Filters
Appendix IV — Part-IS requirements mapping to ISO/IEC 27001:2022 clauses and controls, and considerations on differences
ED Decision 2025/015/R
Although Part-IS does not credit ISO/IEC 27001 certification, the practices and methods typically adopted for implementing and maintaining an ISMS under ISO/IEC 27000 largely align with the objectives of this regulation. Therefore, entities that have already implemented an ISMS under ISO/IEC 27001 can use this as a basis for Part-IS compliance.
The following provides guidance on how competent authorities that have already implemented an ISMS compliant with ISO/IEC 27001:2022 can integrate Part-IS requirements into their existing ISMS. Specifically, the table below illustrates how to incorporate the ‘Part-IS particularity’ of each requirement into an existing ISO/IEC 27001-based ISMS in order to achieve Part-IS compliance. This is referred to as ‘Guidance on Part-IS implementation’.
Part-IS requirement | ISO/IEC 27001:2022 mapping and specific guidance |
IS.AR.200(a) | Related ISO/IEC 27001:2022 clauses and controls |
4.Context of the organisation 6.1.1Actions to address risks and opportunities - General | |
Part-IS particularity | |
An ISMS designed in the context of an ISO/IEC 27001:2022 ISMS, which is currently not connected to the management systems required by the delegated and implementing acts of Regulation (EU) 2018/1139, including Part-IS, may differ if these different systems do not address the same goals. Part-IS focuses on information security requirements meeting the applicable aviation safety objectives, which have an influence on elements of the ISMS. Also, the ‘interested parties’ and the ‘internal and external issues’ as laid down in Chapter 4 of ISO/IEC 27001:2022 may be adapted to address the requirements of Part-IS for the competent authority. | |
Guidance on Part-IS implementation | |
Please note that the point IS.AR.200 requirement points to many other Part-IS requirements that the ISMS has to comply with, namely points 205, 210, 215, 220, 225, 230 and 235. Further details are provided in the specific chapters on the particular requirement. Regarding the other remaining requirements, not pointing out to other Part-IS requirements, and comparing them with ISO/IEC 27001:2022, there are five requirements left, namely points IS.AR.200(a)(1), IS.AR.200(a)(8), IS.AR.200(a)(9), IS.AR.200(a)(10) and IS.AR.200(a)(11). | |
IS.AR.200(a)(1) | Related ISO/IEC 27001:2022 clauses and controls |
5.2Policy A.5.1Policies for information securities | |
Part-IS particularity | |
An ISMS designed in the context of an ISO/IEC 27001:2022 ISMS, which is currently not connected to the management systems required by the delegated and implementing acts of Regulation (EU) 2018/1139, may differ as these different systems do often not address the same goals. Part-IS focuses on information security requirements influencing the applicable aviation safety objectives, which in their turn have an influence on the elements of the ISMS. | |
Guidance on Part-IS implementation | |
The policy on information security established in an ISO/IEC 27001:2022 context has to be updated with regard to the potential impact of the risks on aviation safety. At least the elements of AMC1 IS.AR.200(a)(1) have to be mentioned in the policy. Therefore, the following elements may need to be added to an existing ISMS policy. The elements in bold and italics are additional guidance that might also be considered. (a)committing to complying with applicable legislation, considering relevant standards and best practices, including safety- and cybersecurity-related standards and guidance published or prescribed by ICAO or EASA; (b)setting objectives and performance measures for managing information security, updated to ensure meeting the applicable aviation safety objectives; (c)defining general principles, activities, processes for the competent authority to appropriately secure information and communication technology systems and data, in relation to the information security / safety risk assessment required by point IS.AR.205; (d)committing to applying ISMS requirements into the processes of the competent authority; (e)committing to continually improving towards higher levels of information security process maturity as per point IS.AR.235; (f)committing to satisfying applicable requirements regarding information security and its proactive and systematic management and to providing appropriate resources for its implementation and operation; (g)assigning information security as one of the essential responsibilities for all managers; (h)committing to promoting the information security policy through training or awareness sessions within the competent authority to all personnel on a regular basis or upon modifications; (i)encouraging the implementation of a ‘just culture’ and the reporting of vulnerabilities, suspicious/anomalous events and/or information security incidents; (j)committing to communicating the information security policy to all relevant parties, as appropriate. | |
IS.AR.200(a)(8) | Related ISO/IEC 27001:2022 clauses and controls |
9.2.Internal audit 9.3Management review 10.2Non-conformity and corrective action A5.36Compliance with policies, rules and standards for information security | |
Part-IS particularity | |
This requirement is strongly related to the internal audit system and the independent checking function of ISO/IEC 27001:2022. The required feedback system to the person referred to in point IS.AR.225(a) fits into the requirement of 9.3. In addition, all delegated and implementing acts for the specific domains require a similar ‘compliance monitoring function’, where information security should be integrated as described in AMC1 IS.AR.200(a)(8). | |
Guidance on Part-IS implementation | |
The requirements of ISO/IEC 27001:2022 and the delegated and implementing acts of Regulation (EU) 2018/1139 are compatible. Therefore, it will be easy to integrate Part-IS into the audit scope of the ISO/IEC 27001:2022 internal audit system. The role of the the person referred to in point IS.AR.225(a) has to be addressed accordingly in the feedback loop if the role is not already addressed in the management review process. This person is required to be personally briefed on the key findings so that appropriate decisions can be made. Refer also to GM1 IS.AR.200(a)(8). Note: ISO 19011:2018 provides guidance on the establishment of an internal audit system. Specifically, Chapter A.7 ‘Auditing compliance within a management system’ provides useful guidance on how to integrate a compliance monitoring function into an internal audit system. | |
IS.AR.200(a)(9) | Related ISO/IEC 27001:2022 clauses and controls |
7.5.3.Control of documented information (Note) A5.12Classification of information A5.34Privacy and protection of personal identifiable information (PII) A8.12Data leakage prevention | |
Part-IS particularity | |
This requirement is limited to ‘information related to oversight activities and received through the organisation’s external reporting scheme’ and to confidentiality. ISO/IEC 27001:2022 does not differentiate between type of information (as laid down e.g. in ISO 9001:2015 Chapter 8.5.3). The only reference is made in the note in Chapter 7.5.3. Part-IS stresses protection of information-related oversight activities and external information received due to the sensitivity it may have regarding incidents and vulnerabilities disclosure. Insufficient confidentiality protection may result in exploitation of vulnerabilities affecting safety that the original provider of information may not have perceived. | |
Guidance on Part-IS implementation | |
The protection of information, specifically regarding confidentiality (as in ISO/IEC 27002:2022), is related to a set of controls that can be found in Table A.1 (Matrix of controls and attribute values) of ISO/IEC 27002:2022. See also the definition in ISO/IEC 27002:2022: 3.1.7Confidential information Information that is not intended to be made available or disclosed to unauthorized individuals, entities or processes. The competent authority having implemented these controls should take special care that they apply to external information that may result in information security threats if known by unauthorised actors. When this kind of information is further shared with other entities, appropriate confidentiality procedures must be put in place and followed (TLP marking for instance). | |
IS.AR.200(a)(10) and | Related ISO/IEC 27001:2022 clauses and controls |
A5.5Contact with authorities | |
Part-IS particularity | |
These requirements are not directly addressed in ISO/IEC 27001:2022. | |
Guidance on Part-IS implementation | |
This is not covered by the requirements of ISO/IEC 27001:2022, so it is not possible to adapt existing policies and procedures under ISO/IEC 27001:2022 for these provisions. To ensure compliance with these requirements, please refer exclusively to the related AMC and GM. | |
IS.AR.200(b) | Related ISO/IEC 27001:2022 clauses and controls |
10.1Continual improvement | |
Part-IS particularity | |
Part-IS and ISO/IEC 27001:2022 are very similar regarding this requirement. See points IS.AR.235 (a) and (b) for subtle differences. | |
Guidance on Part-IS implementation | |
See point IS.AR.235 in this table. | |
IS.AR.200(c) | Related ISO/IEC 27001:2022 clauses and controls |
6.3Planning of changes 7.5.3Control of documented information | |
Part-IS particularity | |
Control of documented information is one of the key processes in each ISO management system standard, following the ISO ‘high-level structure’ (ISO/IEC Directives part 1 Annex SL), such as ISO/IEC 27001:2022. In addition, most of the delegated and implementing acts for the specific domains require a similar need to document, where information security should be integrated. | |
Guidance on Part-IS implementation | |
Additional guidance is provided under GM1 IS.AR.200(c). | |
IS.AR.200(d) | Related ISO/IEC 27001:2022 clauses and controls |
4.3Determining the scope of the information security management system. | |
Part-IS particularity | |
The scope statement and the ‘statement of applicability’ (SOA) are the best references to apply the ‘nature and complexity’. In addition, most of the delegated and implementing acts for the specific domains require a similar need to document, where information security should be integrated. | |
Guidance on Part-IS implementation | |
When determining the scope, it should be noted that Part-IS is delimited to the subject matter as defined in Article 1 of the Regulation(s), which refers to identification and management of information security risks with potential impact on aviation safety. Considering this, the scope of an ISMS under ISO/IEC 27001:2022 may be broader than that required by Part-IS. Some organisational units, processes or locations may fall under what is covered by the ISMS under ISO/IEC 27001:2022, but not within the scope of Part-IS. The opposite may happen too: the scope under ISO/IEC 27001:2022 may be narrower than the one Part-IS would require (e.g. the ISO/IEC 27001:2022 scope covers only the IT department). In both situations, scope definitions have to be compared and adjusted when necessary. Note: See also guidance on point IS.AR.205(a) in this table. The scope statement in the ISO/IEC 27001:2022 context is the right place where this clarification is made. | |
IS.AR.205(a) | Related ISO/IEC 27001:2022 clauses and controls |
4.3Determining the scope of the information security management system 6.1.2Information security risk assessment | |
Part-IS particularity | |
This requirement of Part-IS is in line with ISO/IEC 27001:2022, however ISO/IEC 27001:2022 allows a wider focus, whereas Part-IS puts the focus on safety already from the element’s identification stage. In addition, all of the delegated and implementing acts for the specific domains require a risk assessment process, where information security can be integrated. | |
Guidance on Part-IS implementation | |
AMC1 IS.AR.205(a) explains that when conducting an information security risk assessment, the competent authority should ensure that each relevant aviation safety impact is identified and included in the ISMS scope, which might not be the case when using ISO/IEC 27001:2022. On the other hand, an ISO/IEC 27001:2022 ISMS focuses its security risk assessment mainly on the business impact of infringement on confidentiality, integrity and availability, their risks and the impact on assets (e.g. loss of IT infrastructure, breach of data). This means that, starting from an ISMS based on ISO/IEC 27001:2022, a complementary analysis has to be made to take into account all the elements related to aviation safety. To bridge the two approaches of management systems (SMS and ISMS), an identified information security risk may be entered as a ‘cause’ or ‘contributing event’ in the aviation-safety-focused risk assessment required by the domain-specific implementing or delegated act. The figure in GM1 IS.AR.205(c) provides a good indication of how this bridge could be built. | |
IS.AR.205(b) | Related ISO/IEC 27001:2022 clauses and controls |
4.1Understanding the organisation and its context 4.3Determining the scope of the information security management system A5.19Information security in supplier relationships A5.21Managing information security in the information and communication technology (ICT) supply chain | |
Part-IS particularity | |
Point IS.AR.205(b) focuses on the identification of interfaces with the other parties. ISO/IEC 27001:2022 4.3 requires considering in point c) the interfaces at and dependencies between activities performed by the competent authority and those that are performed by other parties. So, there is more in Part-IS than that required by ISO/IEC 27001:2022, provided that the scope considered includes safety, as required by point IS.AR.205(a). Controls A5.19 and A5.21 are a profound foundation for the requirements of point IS.AR.205(b). | |
Guidance on Part-IS implementation | |
ISO/IEC 27001:2022 A5.19 requires the identification of risks associated with the use of suppliers’ products or services. ISO 27002 A5.19 contains additional guidance in points f) to j) on how to manage the risk exposure. ISO/IEC 27001:2022 A5.21 requires the management of information security risks associated with the ICT products and services supply chain. ISO 27002 A5.21 contains additional guidance in points f), k), l) and m) on how to manage risks through the supply chain. The Part-IS notion about interfaces and supply chain goes beyond the respective ISO/IEC 27001:2022 notion. GM1 IS.AR.205(b) requests interfacing entities to share information about mutual risk exposure (including all data flows) and urges competent authorities to use ED-201A for that. Point IS.AR.205(c) also requires accounting for information acquired by interfacing entities, which underlines the two-way nature of the considerations. | |
IS.AR.205(c) | Related ISO/IEC 27001:2022 clauses and controls |
6.1.2Information security risk assessment | |
Part-IS particularity | |
Point IS.AR.205(c) is the ‘heart’ of Part-IS. ISO/IEC 27001:2022 6.1.2 opens a ‘framework’ where the requirements of point IS.AR.205 may fit in. It has to be assured that the risk management systems of the ISMS and those required by the SMS-regulations (see point IS.AR.205(a)) do NOT operate independently, as there might be difficulties in connecting the two systems. | |
Guidance on Part-IS implementation | |
Further to this provision, a proper risk assessment has to be made, taking into account the scope and interfaces described in points IS.AR.205(a) and IS.AR.205(b). It has to be noted (see also GM1 IS.AR.205(c)) that point IS.AR.205 does not require the use of any specific information security risk assessment framework, such as ISO31000, NIST or others to develop the risk assessment. ISO/IEC 27001:2022 tends to lean towards using ISO 27005 as a risk assessment standard; however, it does not make it mandatory. The key point is that the risk assessment carried out in the application of ISO/IEC 27001:2022 6.1.2 does not necessarily consider safety risks, and may focus on different types of risks. With respect to safety, conditions that may lead to safety consequences are identified as hazards. Their materialisation may be either directly triggered or caused by information security threats which have not been successfully prevented. Information security can thus cause or contribute to a safety consequence in four different ways: (1)it can act as a safety threat; (2)it can have a negative effect on a safety barrier, rendering it less effective than before; (3)it can directly trigger the materialisation of an already identified hazard; or (4)it can constitute a new, not yet identified, hazard, which can obviously also materialise. By using e.g. the ‘bow-tie method’ regarding information security, a ‘hazard’ would be replaced by a ‘vulnerability’, which can be exploited resulting in information security consequences (e.g. lack or reduction of confidentiality, integrity, availability, authenticity properties). Hence, from a methodology perspective, both considerations are very similar and can be designed to interact (e.g. consequences of the information security bow-tie may connect as causes of the ‘safety bow-tie’). Where the authority has implemented an SMS and operates an ISMS under voluntary compliance with ISO/IEC 27001:2022, it may operate two risk management systems, one for safety and one for information security. The latter may ultimately be certified by an ISO/IEC 27001:2022-accredited body. Each potential risk identified by the ISMS risk management has to be systematically assessed for its potential impact on safety. To establish the connection between the systems, the following approach should be used: (1)If a safety risk assessment is available, it should be able to provide its context and determined target likelihoods for acceptable information security risks to the information security risk assessment process. The context consists of the system architecture, including its preventative and mitigative barriers, the hazards assessed and the safety risks identified. Based upon the information provided, the information security risk assessment can be conducted. Modifications to the system architecture, or any modifications of properties of the preventative or mitigative barriers, as well as the achieved risk properties need to be communicated back to the safety risk assessment process. Based upon this communication, the safety risk assessment has to be updated. In other words: mitigation measures put in place as a result of the information security risk assessment should also be considered as they may not only mitigate, but possibly also create a negative safety impact. (2)If a safety risk assessment is available, but the information security assessment process identifies a new hazard that was previously unknown to the safety risk assessment, a full hazard assessment of all safety aspects has to be conducted to ensure that the safety risk assessment contains the ‘full picture’ of the newly addressed hazard. (3)The safety risk and the information security risk assessments need to be repeated as described above until all acceptability requirements for all aspects are met. | |
IS.AR.205(d) | Related ISO/IEC 27001:2022 clauses and controls |
6.3Planning of changes 8.2Information security risk assessment | |
Part-IS particularity | |
Point IS.AR.205(d) is about the subsequent changes to the original risk assessment, due to a change of context or interfaces or knowledge about the risks or lessons learnt. This is equivalent to ISO/IEC 27001:2022 8.2. In both frameworks the reviews are planned and documented. | |
Guidance on Part-IS implementation | |
The same process as that already in place in an ISO/IEC 27001:2022 context can be used to implement point IS.AR.205(d), provided that this process has been updated to include safety criteria evaluation of changes that trigger an unplanned update of the risk assessment. Those competent authorities that have most experienced risk assessment updates at planned intervals will need to be proactive to trigger such updates more often in the situations listed in points IS.AR.205(d) (1), (2), (3), and (4) that could affect safety. The triggering criteria and the process should be documented and tested before implementation, for example through table-top exercises. The change management process is key to keep a management system in a solid and stable condition. Considering an established ISMS according to ISO/IEC 27001:2022, the regular updates of the risk assessment based on changes and lessons learned should be effective. The essential focus, introduced by Part-IS, is the ‘impact on safety’, which drives the update assessment. Change management processes focusing on changes that may have impact on safety are also set out in all domain-specific implementing and delegated acts. Without the ‘bridge’ of Part-IS, both systems (ISMS and SMS) are implemented independently, often without considering interdependencies. Part-IS implies the need (and provides the opportunity) to interlink the systems to provide a common risk picture for the competent authority, with a focus on safety, but also opening the horizon to information security. | |
IS.AR.210(a) | Related ISO/IEC 27001:2022 clauses and controls |
6.1.3Information security risk treatment 8.3Information security risk treatment | |
Part-IS particularity | |
Point IS.AR.210(a) is about information security risk treatment, which is widely covered by ISO/IEC 27001:2022, its Appendix A, and ISO/IEC 27002. Point IS.AR.210(a) provides however some additional inputs related to the risks that may have a safety impact. | |
Guidance on Part-IS implementation | |
ISO/IEC 27001:2022 6.1.3 is about the definition of the risk treatment plan, while ISO/IEC 27001:2022 8.3 deals with the implementation of the plan, and both are relevant. ISO/IEC 27001:2022 Annex A contains a list of possible information security controls, and therefore should also be used in addition to the already existing controls, to mitigate information security risks having an impact of safety. All the controls of Annex A are detailed in ISO/IEC 27002. Point IS.AR.210(a) specifies that the measures selected in the plan have to reduce the consequences on aviation safety associated with the materialisation of the threat scenario. This is in line with IS.AR.205 since the risk treatment phase is a consequence of the risk assessment phase and has to address all the risks that have been evaluated. Point IS.AR.210(a) also stipulates that those (protection) measures shall not introduce any new potential unacceptable risks to aviation safety. This is an area that is not directly covered by either ISO/IEC 27001:2022 or Also, the risk treatment of the identified risks should focus on addressing safety via the same linkage/integration of ISMS and safety management. | |
IS.AR.210(b) | Related ISO/IEC 27001:2022 clauses and controls |
6.1.3.fInformation security risk treatment 7.3Awareness 9.3Management review A5.19Information security in supplier relationships A5.21Managing information security in the ICT supply chain | |
Part-IS particularity | |
Point IS.AR.210(b) requires key personnel in the competent authority to be informed about the risks, the corresponding threat scenarios and the security risk treatment measures, which result in specific controls covered by Annex A to ISO/IEC 27001:2022 and ISO/IEC 27002. It partially covers point IS.AR.210(b) by the following requirement: obtain risk owners’ approval of the information security risk treatment plan and acceptance of the residual information security risks. Point IS.AR.210(b) has two specific requirements that also have equivalent requirements in ISO/IEC 27001:2022 and ISO/IEC 27002: —Inform the person referred to in point IS.AR.225(a) of the risk treatment plan — which is a mandatory input to the management review. —Inform the interfacing entities (the same as in point IS.AR.205(b)) of all risks shared with them — which is stated in A5.19 Guidance point l). | |
Guidance on Part-IS implementation | |
In addition to the risk owner’s approval requested by ISO/IEC 27001:2022 6.1.3.f, the competent authority will need to inform: —the person referred to in point IS.AR.225(a) of the risk treatment plan. ISO/IEC 27001:2022 9.3. f) defines ‘results of risk assessment and status of risk treatment plan’ as mandatory input for the management review which is the vehicle to inform the person referred to in point IS.AR.225(a); —the interfacing entities (the same as in point IS.AR.205(b)) of all risks shared with them. ISO/IEC 27002 A5.21 states in point f) ‘defining rules for sharing of information and any potential issues and compromises between the organisations’. GM1 IS.AR.205(b) and ED-201A may also be used as guidance on risk sharing. | |
IS.AR.215(a) | Related ISO/IEC 27001:2022 clauses and controls |
A5.24Information security incident management planning and preparation A5.25Assessment and decision on information security events A5.26Response to information security incidents A5.27Learning from information security incidents A5.28Collection of evidence A5.29Information security during disruption A7.5Physical security monitoring A8.16Monitoring activities | |
Part-IS particularity | |
Fully covered by the requirements of A5.24 to A5.29, and A7.5 for physical security and A8.16 for technical monitoring. | |
Guidance on Part-IS implementation | |
The requirements of the controls (both reactive and proactive) mentioned above and the guidance in ISO/IEC 27002:2022 are comprehensive to fulfil the requirements of point IS.AR.215(a). Again, the impact on safety needs to be assessed, and measures shall be taken to ensure safety. Part-IS refers to ‘unsafe conditions’, which have to be mitigated to an acceptable level. A re-assessment of risks that are related to incidents that have occurred or to a vulnerability that has been identified is mandatory in Part-IS to ensure that no risk becomes unacceptable. Note: Due to historical reasons, information security and safety management use different wording when referring to situations which are more or less the same. The term ‘incident’ is used in a similar way (an event which already happened and infringes safety/security). A vulnerability in the sense of information security could be mapped to the term ‘hazard’ in the area of safety (a situation identified, which is possible to happen, but has not happened so far). | |
IS.AR.215(b) | Related ISO/IEC 27001:2022 clauses and controls |
A5.26Response to information security incidents A5.29Information security during disruption A7.5Physical security monitoring A8.8Management of technical vulnerabilities | |
Part-IS particularity | |
Fully covered by the requirements of A5.26 and A5.29. | |
Guidance on Part-IS implementation | |
The requirements of the control A5.26 and the guidance in ISO/IEC 27002:2022 are comprehensive to fulfil the requirements of point IS.AR.215(b). | |
IS.AR.215(c) | Related ISO/IEC 27001:2022 clauses and controls |
A5.26Response to information security incidents A5.29Information security during disruption | |
Part-IS particularity | |
This requirement is covered by the requirements of A5.26 and A5.29, with the difference that the recovery here is not intended to continuously ensure confidentiality, integrity, availability and integrity; instead, it is intended to maintain or return to an acceptable level of safety. | |
Guidance on Part-IS implementation | |
Coupled with the requirements of controls A5.26 and A5.28 and the guidance in ISO/IEC 27002:2022, AMC1.IS.AR.215(c) should be applied in order to revert as quickly as possible to a safe state. | |
Related ISO/IEC 27001:2022 clauses and controls | |
A5.19Information security in supplier relationships A5.21Managing information security in the information and communication technology (ICT) supply chain A5.22Monitoring, review and change management of supplier services | |
Part-IS particularity | |
ISO/IEC 27001:2022 controls A5.19, A5.21 and A5.29 may cover this requirement. The difference in the requirements of point IS.AR.220 is that they are limited to those activities directly related to the ISMS (e.g. internal audits, consultancy for risk assessments, etc.). | |
Guidance on Part-IS implementation | |
This requirement relates only to ISMS activities (e.g. internal audits, risk assessments), not to those activities not directly related to ISMS itself (e.g. hardware, software, IT and OT). The difference in the requirements of point IS.AR.220 is that they are limited to those activities directly related to the ISMS (e.g. internal audits, consultancy for risk assessments, etc.). The controls in ISO/IEC 27001:2022 do not exclude those kinds of services, but sometimes they will not be in the focus of the competent authority. Therefore, there is no need to establish an independent system for those contractors referred to in point IS.AR.220. The list of suppliers should be reviewed to ensure that the suppliers providing the services mentioned in point IS.AR.220 are covered. | |
IS.AR.225(a) | Related ISO/IEC 27001:2022 clauses and controls |
5.1Leadership and commitment 5.3Organisational roles, responsibilities and authorities 7.1Resources A5.2Information security roles and responsibilities | |
Part-IS particularity | |
ISO/IEC 27001:2022 does not require a specific role. | |
Guidance on Part-IS implementation | |
The implementation of the requirements of point IS.AR.225(a) can be covered by the implementation of ISO/IEC 27001:2022 requirements mentioned above, provided that the role of the person referred to in point IS.AR.225(a) is clearly defined and meets the requirements in point IS.AR.225(a). | |
IS.AR.225(b) | Related ISO/IEC 27001:2022 clauses and controls |
7.1Resources | |
Part-IS particularity | |
The requirements of 7.1 should be implemented. | |
Guidance on Part-IS implementation | |
A systematic capacity planning of human resources is a key element of any management system. Therefore, such a process should be established in an ISMS. The possible additional requirement stemming from Part-IS has to be assessed and the capacity planning updated accordingly. The targeted safety levels set in the safety/information security assessment should never be jeopardised by a lack of resources, even temporarily. AMC1 IS.AR.225(b) should be considered. | |
IS.AR.225(c) | Related ISO/IEC 27001:2022 clauses and controls |
7.2Competency A6.3Information security awareness, education and training | |
Part-IS particularity | |
The implementation of the requirements of 7.2 and A6.3 is sufficient to cover the requirement. | |
Guidance on Part-IS implementation | |
A systematic competency management process of staff is a key element of any management system. Therefore, such a process should have been established in an ISMS. The possible additional requirement stemming from Part-IS has to be assessed and the competency requirements updated accordingly. AMC1 IS.AR.225(c) should be considered. | |
IS.AR.225(d) | Related ISO/IEC 27001:2022 clauses and controls |
A6.2Terms and conditions of employment | |
Part-IS particularity | |
The implementation of the requirements of A6.2 with some adaptation would be sufficient to cover the provision of point IS.AR.225(d). | |
Guidance on Part-IS implementation | |
Point IS.AR.225(d) is (at least partially) covered by ISO/IEC 27001:2022 A.6.2 ‘The employment contractual agreements should state the personnel’s and the organisation’s responsibilities for information security.’ and A.6.4 ‘disciplinary process’ (see ‘Just Culture’). It depends on the organisational culture and on whether job descriptions or role assignments need to be formally acknowledged. In many cases, the assigned jobs and roles are mutually acknowledged by performing the tasks assigned. | |
IS.AR.225(e) | Related ISO/IEC 27001:2022 clauses and controls |
A5.19Information security in supplier relationships A6.1Screening A7.2Physical entry A8.3Information access restriction A8.5Secure authentication | |
Part-IS particularity | |
The implementation of the requirements of A5.19, A6.1, A7.2, A8.3 and A8.5 might be sufficient controls to cover this requirement for the personnel of the competent authority, as well as for contractors and suppliers. | |
Guidance on Part-IS implementation | |
All the controls established in an ISO/IEC 27001:2022-compliant ISMS are designed to ensure the confidentiality and integrity of information. The implementation of those controls will provide sufficient protection to ensure compliance with this requirement. AMC1 IS.AR.225(e) should be considered. | |
IS.AR.230(a) | Related ISO/IEC 27001:2022 clauses and controls |
7.5Documented information A5.9Inventory of information and other associated assets A5.13Labelling of information A8.10Information deletion A8.13Information backup | |
Part-IS particularity | |
Record-keeping and retention are an inherent part of the document control system under 7.5 of ISO/IEC 27001:2022. Controls A5.9, A5.13, A8.10 and A8.13 also apply. | |
Guidance on Part-IS implementation | |
Chapter 7.5.1 b) states that the ISMS has to include ‘documented information determined by the competent authority as being necessary for the effectiveness of the information security management system.’ This includes the records defined in point IS.AR.230(a)(1). Chapter 7.5.3 requires, under f), also document control for retention and disposition. Part-IS requirements have to be integrated into the existing system, especially the minimum duration of record-keeping of five years. The minimum set of records, as defined in point IS.AR.230(a)(1) should be covered in the inventory of assets. For the coverage, the content of GM1 IS.AR.230 also applies. As records are not only information assets, the requested ‘record retention policy’ may be integrated into a wider policy as recommended by ISO/IEC 27002:2022 above. AMC1 IS.AR.230(a)(1)(iv)&(a)(4) should be implemented. | |
IS.AR.230(b) | Related ISO/IEC 27001:2022 clauses and controls |
7.5Documented information A5.9Inventory of information and other associated assets A5.10Acceptable use of information and other associated assets A5.13Labelling of information A5.34Privacy and protection of personal identifiable information (PII) A8.10Information deletion A8.13Information backup | |
Part-IS particularity | |
Record-keeping and retention are an inherent part of the document control system under 7.5 of ISO/IEC 27001:2022. Controls A5.9, A5.13, A8.10 and A8.13 will also apply and, due to GDPR issues specifically, also A5.10 and A5.34. | |
Guidance on Part-IS implementation | |
Chapter 7.5.1 b) states that the ISMS has to include ‘documented information determined by the competent authority as being necessary for the effectiveness of the information security management system.’ This includes the records defined in point IS.AR.230(a)(1). Chapter 7.5.3 requires, under f), also document control for retention and disposition. Part-IS requirements have to be integrated into the existing system, especially the minimum duration of record-keeping of five years. However, whereas there is no retention duration specified in ISO/IEC 27001:2022, point IS.AR.230(b) specifies three years after the person has left the competent authority. As these records fall under the GDPR Regulation, each competent authority has to ensure that they are handled accordingly. It is recommended that the procedures are used not only for records related to ISMS, but also for the entire HR personnel files of the staff. | |
IS.AR.230(c) | Related ISO/IEC 27001:2022 clauses and controls |
7.5Documented information A5.13Labelling of information | |
Part-IS particularity | |
Record-keeping and retention are an inherent part of the document control system under 7.5 of ISO/IEC 27001:2022 as well as control A5.13. | |
Guidance on Part-IS implementation | |
Chapter 7.5.3, under a), requires for the information that ‘it is available and suitable for use, where and when it is needed’. Part-IS requirements have to be integrated into the existing system. ISO/IEC 27002:2022 A5.13 states ‘Procedures for information labelling should cover information and other associated assets in all formats.’; therefore, the Part-IS requirement is fulfilled with control A5.13. | |
IS.AR.230(d) | Related ISO/IEC 27001:2022 clauses and controls |
7.5Documented information A5.10Acceptable use of information and other associated assets A5.12Classification of information A5.33Protection of records A8.12Data leakage prevention | |
Part-IS particularity | |
Record-keeping and retention are an inherent part of the document control system under 7.5 of ISO/IEC 27001:2022. Controls A5.10, A5.12, A5.33 and A8.12 will also apply. | |
Guidance on Part-IS implementation | |
Chapter 7.5.3, under d), requires ‘storage and preservation, including the preservation of legibility’. Part-IS requirements have to be integrated into the existing system. The application of A5.33 and A8.12 has a strong relationship to A7.5 (Protecting against physical and environmental threats), A7.10 (Storage media), A8.3 (Information access restriction), A8.13 (Information backup), A8.14 (Redundancy of information processing facilities), A8.15 (Logging), A8.17 (Clock synchronization) and A8.24 (Use of cryptography). | |
IS.AR.235(a) | Related ISO/IEC 27001:2022 clauses and controls |
9.3Management review 10.1Continual improvement A5.35Independent review of information security | |
Part-IS particularity | |
This requirement reflects a combination of requirements 9.3 and 10.1 of ISO/IEC 27001:2022 with references to requirements 4.4 and 5.2. While ISO/IEC 27001:2022 focuses on ISMS suitability, adequacy and effectiveness, point IS.AR.235(a) requires also a periodical maturity assessment of the ISMS. | |
Guidance on Part-IS implementation | |
ISO/IEC 27001:2022, 4.4 shows a clear requirement (‘shall’) for ISMS maintenance and improvement. The top management has a responsibility for continuous ISMS improvement as per ISO/IEC 27001:2022 5.2(d). The planning section also requires continuous improvement (ISO/IEC 27001:2022 6.1.1(c)). Point IS.AR.235(a) requires an assessment of the effectiveness and maturity of the ISMS on a calendar basis or following an information security incident. This assessment should be performed by using indicators. ISO/IEC 27001:2022 Chapter 9.3.1 defines a very similar approach for the management review process. Chapter 10.1 indicates a more independent process to improve the ISMS. The process in Chapter 10.1 is seen as more of a bottom-up approach, whereas that in Chapter 9.3 is intended to be topdown. The results from A5.35 should all be used as inputs for continuous improvement. Point IS.AR.235(a) requires also a maturity assessment of the ISMS. Each competent authority should establish which maturity model will be followed and which targeted maturity level is expected to be reached and by when. For the maturity assessment, point (b) of AMC1 IS.AR.235(a) and GM1 IS.AR.235(a) provide guidance on how to ensure compliance with point IS.AR.235(a). | |
IS.AR.235(b) | Related ISO/IEC 27001:2022 clauses and controls |
10.2Non-conformity and corrective action A5.7Threat intelligence | |
Part-IS particularity | |
Point IS.AR.235(b) addresses the improvement measures, i.e. corrections and corrective actions for the deficiencies detected in point IS.AR.235(a) and the continuous improvement process. This requirement reflects mainly requirement 10.2 of ISO/IEC 27001:2022, even if the term used is ‘non-conformity’, while point IS.AR.235(b) uses the term ‘deficiencies’. Deficiency has a broader meaning than non-conformity. It encompasses the case of a targeted maturity level that would not be reached at the planned date; that would be a deficiency but not necessarily a non-conformity. | |
Guidance on Part-IS implementation | |
The provisions listed in ISO/IEC 27001:2022 10.2 can be used to take corrective actions, to resolve both non-conformities and maturity level gaps. |
ANNEX II — INFORMATION SECURITY — ORGANISATION REQUIREMENTS [PART-IS.I.OR]
IS.I.OR.100 Scope
Regulation (EU) 2023/203
This Part establishes the requirements to be met by the organisations referred to in Article 2(1) of this Regulation.
IS.I.OR.200 Information security management system (ISMS)
Regulation (EU) 2023/203
(a)In order to achieve the objectives set out in Article 1, the organisation shall set up, implement and maintain an information security management system (ISMS) which ensures that the organisation:
(1)establishes a policy on information security setting out the overall principles of the organisation with regard to the potential impact of information security risks on aviation safety;
(2)identifies and reviews information security risks in accordance with point IS.I.OR.205;
(3)defines and implements information security risk treatment measures in accordance with point IS.I.OR.210;
(4)implements an information security internal reporting scheme in accordance with point IS.I.OR.215;
(5)defines and implements, in accordance with point IS.I.OR.220, the measures required to detect information security events, identifies those events which are considered incidents with a potential impact on aviation safety except as permitted by point IS.I.OR.205(e), and responds to, and recovers from, those information security incidents;
(6)implements the measures that have been notified by the competent authority as an immediate reaction to an information security incident or vulnerability with an impact on aviation safety;
(7)takes appropriate action, in accordance with point IS.I.OR.225, to address findings notified by the competent authority;
(8)implements an external reporting scheme in accordance with point IS.I.OR.230 in order to enable the competent authority to take appropriate actions;
(9)complies with the requirements contained in point IS.I.OR.235 when contracting any part of the activities referred to in point IS.I.OR.200 to other organisations;
(10)complies with the personnel requirements laid down in point IS.I.OR.240;
(11)complies with the record-keeping requirements laid down in point IS.I.OR.245;
(12)monitors compliance of the organisation with the requirements of this Regulation and provides feedback on findings to the accountable manager to ensure effective implementation of corrective actions;
(13)protects, without prejudice to applicable incident reporting requirements, the confidentiality of any information that the organisation may have received from other organisations, according to its level of sensitivity.
(b)In order to continuously meet the requirements referred to in Article 1, the organisation shall implement a continuous improvement process in accordance with point IS.I.OR.260.
(c)The organisation shall document, in accordance with point IS.I.OR.250, all key processes, procedures, roles and responsibilities required to comply with point IS.I.OR.200(a), and shall establish a process for amending that documentation. Changes to those processes, procedures, roles and responsibilities shall be managed in accordance with point IS.I.OR.255.
(d)The processes, procedures, roles and responsibilities established by the organisation in order to comply with point IS.I.OR.200(a) shall correspond to the nature and complexity of its activities, based on an assessment of the information security risks inherent to those activities, and may be integrated within other existing management systems already implemented by the organisation.
(e)Without prejudice to the obligation to comply with the reporting requirements laid down in Regulation (EU) No 376/2014 and the requirements laid down in point IS.I.OR.200(a)(13), the organisation may be approved by the competent authority not to implement the requirements referred to in points (a) to (d) and the related requirements contained in points IS.I.OR.205 through IS.I.OR.260, if it demonstrates to the satisfaction of that authority that its activities, facilities and resources, as well as the services it operates, provides, receives and maintains, do not pose any information security risks with a potential impact on aviation safety neither to itself nor to other organisations. The approval shall be based on a documented information security risk assessment carried out by the organisation or a third party in accordance with point IS.I.OR.205 and reviewed and approved by its competent authority.
The continued validity of that approval will be reviewed by the competent authority following the applicable oversight audit cycle and whenever changes are implemented in the scope of work of the organisation.
GM1 IS.I.OR.200 Information security management system (ISMS)
ED Decision 2025/014/R
An information security management system (ISMS) is a systematic approach to establish, implement, operate, monitor, review, maintain and continuously improve the state of information security of an organisation. Its objective is to protect the information assets, such that the operational and safety objectives of an organisation can be reached in a risk-aware, effective and efficient manner.
Generally speaking, an ISMS establishes an information security risk management process, based upon the results of information security impact analyses, which basically determine its scope. If information security breaches may cause or contribute to aviation safety consequences, information security requirements need to limit the impact or influence of information security breaches on levels of aviation safety, which are deemed acceptable. Hence, all roles, processes, or information systems, which may cause or contribute to aviation safety consequences, are within the scope of Regulation (EU) 2023/203. The ISMS provides for means to decide on needed information security controls for all architectural layers (governance, business, application, technology, data) and domains (organisational, human, physical, technical). It further allows to manage the selection, implementation, and operation of information security controls. Finally, it allows to manage the governance, risk management and compliance (GRC) within the ISMS scope.
The overall risk assessment considers safety consequences influenced by information security risks. These may emerge as threats, hazards, escalation factors that weaken barriers, or direct triggers of existing hazards. When conducting this assessment, both aspects, information security and safety need to be coordinated throughout the process. This ensures mutual understanding of the objectives and the implementation of preventive measures against all types of threats or weaknesses, as well as mitigating measures.
The risk management process is thus based on aviation safety risk assessments and derived information security risk acceptance levels, which are designed to effectively treat and manage information security risks with a potential impact on aviation safety caused by threats exploiting vulnerabilities of information assets in aeronautical systems.
Interacting bow-ties is one possible way that allows for a higher-level and non-exhaustive illustration of how different disciplines of risk assessment may need to collaborate to establish a common risk perspective. The below Figure 1 from ICAO Doc 10204 ‘Manual on Aviation Information Security’ illustrates these interactions.
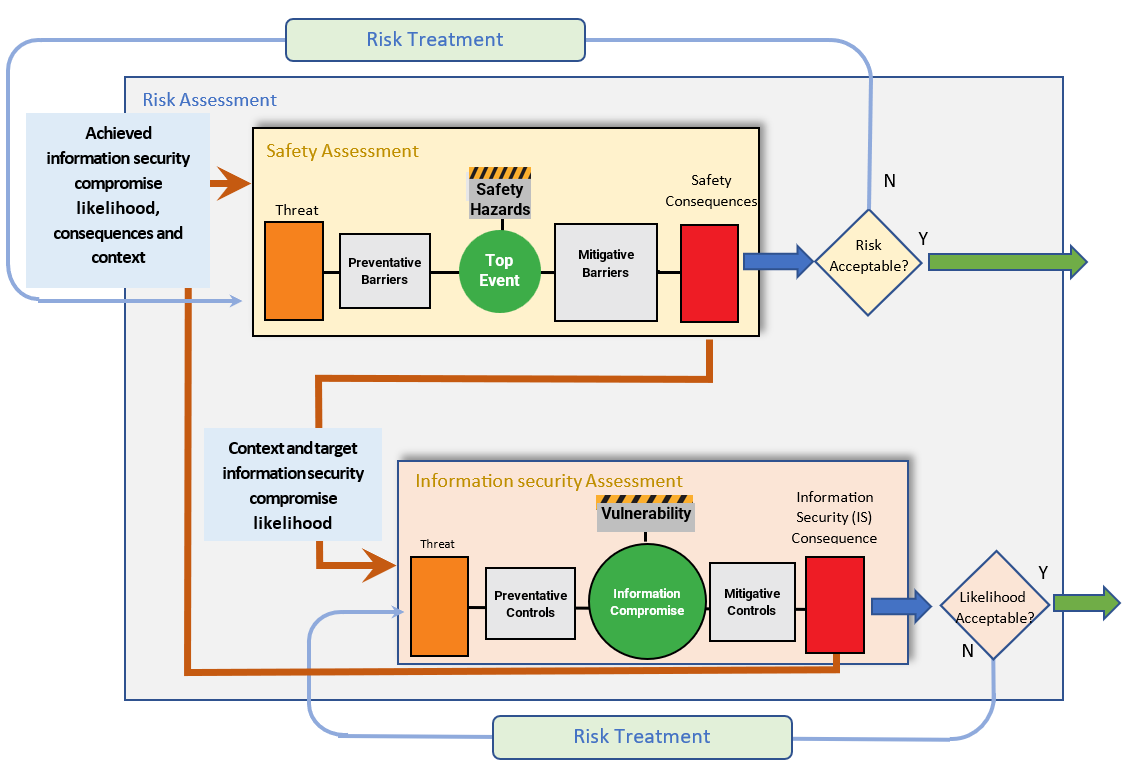
Figure 1: Bow-tie representation of management of aviation safety risks posed by information security threats
In the drawing, the term ‘context’ in the communication between the safety assessment process (SAP) and the information security assessment process (ISAP) carries slightly different notions, which need to be understood and distinguished.
In order to satisfy the safety requirements, the SAP will provide context information such as:
—the architecture of the systems and the functional descriptions of the elements within the scope, including those related to the barriers. Systems should be understood as the dynamic interaction between people, processes, and products or services;
—all identified relevant safety hazards;
—the top events and their relations (e.g. triggers) to those hazards.
In addition to context information, it provides the target likelihood of the related information security successful compromise. This target likelihood is commensurate with the safety objectives related to the severity of the safety consequence. However, it needs to be complemented to include information about the acceptable level of uncertainty, in order to be able to rely adequately on the results of the ISAP.
In turn, the ISAP will return context information such as:
—modification to the architecture of the systems and functional descriptions of the elements modified or added, whether those were safety barriers or other items;
—additional threats;
—potentially additional safety hazards;
—additional direct triggers of hazards;
—additional escalating factors affecting barriers.
In addition to context information, it provides the achieved likelihood of an information security successful compromise. While this likelihood is consistent with the safety objectives set by the SAP, the achieved level of uncertainty also needs to be considered.
The interaction between SAP and ISAP is iterative and continues until the safety risk is acceptable, i.e. the target likelihood of the related information security successful compromise has been achieved. The interaction can start from safety consequences identified through the SAP that fall within the scope of the ISMS risk analysis, or from existing information security assessments.
ISMS implementation and maintenance
An ISMS, as defined in this Regulation, employs the perspectives of governance, risk and compliance, and an approach that combines the safety risk and performance dimensions to determine the information security controls that are appropriate to and compliant with the specific context and can effectively provide the level of protection required to achieve the aviation safety objectives by:
—Governance perspective refers to providing management direction and leadership aimed to achieve the entity’s own overarching objectives:
—leadership and commitment of the senior management defining and ensuring the close involvement of the management and a ‘top-down’ ISMS implementation
—information security and safety objectives aligned and consistent with the entity’s business objectives and monitored by, e.g., management reviews
—information security policies stating the principles and objectives to be achieved
—roles, responsibilities, competencies and resources required for an effective ISMS
—effective, target-group-oriented communication to internal and external stakeholders
—Risk perspective refers to a key aspect of an ISMS in an aviation safety context according to this Regulation, and serves as a basis for transparent decision-making and prioritisation of controls and risk treatment options. It further refers to the assessment, treatment and monitoring of information security risks in support of the management of aviation safety risks for the key processes and information assets upon which they depend. This includes protection requirements, risk exposure, attitude towards risks and risk acceptance criteria, methods and industry standards.
—Compliance perspective refers to the compliance with regulatory, legal and contractual requirements. This includes:
—this Regulation,
—the entity’s own policies and standards and may further include international or industry standards adopted by the entity from ISO, EUROCAE, etc.
This perspective comprises the definition, implementation and maintenance of the required information security provisions whose effectiveness and compliance should be regularly monitored and assured by, e.g., (internal) audits.
Based on these perspectives, we may identify the following processes or subject areas that have been shown to be relevant for the establishment of an effective ISMS. These ISMS processes and subject areas can be summarised as follows:
(a)context establishment defining the scope, interfaces, dependencies and requirements of interested parties;
(b)leadership and commitment of the senior management;
(c)information security and safety objectives;
(d)information security policies;
(e)roles, responsibilities, competencies and resources required for an effective ISMS;
(f)communication to internal and external stakeholders to achieve a sufficient level of information security awareness and training of all involved parties;
(g)information security risk management including risk assessment and treatment;
(h)information security incident management establishing processes for the handling of information security incidents and vulnerabilities;
(i)performance & effectiveness monitoring, measurement and evaluation;
(j)internal audits and management reviews;
(k)corrections and corrective actions;
(l)continuous improvement;
(m)relationship with suppliers;
(n)documentation, record-keeping, and evidence collection.
Additional critical success factors for the implementation and operation of an ISMS include the following:
—The ISMS should be integrated with the entity’s processes and overall management structure or even — at least partially, with safeguards for their respective integrity, and as reasonably applicable — with an overarching management system comprising information security, aviation safety and quality management.
—Information security has to be considered at an early stage in the overall design of processes and procedures, of systems and of information security controls, to be seamlessly integrated, for maximum effectiveness, minimal functional interference and optimised cost. None of these benefits can be achieved by integrating it on later.
—The risk management process determines appropriate characteristics of preventive controls to reach and maintain acceptable risk levels.
—The incident management process ensures that the organisation detects, reacts and responds to information security incidents in a timely manner. This is achieved by defining responsibilities, procedures, scenarios and response plans in advance to ensure a coordinated, targeted and efficient response.
—Continuous monitoring and reassessment are undertaken and improvements are made in response.
The above-mentioned core components are related to the requirements in this Regulation, for which Figure 2 provides a high-level depiction of the aspects that are more prominent in the implementation phase and those that characterise the operational phase, as well as the review and possible improvement, if the functions do not perform as planned.
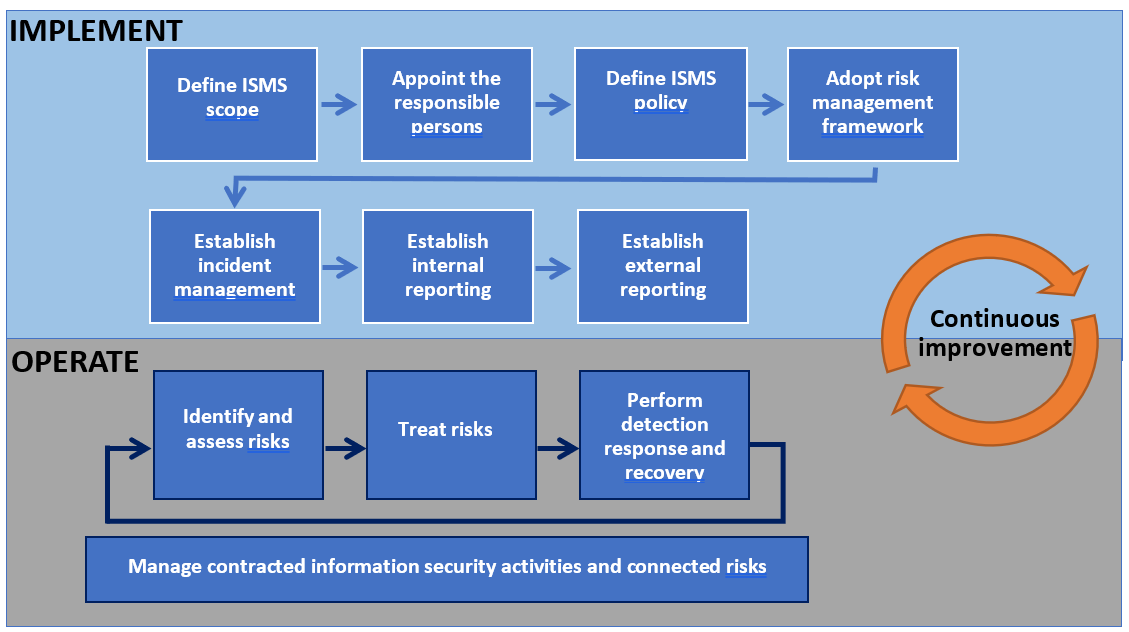
Figure 2: Representation of the Part-IS requirements from an ISMS’s life cycle perspective
Plan-Do-Check-Act approach
The Plan-Do-Check-Act (PDCA) refers to a process approach that is often used to establish, implement, operate, monitor, review and improve management systems. Figure 3 depicts the PDCA applied to an ISMS.
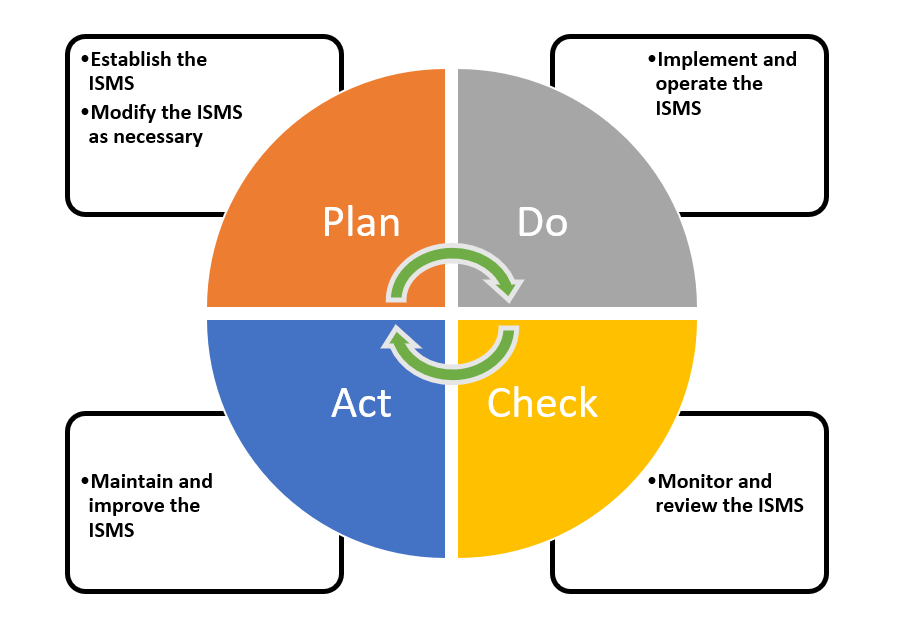
Figure 3: Plan-Do-Check-Act approach applied to an ISMS
Benefits of an ISMS
The benefits of a management system operating in a dynamic, uncertain or unpredictable risk environment are realised in the long term only when the organisation improves existing controls, processes and solutions based on the assessments of risks, performance and maturity as well as on the learnings from incidents, audits, non-conformities and their root causes. A successful adoption and deployment of an ISMS allows an entity to:
—achieve greater assurance to the management and interested parties that its information assets are adequately protected against threats on a continual basis;
—increase its trustworthiness and credibility providing confidence to interested parties that information security risks with an impact on aviation safety are adequately managed;
—increase the resilience of the entity’s key processes against unauthorised electronic interactions and maintains the entity’s ability to decide and act;
—support the timely detection of control gaps, vulnerabilities or deficiencies aimed to prevent information security incidents or at least to minimise their impact;
—detect and timely react to changes in the entity’s environment including system architecture and threat landscape or the adoption of new technologies;
—provide a foundation for effective and efficient implementation of a comprehensive information security strategy in times of digital transformation, increasing interconnectivity of systems, emerging information security threats and new technologies.
Relation to ISO/IEC 27001
The international standard ISO/IEC 27001 is a widely adopted standard for ISMS which specifies generic requirements for establishing, implementing, maintaining and continually improving an ISMS. It also includes requirements for the assessment and treatment of information security risks. The requirements are applicable to all entities, regardless of type, size or nature. The conformity of an ISMS with the ISO/IEC 27001 standard can be certified by an accredited certification body. ISO/IEC 27001 is compatible with other management system standards (quality, safety, etc.) that have also adopted the structure and terms defined in Annex SL to ISO/IEC Directives, Part 1, Consolidated ISO Supplement. This compatibility allows an entity to operate a single management system that meets the requirements of multiple management system standards.
ISO/IEC 27001 allows entities to define their own scope of audit and their own organisational risk appetite. This, in turn, leads to information security requirements that provide the ISMS with criteria for the acceptability of information security risks in line with the entity’s risk appetite (see Figure4).
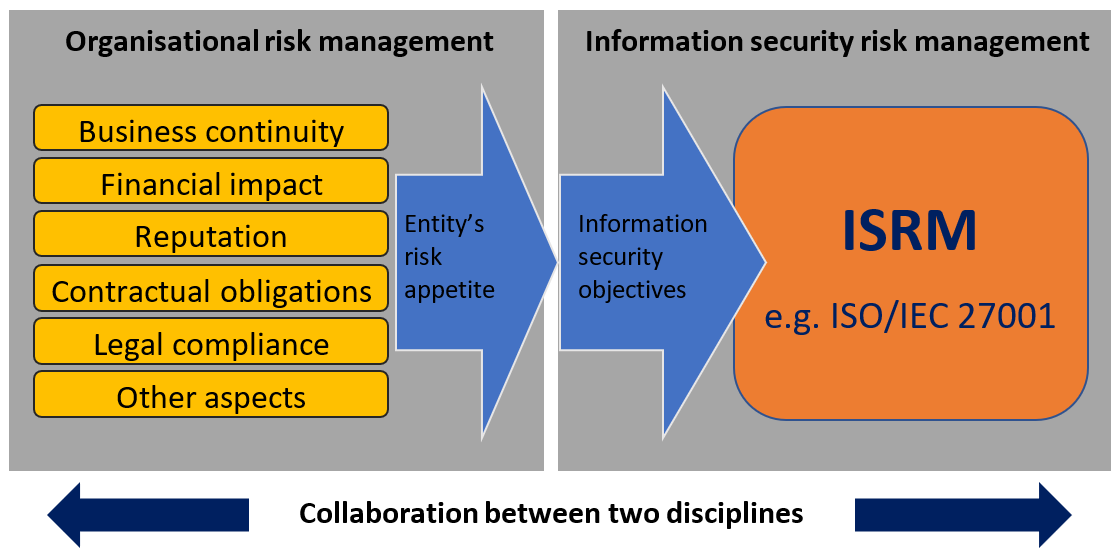
Figure 4: Relation between the entity’s risk appetite and the information security objectives
The requirements for an ISMS specified by this Regulation are in most parts consistent and aligned with ISO/IEC 27001; however, this Regulation introduces provisions specific to the context of aviation safety. If an ISO/IEC 27001-based ISMS is already operated by an entity for a different scope and context, it can be adapted and extended to the scope and context of this Regulation in a straightforward manner based on an analysis of the scope and the gaps. In order to take credit from ISO/IEC 27001 certifications to achieve compliance with Part-IS, aviation safety needs to be included in the organisational risk management, with the relevant risk acceptance level determined by the applicable regulation (see Figure 5). Therefore, careful determination of the scope of the ISMS related to aviation safety risks is needed, as it might differ from the one related to the other organisational risks. To allow demonstration of compliance with Regulation (EU) 2023/203, careful delineation between aspects of the ISMS related to aviation safety risks and other organisational risks may be required. This could have an influence upon the decision to integrate ISMSs.
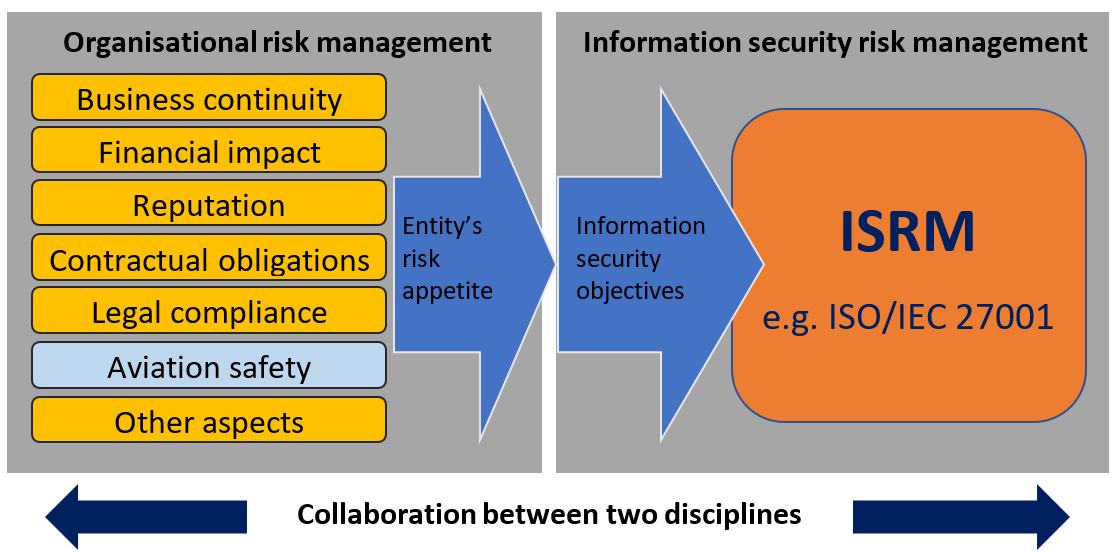
Figure 5: Introduction of aviation safety aspects in the entity’s risk appetite
PART-IS versus ISO/IEC 27001:2022 cross reference table
For a mapping between the Part-IS provisions and the clauses and associated controls in ISO/IEC 27001:2022, refer to Appendix IV.
