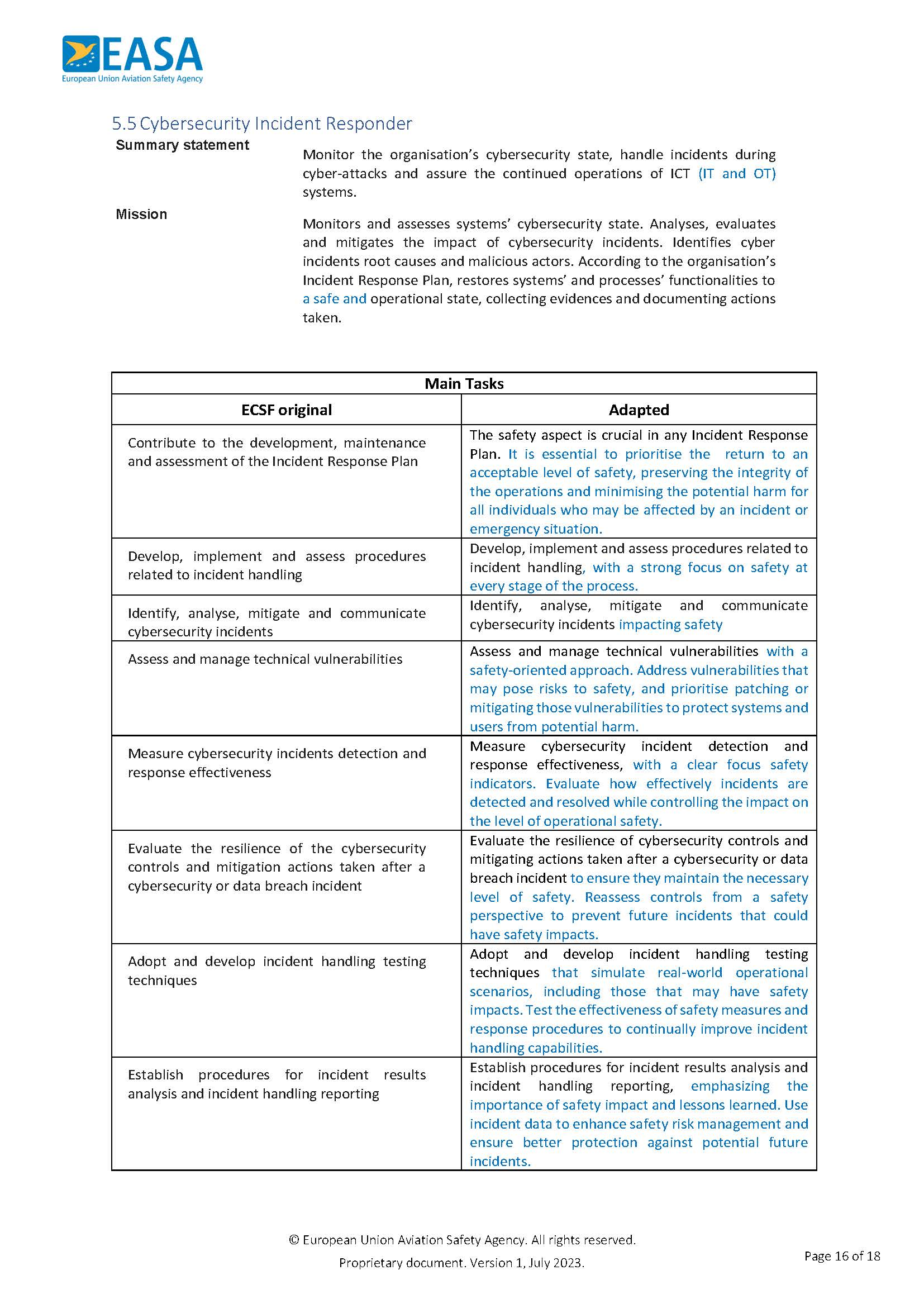
Appendix VI — Adaptation of the EU Cybersecurity Skills Framework (ECSF)
ED Decision 2025/014/R