Filters
Appendix II — Main tasks stemming from the implementation of Part-IS mapped to the EU e-CF and the NIST CSF 2.0
ED Decision 2025/014/R
Part-IS main task | Activity type | Reference | ||
Management, | Part-IS | EU e-CF | NIST CSF 2.0 | |
Competence areas & skills | Functions & categories | |||
Establish and operate an information security management system (ISMS) | Management | IS.D.OR.200(a) | ISM (E.08) | GV – Govern |
Establish the scope of the ISMS in accordance with Part-IS requirements | Management | IS.D.OR.205(a) | ISM (E.08) | GV.RM – Risk Management Strategy; |
Implement and maintain an information security policy | Management | IS.D.OR.200(a)(1) | ISM (E.08) | GV.PO – Policy |
Identify and review information security risks | Management | IS.D.OR.200(a)(2) | ISM (E.08), Risk Management (E.02) | GV.SC – Cybersecurity Supply Chain Risk Management; |
Implement information security risk treatment measures | Management | IS.D.OR.200(a)(3) | ISM (E.08), Risk Management (E.02) | ID.RA – Risk Assessment |
Set up measures to detect information security events, identify those that may develop to incidents with a potential impact on aviation safety, and respond to, and recover from, such incidents | Management | IS.D.OR.200(a)(5) | Incident Management (C.04) | DE – Detect; |
Implement measures that have been notified by the competent authority | Operational | IS.D.OR.200(a)(6) | ||
Take appropriate remedial actions to address findings notified by the competent authority (non-compliances) | Both | IS.D.OR.200(a)(7) | ||
Implement an external information security reporting scheme | Management | IS.D.OR.200(a)(8) | Incident Management (C.04) | RS.CO – Incident Response Reporting and Communication; |
Monitor compliance with this Regulation and report findings to top management | Operational | IS.D.OR.200(a)(12) | Compliance (E.09) | GV.RR – Roles, Responsibilities and Authorities; |
Protect confidentiality of exchanged information | Operational | IS.D.OR.200(a)(13) | Information Security Management (E.08) | PR.DS – Data Security; |
Implement and maintain a continuous improvement process to measure the effectiveness and maturity of the ISMS and strive to improve it | Management | Information Security Management (E.08) | GV.OV – Oversight; | |
Document and maintain all key processes, procedures, roles and responsibilities | Management | IS.D.OR.200(c) | ISM (E.08), Compliance (E.09) | GV.RR – Roles, Responsibilities and Authorities; |
Identify all elements which could be exposed to information security risks | Management | IS.D.OR.205(a) | Risk Management (E.02) | ID.AM – Asset Management |
Identify the interfaces with other organisations which could result in exposure to information security risks | Management | IS.D.OR.205(b) | Risk Management (E.02), Business Change Management (E.07) | ID.AM – Asset Management; |
Identify information security risks and assign a risk level | Management | IS.D.OR.205(c) | Risk Management (E.02) | GV.RM – Risk Management Strategy; |
Review and update the risk assessment based on certain criteria | Operational | IS.D.OR.205(d) | Risk Management (E.02) | GV.RM – Risk Management Strategy; |
Develop and implement measures to address risks and verify their effectiveness | Operational | IS.D.OR.210(a) | Risk Management (E.02) | GV.RM – Risk Management Strategy; |
Communicate the outcome of the risk assessment to management, other personnel and other organisations sharing an interface | Operational | IS.D.OR.210(b) | Risk Management (E.02), ISM (E.08) | GV.RM – Risk Management Strategy; |
Establish an internal information security reporting scheme to enable the collection and evaluation of information security events from personnel | Management | IS.D.OR.200(a)(4) | Incident Management (C.04) | ID.RA – Risk Assessment; |
Ensure that contracted organisations report information security events | Management | IS.D.OR.215(c) | Supplier Relationship Management (E.10) | GV.SC – Cybersecurity Supply Chain Risk Management; |
Analyse internally reported occurrences to identify information security events, incidents, and vulnerabilities | Operational | IS.D.OR.215(b)(1)–(b)(3) | Incident Management (C.04) | DE.AE – Adverse Event Analysis |
Implement measures to detect in processes and operations information security events which may have a potential impact on aviation safety | Operational | IS.D.OR.220(a) | ISM (E.08) | DE.CM – Continuous Monitoring; |
Implement measures to respond to information security events that may cause an information security incident | Operational | IS.D.OR.220(b) | Incident Management (C.04) | RS.MA – Incident Management; |
Cooperate on investigations with other organisations that contribute to the information security of its own activities | Management | IS.D.OR.215(d) | Incident Management (C.04), Legal Advice and Compliance (E.09) | DE.CM – Continuous Monitoring; |
Implement measures to recover from information security incidents | Operational | IS.D.OR.220(c) | Incident Management (C.04) | RC.RP – Incident Recovery Plan Execution; |
Manage risks associated with contracted activities with regard to the management of information security | Management | Supplier Relationship Management (E.10) | GV.SC – Cybersecurity Supply Chain Risk Management | |
Create and maintain a process to ensure that there is sufficient personnel to perform all activities regarding information security management | Management | IS.D.OR.240(f) | Personnel Development (D.11) | GV.RR – Roles, Responsibilities, and Authorities |
Create and maintain a process to ensure that the personnel have the necessary competence for activities regarding information security management | Management | IS.D.OR.240(g) | Personnel Development (D.11) | GV.RR – Roles, Responsibilities, and Authorities; |
Create and maintain a process to ensure that the personnel acknowledge the responsibilities associated with the assigned roles and tasks | Management | IS.D.OR.240(h) | Personnel Development (D.11) | GV.RR – Roles, Responsibilities, and Authorities |
Verify the identity and trustworthiness of personnel who have access to information systems | Management | IS.D.OR.240(i) | ISM (E.08) | GV.RR – Roles, Responsibilities, and Authorities; |
Archive, protect and retain records and ensure they are traceable for a specified time | Operational | ISM (E.08), Compliance (E.09) | GV.OV – Oversight; | |
Correct non-compliance findings upon notification by the competent authority within the period agreed with the competent authority | Operational | |||
Implement an information security reporting system in accordance with Regulation (EU) No 376/2014 | Management | IS.D.OR.230(a) | ||
Report information security incidents or vulnerabilities to the competent authority and, under certain conditions, to others | Operational | IS.D.OR.230(b) | Incident Management (C.04) | GV.OC – Organisational Context; |
Regularly assess the effectiveness and maturity of the ISMS | Operational | IS.D.OR.260(a) | ISM (E.08) | GV.OV – Oversight; |
Take actions to improve the ISMS if required. Reassess the ISMS elements affected by the implemented measures. | Operational | IS.D.OR.260(b) | ISM (E.08) | GV.OV – Oversight; |
Ensure accessibility of the competent authority to the contracted organisation | Management | IS.D.OR.235(b) | ISM (E.08) | GV.OC – Organisational Context |
Top management ensures that all necessary resources are available to comply with the Regulation | Management | IS.D.OR.240(a)(1) | ISM (E.08) | GV.RR – Roles, Responsibilities, and Authorities |
Top management establishes and promotes the information security policy and demonstrates a basic understanding of the Regulation | Management | IS.D.OR.240(a)(2) | ISM (E.08) | GV.PO – Policy; |
Appoint a responsible person or a group of persons with appropriate knowledge to manage compliance with the Regulation | Management | IS.D.OR.240(b) | ISM (E.08), Compliance (E.09) | GV.PO RR – Roles, Responsibilities, and Authorities |
Create and maintain an information security management manual (ISMM) | Management | |||
Develop a procedure on how to notify the competent authority upon changes to the ISMS | Management | IS.D.OR.255(a) | Compliance (E.09) | GV.OC – Organisational Context; |
Manage changes to the ISMS and notify the competent authority and/or request for approval of changes | Management | IS.D.OR.255(a) | ISM (E.08), Process Improvements (E.05) | GV.OC – Organisational Context; |
Appendix III — Examples of aviation services and interfaces
ED Decision 2025/014/R
AVIATION SERVICES
The following is a non-exhaustive and non-complete list of aviation services that can be used as a basis to identify the scope of the risk assessment for the organisation.
—aerodrome & ATM-MET service providers
—aeronautical digital mapping services
—aeronautical information management (AIM) – external, national, regional
—airports
—air traffic control (ATC) – external, superior
—air traffic management (ATM)
—approach (APP) & area control (ACC) Services – ER ACC, APP ACC
—cargo and passenger loading
—civil & state airspace user (AU) operations centres
—communication infrastructure
—flight information services / traffic information services (FIS/TIS) data integrator
—fuel calculation
—navigation infrastructure – ground-based, satellite-based
—non-ATM meteorological (MET) service providers
—mass & balance calculation
—non-aviation users (external)
—regional & sub-regional airspace management (ASM) and air traffic flow & capacity management (ATFCM)
—static aeronautical data services
—sub-regional demand & capacity balancing (DCB) common service providers
—surveillance infrastructure – airport, en-route, terminal manoeuvring area (TMA)
—route planning
—time reference services (external)
—tower (TWR) services
INTERFACES
Below are some examples of data exchange at the interfaces between organisations interacting in different functional chains, which can be used as a basis for identifying the scope of the risk assessment for the organisation.
Note 1: These examples are graphical representations based on the ‘Examples of ecosystem data exchange’ provided in EUROCAE ED-201A, Appendix B - Tables B-14, which can be consulted for further information.
Note 2: Although it is not an organisation, an aircraft has been included in all these examples for the sake of completeness of the description of the data exchange. The aircraft should be considered as an element within the scope of the ISMS of the organisation to which it belongs (typically the airline). Any data exchange between aircraft and other systems within the organisation should take into account existing security measures that may have been evaluated as part of aircraft certification (see also GM1 IS.D.OR.205(c)).
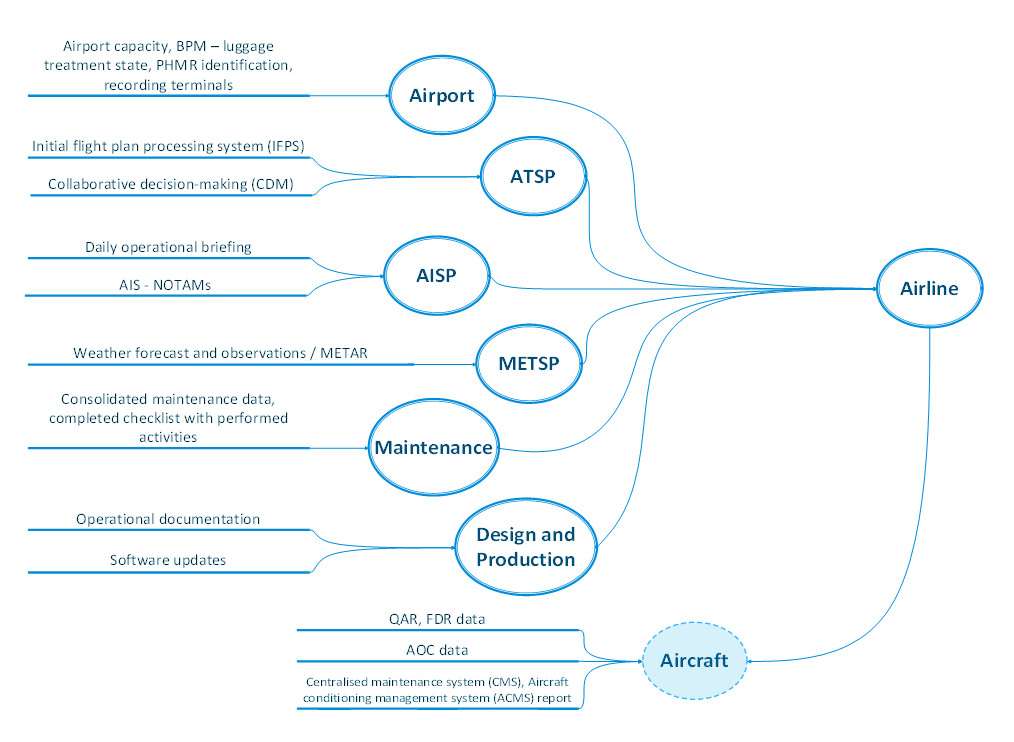
Figure 1: Interfaces of other organisations with an airline operator
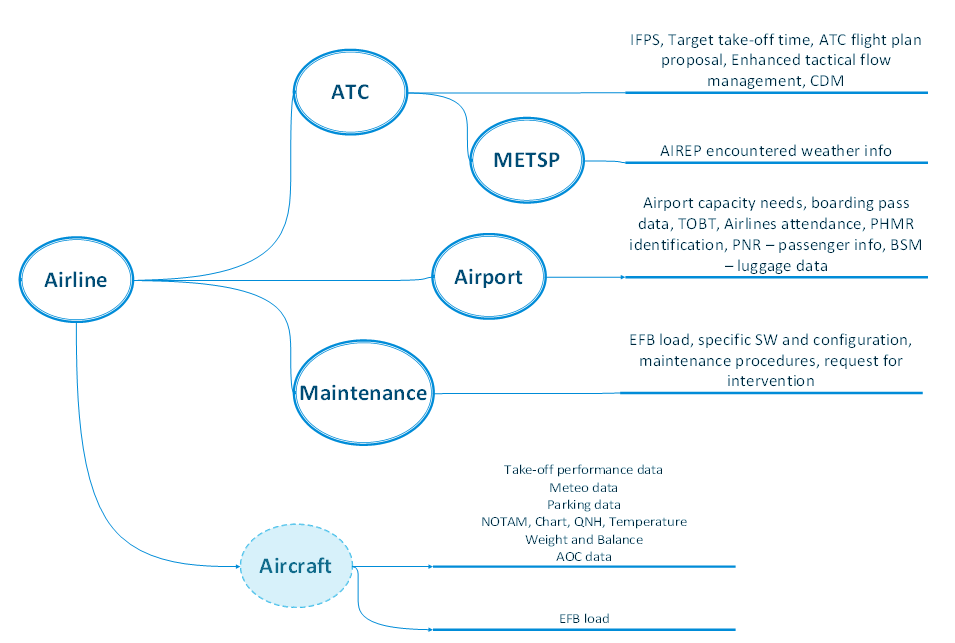
Figure 2: Interfaces of an airline operator with other organisations
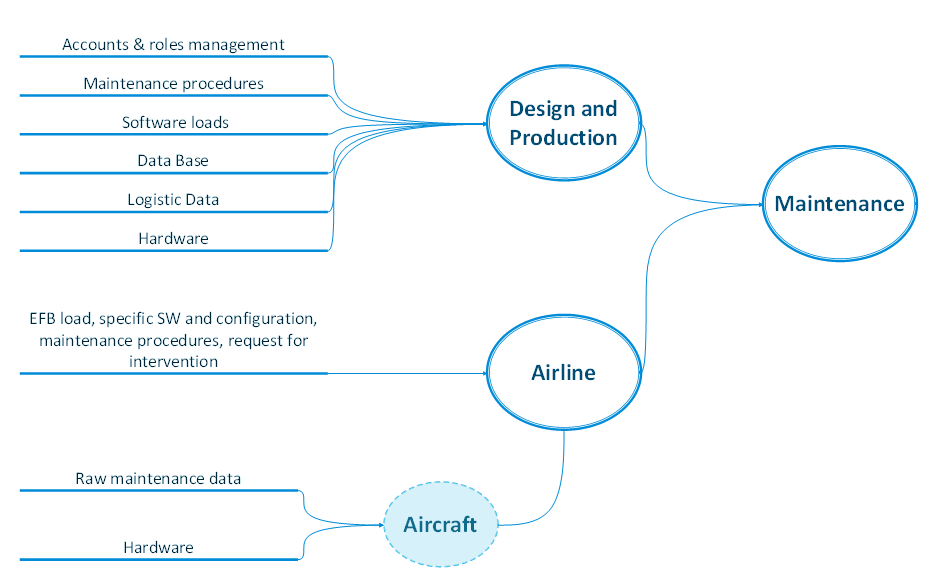
Figure 3: Interfaces of other organisations with a maintenance service provider
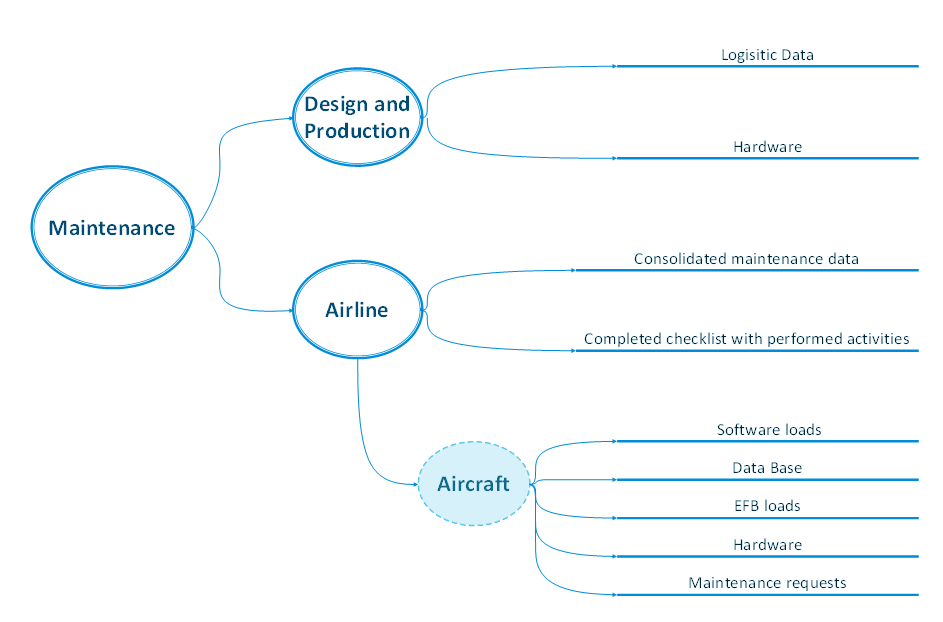
Figure 4: Interfaces of a maintenance service provider with other organisations
